Remote Desktop Protocol Attacks Explained Pdf

Remote Desktop Protocol Attacks Explained Pdf Remote desktop protocol (rdp), a microsoft developed network communications protocol that allows for the remote management of servers, desktops, terminal servers, and applications. A remote code execution vulnerability on windows systems — discovered and kept secret by the nsa — was leaked publicly, and weaponized by hackers months later.
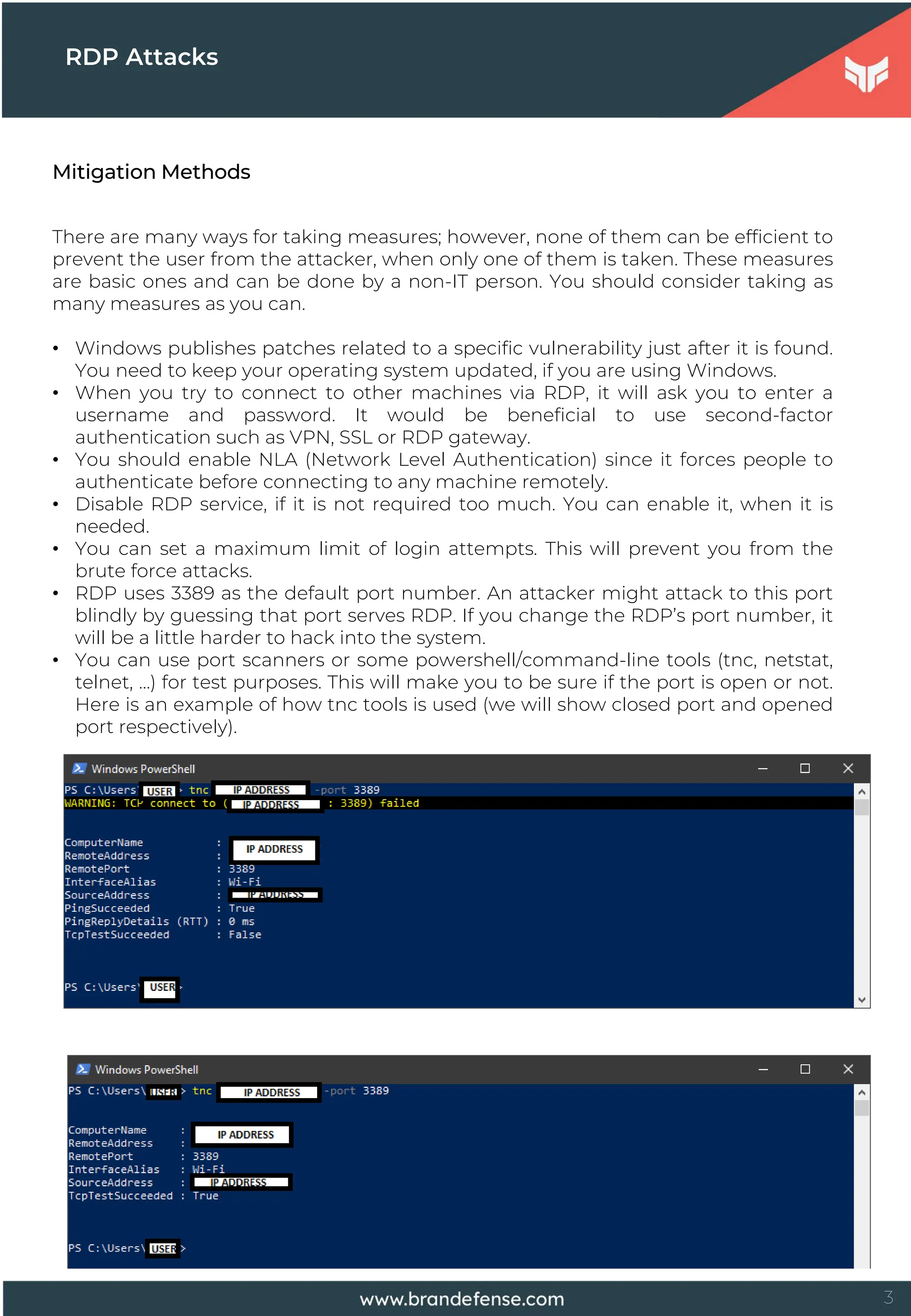
Remote Desktop Protocol Attacks Explained Pdf We developed methods for detecting and characterizing rdp attacks through malicious signatures, windows event log entries, and network traffic metadata. These attacks often leverage exposed rdp ports and weak authentication methods to gain unauthorized access to systems, compromising sensitive data and causing widespread disruption. Rdp vulnerabilities: mitm attacks explained remote desktop protocol (rdp) connections are vulnerable to man in the middle (mitm) attacks even though data is encrypted. By examining current practices and future solutions, this paper provides a comprehensive understanding of the rdp security landscape and the importance of robust protection strategies to safeguard organizational infrastructure against increasingly sophisticated cyber threats.
Remote Desktop Protocol Attacks Explained Pdf Rdp vulnerabilities: mitm attacks explained remote desktop protocol (rdp) connections are vulnerable to man in the middle (mitm) attacks even though data is encrypted. By examining current practices and future solutions, this paper provides a comprehensive understanding of the rdp security landscape and the importance of robust protection strategies to safeguard organizational infrastructure against increasingly sophisticated cyber threats. By our open source attack tool: pyrdp. learn more about it! what is network level authentication (nla)? but the crypto said? nla bypass, legit certificates (lets encrypt), as bad as it can get but how bad is it really? demo! after what we found never use rdp on untrusted networks! blog, blog, blog! attack both!. Protocol (rdp) to access company data are at high risk. between may tacks against networks with public facing rdp services. this was up 1 4% compared to the period from january to sixfold when comparing h1 2020 to h1 2021. Attackers are able to execute commands remotely or even sometimes gain control of the gui of the target machine. attackers are likely to target companies since they have a lot of computers in the same network and they are likely use rdp. Ddos attacks were observed recently, where microsoft remote desktop protocol (rdp) was abused in order to reflect and amplify the amount of bandwidth involved. this is not a vulner ability by itself, but an abuse of the rdp protocol design [1].

Remote Desktop Protocol Attacks Explained Pdf By our open source attack tool: pyrdp. learn more about it! what is network level authentication (nla)? but the crypto said? nla bypass, legit certificates (lets encrypt), as bad as it can get but how bad is it really? demo! after what we found never use rdp on untrusted networks! blog, blog, blog! attack both!. Protocol (rdp) to access company data are at high risk. between may tacks against networks with public facing rdp services. this was up 1 4% compared to the period from january to sixfold when comparing h1 2020 to h1 2021. Attackers are able to execute commands remotely or even sometimes gain control of the gui of the target machine. attackers are likely to target companies since they have a lot of computers in the same network and they are likely use rdp. Ddos attacks were observed recently, where microsoft remote desktop protocol (rdp) was abused in order to reflect and amplify the amount of bandwidth involved. this is not a vulner ability by itself, but an abuse of the rdp protocol design [1].

Remote Desktop Protocol Attacks Explained Pdf Attackers are able to execute commands remotely or even sometimes gain control of the gui of the target machine. attackers are likely to target companies since they have a lot of computers in the same network and they are likely use rdp. Ddos attacks were observed recently, where microsoft remote desktop protocol (rdp) was abused in order to reflect and amplify the amount of bandwidth involved. this is not a vulner ability by itself, but an abuse of the rdp protocol design [1].

Beware Of Remote Desktop Protocol Attacks Advanced Technology Consultants
Comments are closed.