Understanding Remote Desktop Protocol Threats Devolutions

Video Understanding Remote Desktop Protocol Threats Devolutions Blog Many companies don’t clearly understand how the cyber security kill chain works, or the various modus operandi of hackers. the overconfidence in rdp (and other windows services) makes companies vulnerable. Many companies don’t clearly understand how the cyber security kill chain works, or the various modus operandi of hackers. the overconfidence in rdp (and other windows services) makes companies vulnerable.
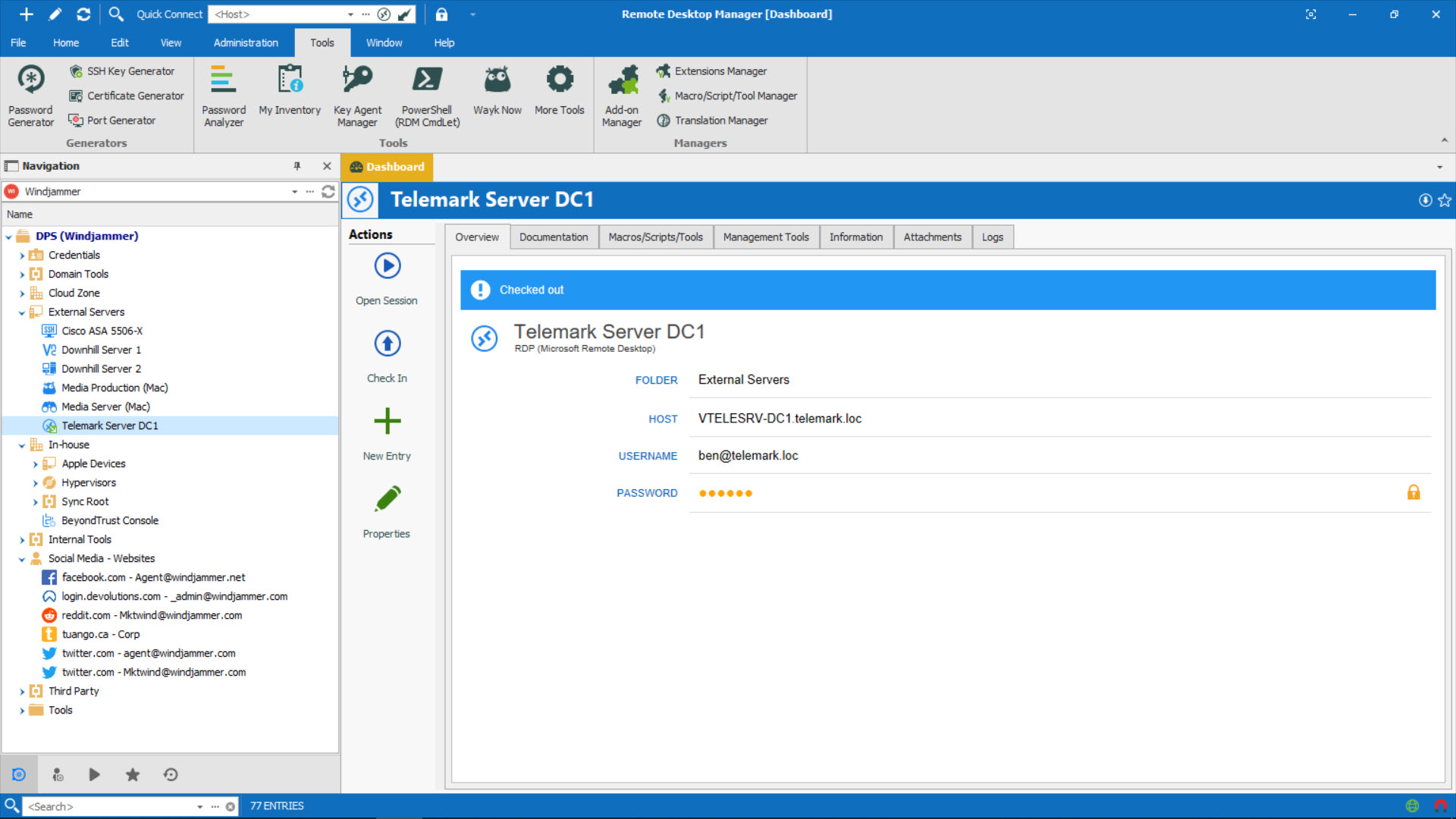
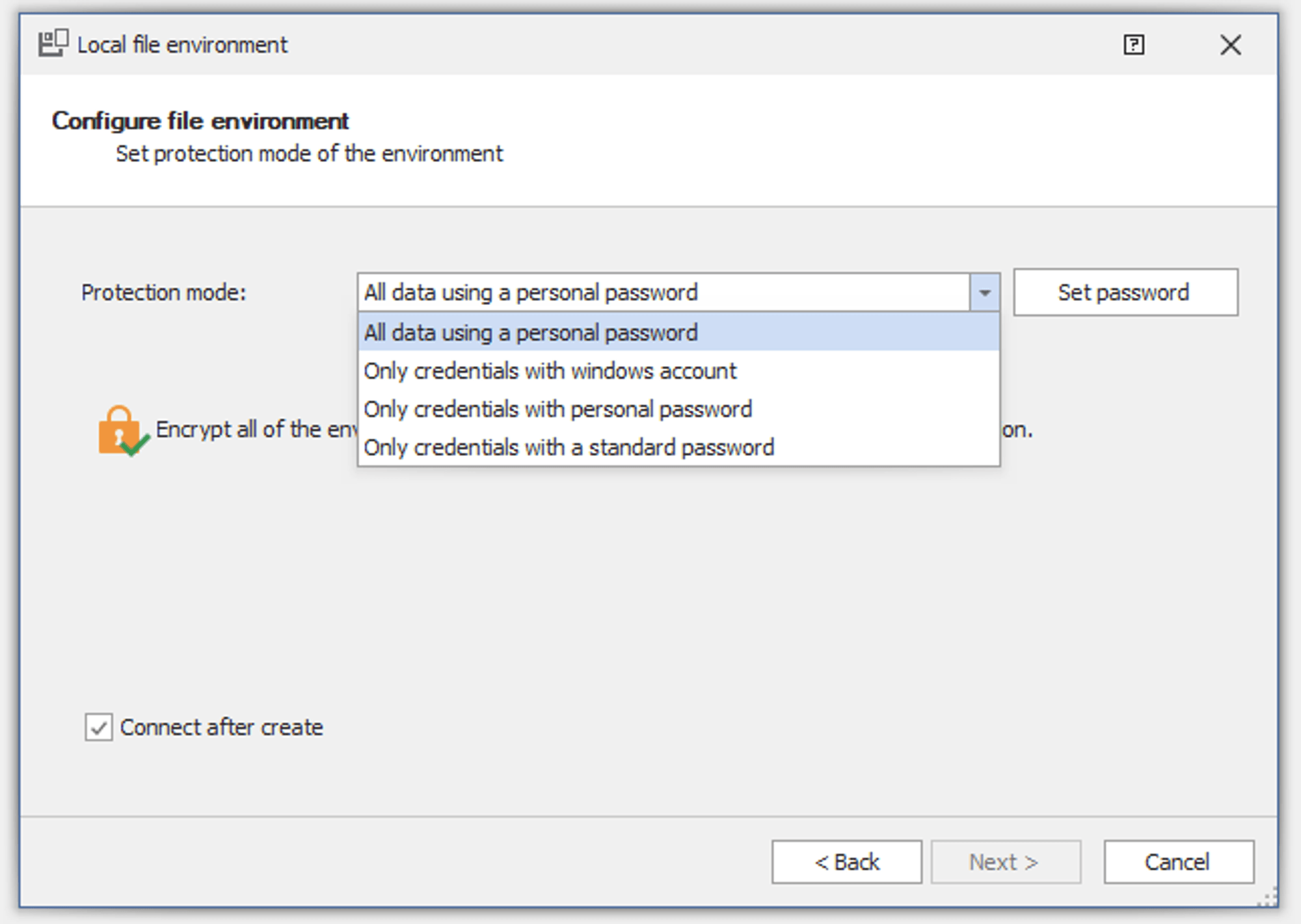
Remote Access And Password Management Devolutions The recently reported hack of labcorp – one of the largest blood testing labs in the u.s. – has raised some legitimate questions about the defense strategies of corporations in an era when cyber attacks can happen at an…. While there are probably many factors that led to the attack, it’s worth focusing on windows remote desktop protocol (rdp). it’s not surprising that the hackers went after rdp. windows services are very attractive as they are bound to an active directory domain for authentication. While there are probably many factors that led to the attack, it’s worth focusing on windows remote desktop protocol (rdp). it’s not surprising that the hackers went after rdp. windows services are very attractive as they are bound to an active directory domain for authentication. Schedule a live demo focused on secure remote desktop: have a product specialist walk your team through workflows such as credential injection, just in time access, approvals, recording and redaction, reporting, and policy templates, which are mapped to your remote desktop use cases.
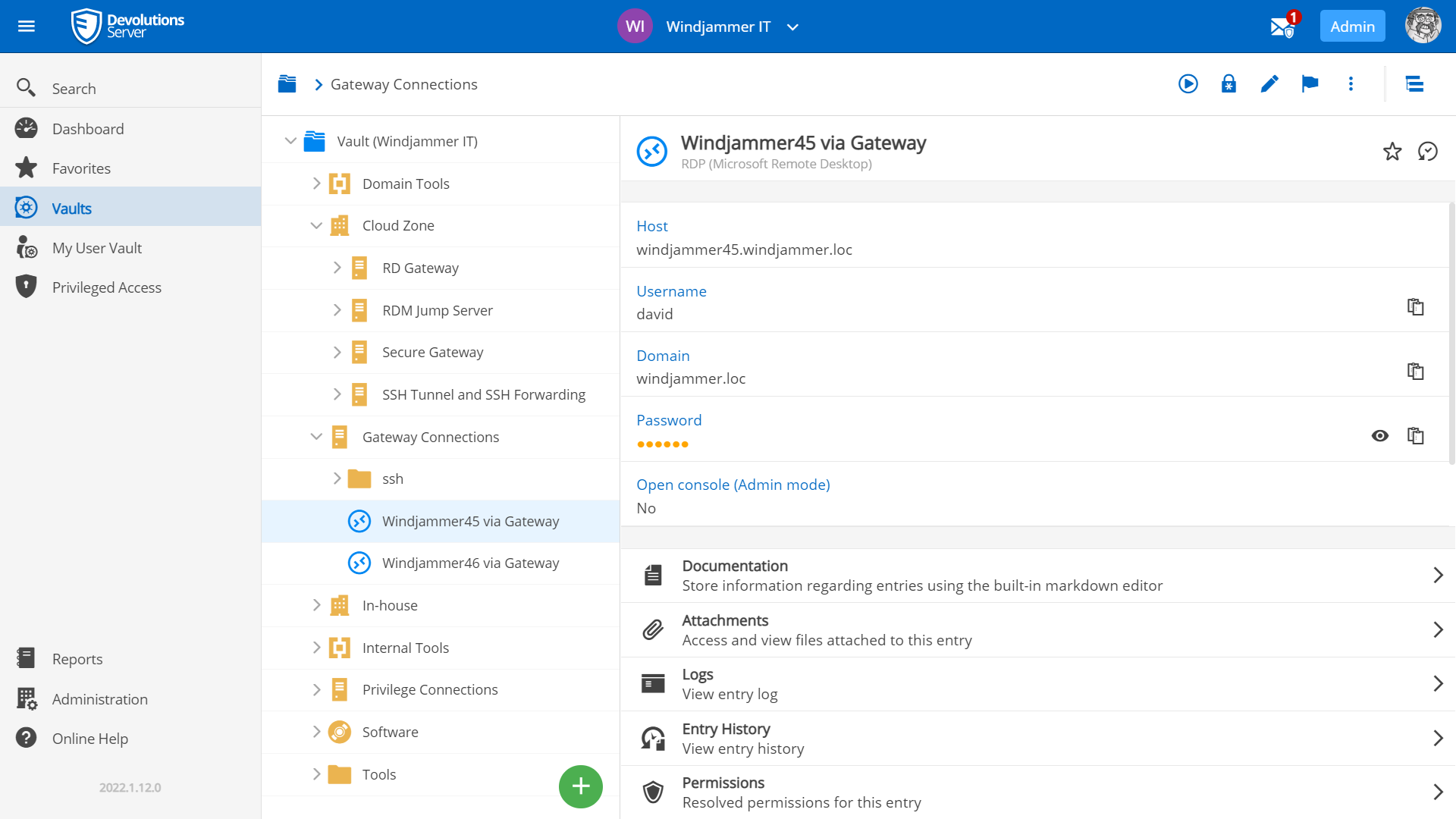
Remote Access And Password Management Devolutions While there are probably many factors that led to the attack, it’s worth focusing on windows remote desktop protocol (rdp). it’s not surprising that the hackers went after rdp. windows services are very attractive as they are bound to an active directory domain for authentication. Schedule a live demo focused on secure remote desktop: have a product specialist walk your team through workflows such as credential injection, just in time access, approvals, recording and redaction, reporting, and policy templates, which are mapped to your remote desktop use cases. 273 subscribers in the devolutions community. a community about devolutions and its products including announcements, news, tips and tricks, case…. A serious vulnerability has been found in microsoft remote desktop client. the vulnerability, which is designated as cve 2025 48817, affects multiple versions of windows and poses significant security risks for organizations that rely on remote desktop protocol (rdp) connections. At its core, cve 2025 24035 highlights a critical security oversight in windows remote desktop services. the vulnerability arises because sensitive data—often including credentials and critical system information—is being stored in memory that hasn’t been securely locked. Devolutions has disclosed critical vulnerabilities in its remote desktop manager (rdm) software, which could allow attackers to intercept and modify encrypted communications through man in the middle (mitm) attacks.

Remote Desktop Manager Free Solo Devolutions 273 subscribers in the devolutions community. a community about devolutions and its products including announcements, news, tips and tricks, case…. A serious vulnerability has been found in microsoft remote desktop client. the vulnerability, which is designated as cve 2025 48817, affects multiple versions of windows and poses significant security risks for organizations that rely on remote desktop protocol (rdp) connections. At its core, cve 2025 24035 highlights a critical security oversight in windows remote desktop services. the vulnerability arises because sensitive data—often including credentials and critical system information—is being stored in memory that hasn’t been securely locked. Devolutions has disclosed critical vulnerabilities in its remote desktop manager (rdm) software, which could allow attackers to intercept and modify encrypted communications through man in the middle (mitm) attacks.

Rdp Management Showdown Rocket Remote Desktop Vs Devolutions Rdm At its core, cve 2025 24035 highlights a critical security oversight in windows remote desktop services. the vulnerability arises because sensitive data—often including credentials and critical system information—is being stored in memory that hasn’t been securely locked. Devolutions has disclosed critical vulnerabilities in its remote desktop manager (rdm) software, which could allow attackers to intercept and modify encrypted communications through man in the middle (mitm) attacks.
Rdp Management Showdown Rocket Remote Desktop Vs Devolutions Rdm
Comments are closed.