Registry Overview Uds

Uds Document Pdf Osi Model Computer Science Uds registry is an oci compliant registry specifically designed for the department of defense (dod) to manage and deploy uds packages to any mission environment. It provides an overview of the integration process, key considerations, and resources to ensure a smooth integration. if you are familiar with uds package creation, uds registry package requirements may be more relevant.

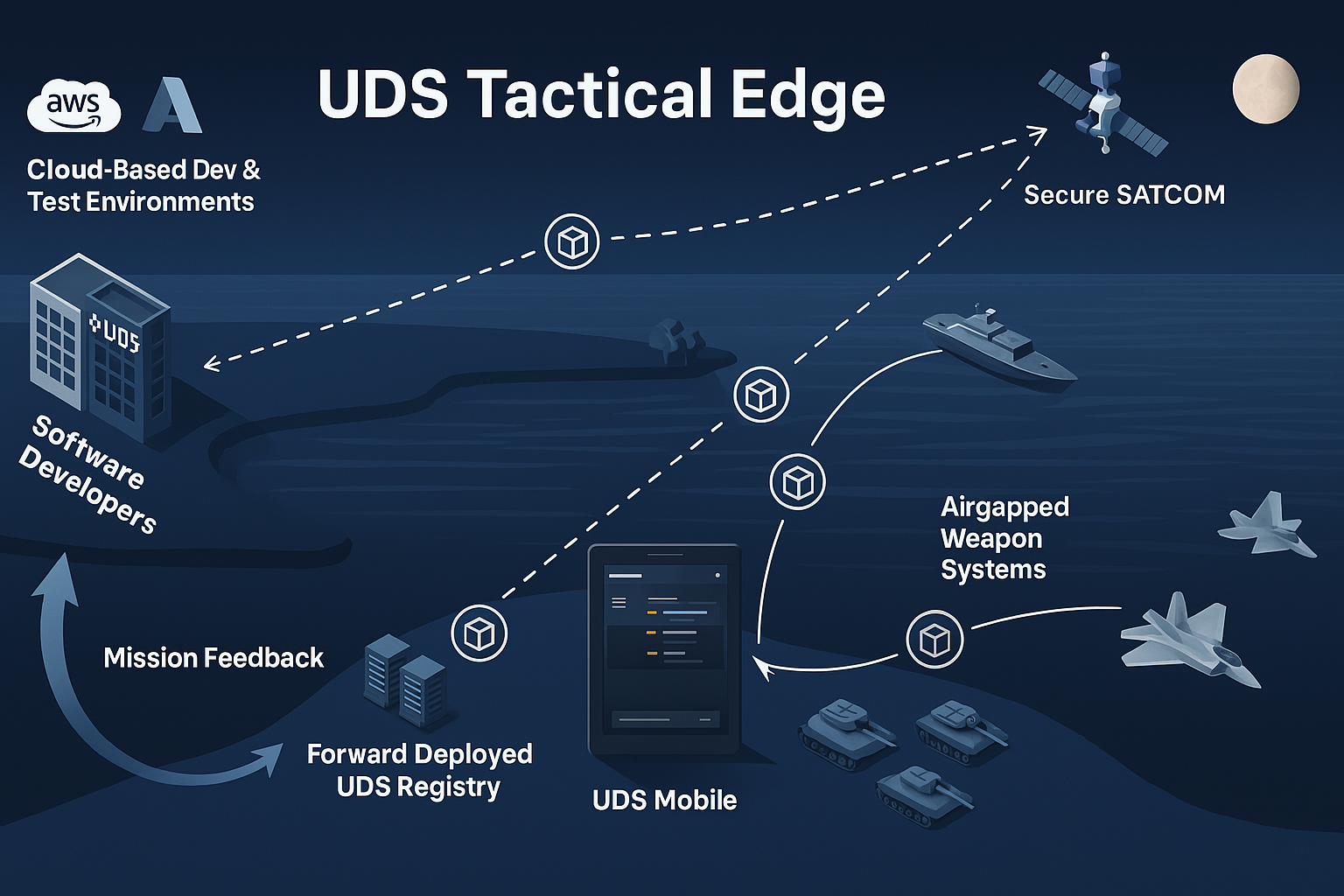
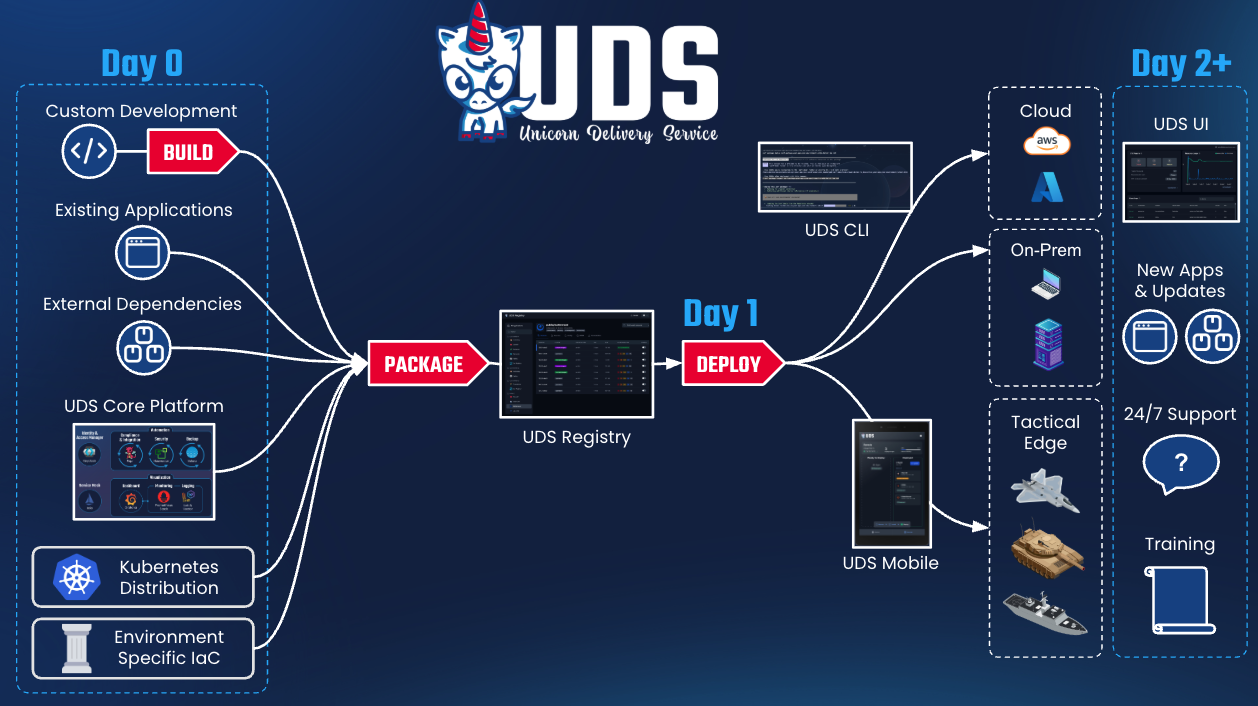
Uds3 Pdf Computing Computer Data Defense unicorns has introduced the uds registry, an air‑gap‑native software repository designed to store, manage, and securely distribute zarf and oci artifacts with the speed, reliability, and performance essential for defense missions in the most extreme environments. Uds registry enables teams across the dod to rapidly discover, access, deploy, and manage software in classified, connected, or fully disconnected environments. Software ready whenever and wherever your mission demands. the first registry purpose built for mission critical environments, securing package delivery from enterprise cloud to tactical edge. Uds registry is the first software registry of its kind to offer the speed, reliability, and mission critical performance required by defense systems operating in the most extreme environments.
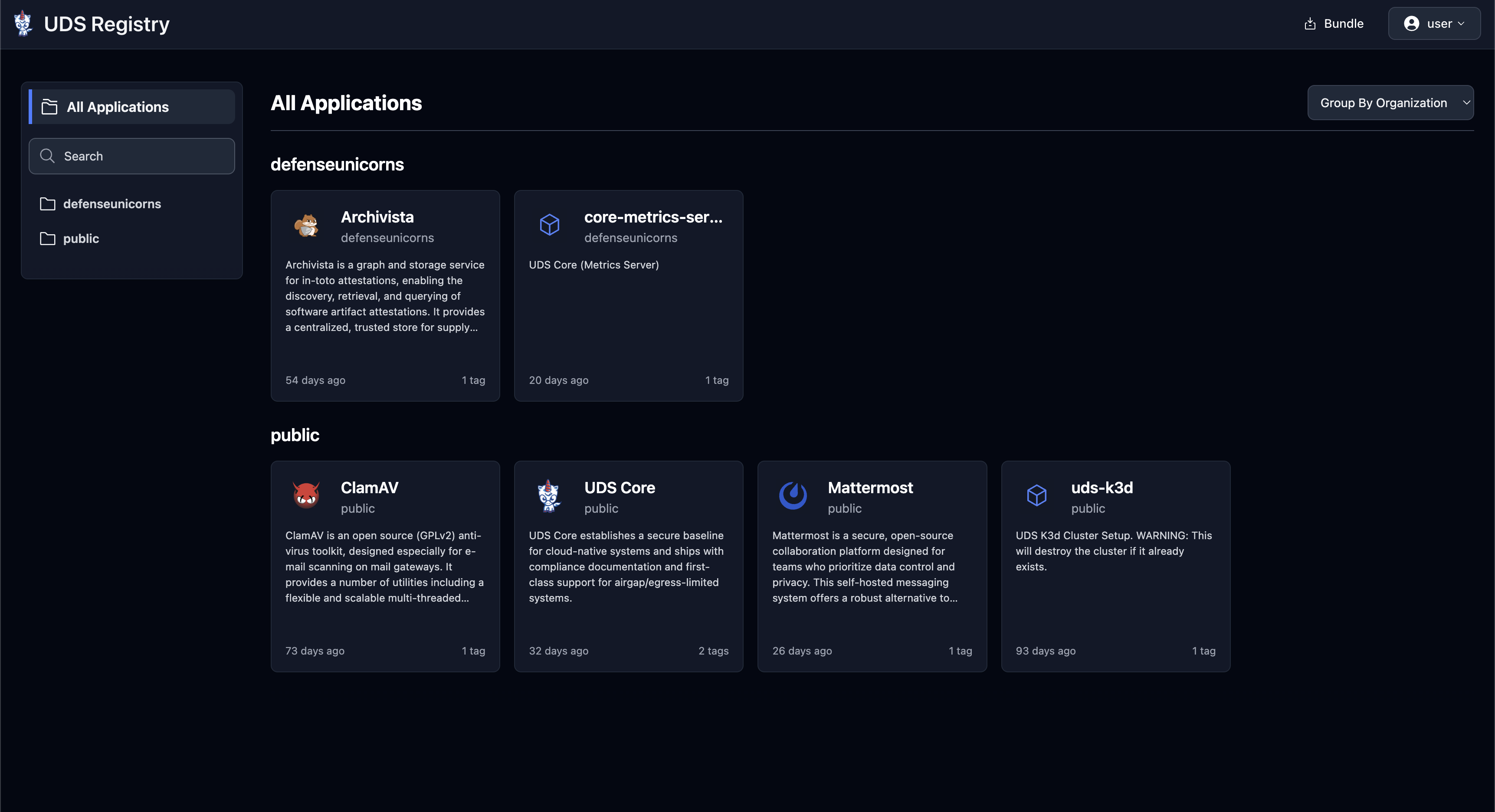
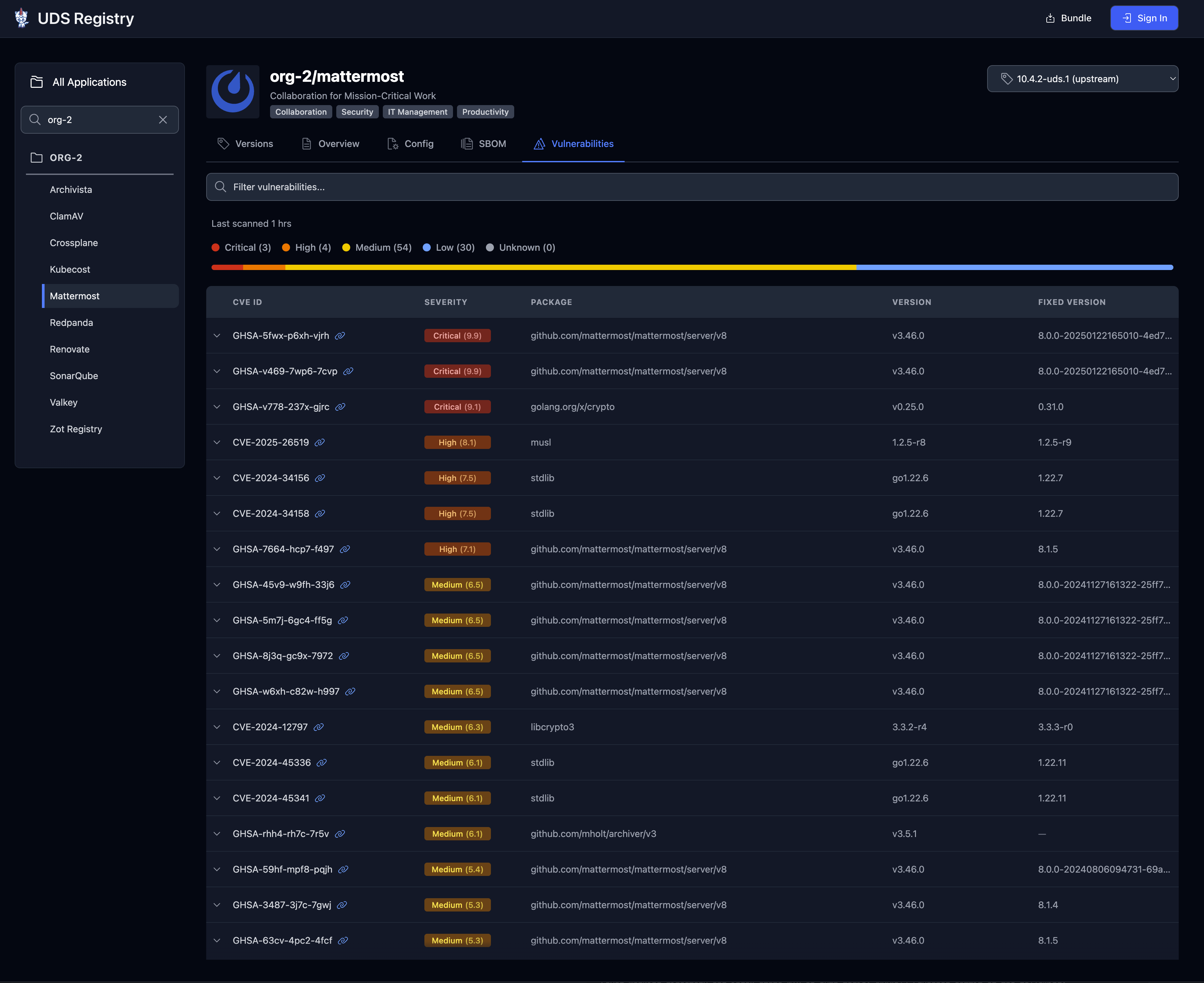
Registry Overview Uds Software ready whenever and wherever your mission demands. the first registry purpose built for mission critical environments, securing package delivery from enterprise cloud to tactical edge. Uds registry is the first software registry of its kind to offer the speed, reliability, and mission critical performance required by defense systems operating in the most extreme environments. Learn more about uds at the tactical edge and the uds registry. docs for llms: machine readable snapshots for assistants and automation. It is the easiest way to explore uds packages and see how the registry works. there are two main organizations to explore, each serving different purposes for package distribution and evaluation. Configuration guide this document provides a comprehensive overview of all configuration options available in the uds registry helm chart. tip uds registry uses sensible defaults, most deployments will need to only require a minimal set of configuration. Uds maintains a defense in depth baseline, providing real security through the entire software delivery process: secure supply chain with cve data and sboms for transparent software composition analysis and security audits.
Registry Overview Uds Learn more about uds at the tactical edge and the uds registry. docs for llms: machine readable snapshots for assistants and automation. It is the easiest way to explore uds packages and see how the registry works. there are two main organizations to explore, each serving different purposes for package distribution and evaluation. Configuration guide this document provides a comprehensive overview of all configuration options available in the uds registry helm chart. tip uds registry uses sensible defaults, most deployments will need to only require a minimal set of configuration. Uds maintains a defense in depth baseline, providing real security through the entire software delivery process: secure supply chain with cve data and sboms for transparent software composition analysis and security audits.
Registry Overview Uds Configuration guide this document provides a comprehensive overview of all configuration options available in the uds registry helm chart. tip uds registry uses sensible defaults, most deployments will need to only require a minimal set of configuration. Uds maintains a defense in depth baseline, providing real security through the entire software delivery process: secure supply chain with cve data and sboms for transparent software composition analysis and security audits.
Registry Overview Uds
Comments are closed.