Rsa Algorithm Cryptography Computer Network Security One Day One
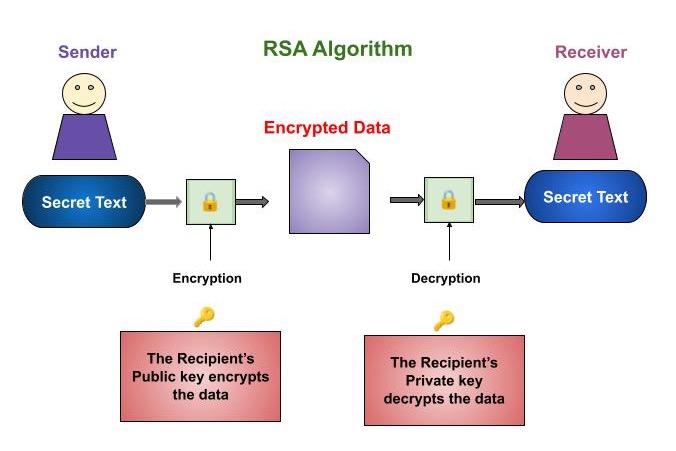
Cryptography Rsa Algorithm Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data. Rsa algorithm how does it work? i'll prove it with an example! cryptography practical tls the rsa encryption algorithm (1 of 2: computing an example).
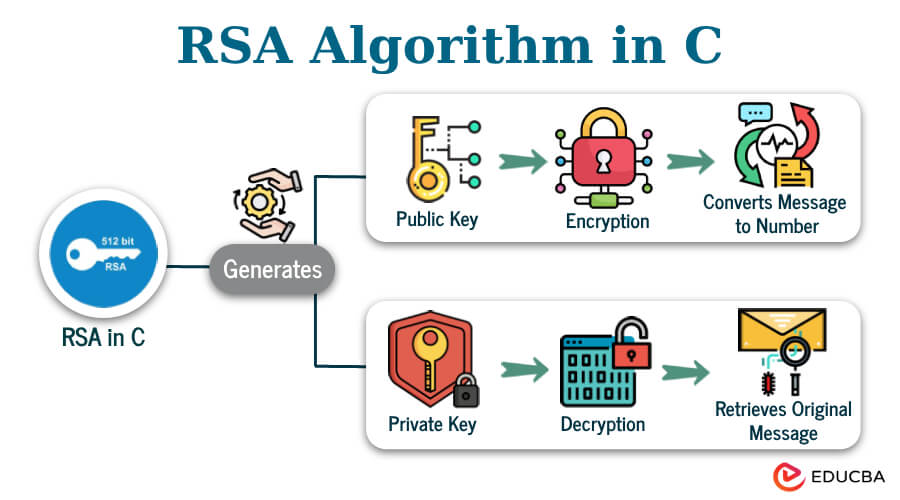
Rsa Algorithm In C Decryption And Mathematical Formula In rsa based cryptography, a user's private key —which can be used to sign messages, or decrypt messages sent to that user—is a pair of large prime numbers chosen at random and kept secret. My immediate goal in this section is to convey to the reader what is meant by cca. as to how rsa is made secure against cca is a story of what goes into the padding bytes that are prepended to the data bytes in order to create a block of bytes that spans the width of the modulus. How does rsa work? rsa is based on the problem of breaking down large numbers into their top factors. to create an rsa key pair, you need to pick very big prime numbers, p and q. it is crucial to pick those primes randomly and ensure they are simply unique from each different. Reverse (decrypt) without the privat key. this is what provides rsa's security. the project walks through the key steps to implement rsa first generating a public and private key pair correctly using number theory, then writing the encryption and d cryption functions using modulo arithmetic. it mentions some ways to improve se.
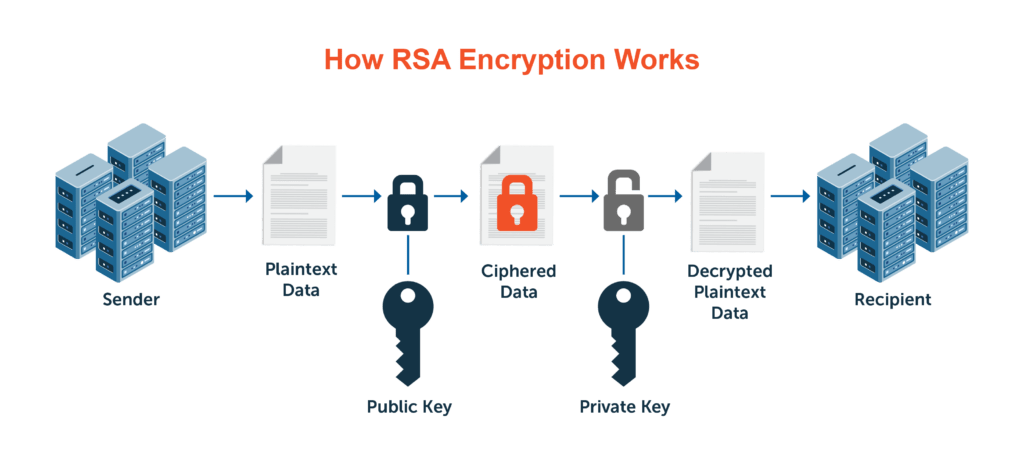
Rsa Algorithm Secure Encryption With Public Key Cryptography Updated How does rsa work? rsa is based on the problem of breaking down large numbers into their top factors. to create an rsa key pair, you need to pick very big prime numbers, p and q. it is crucial to pick those primes randomly and ensure they are simply unique from each different. Reverse (decrypt) without the privat key. this is what provides rsa's security. the project walks through the key steps to implement rsa first generating a public and private key pair correctly using number theory, then writing the encryption and d cryption functions using modulo arithmetic. it mentions some ways to improve se. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Rsa is integral to securing communications over networks, particularly through the ssl and tls protocols. these protocols employ rsa for secure key exchanges, allowing users to establish encrypted connections over the internet, which are critical for safe web browsing and online transactions. Rsa is a public key cryptosystem for data encryption. explore its security features and common use cases, and learn how to mitigate rsa vulnerabilities. These two developments lead to ‘computer security’ and ‘network security’, where the computer security deals with collection of tools designed to protect data and to thwart hackers.

Rsa Algorithm Structure Download Scientific Diagram The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Rsa is integral to securing communications over networks, particularly through the ssl and tls protocols. these protocols employ rsa for secure key exchanges, allowing users to establish encrypted connections over the internet, which are critical for safe web browsing and online transactions. Rsa is a public key cryptosystem for data encryption. explore its security features and common use cases, and learn how to mitigate rsa vulnerabilities. These two developments lead to ‘computer security’ and ‘network security’, where the computer security deals with collection of tools designed to protect data and to thwart hackers.
Comments are closed.