Refund Api Pdf Key Cryptography Encryption

Refund Api Pdf Key Cryptography Encryption Refund api free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides documentation on the refund api for merchants to initiate refunds of transactions. You can use the aws payment cryptography data plane api to use encryption keys for payment related transaction processing and associated cryptographic operations.
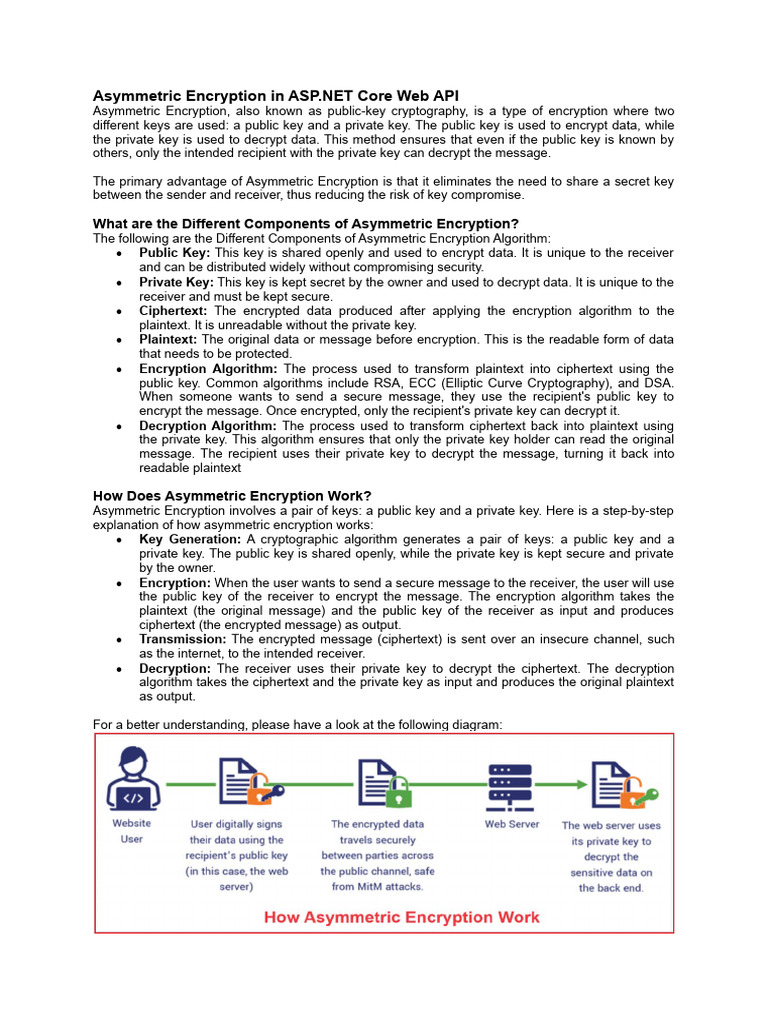
Part 4 Asymmetric Encryption In Asp Net Core Web Api Pdf Key Amount, in the subunit of the supported currency, to be refunded to the customer. amount is optional (defaults to original transaction amount) and cannot be more than the original transaction amount. Here is an example of a use case where a master key is used to generate both a message encryption key and an iv for the encryption, and the derived key and iv are then used to encrypt a message. The key version can be found in the mac key envelope, which is posted to the seller after the agreement has been concluded. the version number is mandatory information. Use case an online marketplace, digital service, or e commerce store wants to refund customers (fully or partially) for cancelled or disputed orders using transactpay.

Part 3 Encryption And Decryption In Asp Net Core Web Api Pdf The key version can be found in the mac key envelope, which is posted to the seller after the agreement has been concluded. the version number is mandatory information. Use case an online marketplace, digital service, or e commerce store wants to refund customers (fully or partially) for cancelled or disputed orders using transactpay. Pdf encryption makes use of rc4 and aes algorithms with different key length. pypdf supports all of them until pdf 2.0, which is the latest pdf standard. pypdf use an extra dependency to do encryption or decryption for aes algorithms. The database stores all data, but sensitive information such as keys and key com ponents are also encrypted under the master key generated by the hsm. keys only exist in clear text inside the hsm. This standard aims to define the detailed cybersecurity requirements related to the cryptography of
Comments are closed.