Raw Rsa Sign And Verify

13 1 Rsa Sign And Verify Using Openssl Pdf Public Key Cryptography Enjoy playing with the above rsa sign verify examples. try to modify the code, e.g. use 4096 bit keys, try to tamper the public key at the signature verification step or the signature. Generate rsa key pairs, sign messages with your private key, and verify signatures with the public key. supports sha256withrsa, rsassa pss, sha512withrsa. run python signature code in your browser. no data stored.

Rsa Signature Pdf Secrecy Cryptography Encryption and signing use the same rsa operations: to verify, messageblock' = rsa (signatureblock, public key). in practice, there are rules to pad the input data before applying the rsa transformation. use the function rsa encodemsg to encode or "pad" the message data you want to encrypt or sign. this uses the rules in [pkcs#1]. This online tool helps you verify signatures using rsa. it supports various curves and signature algorithms. This tool leverages the web crypto api for rsa operations. it allows you to generate rsa key pairs (pem or jwk format), encrypt data using rsa oaep (optimal asymmetric encryption padding), decrypt data, sign messages using rsa pss (probabilistic signature scheme), and verify pss signatures. We discuss the core rsa primitives for sign and verify. note: the raw rsa sign and verify primitives should not be used directly .more.
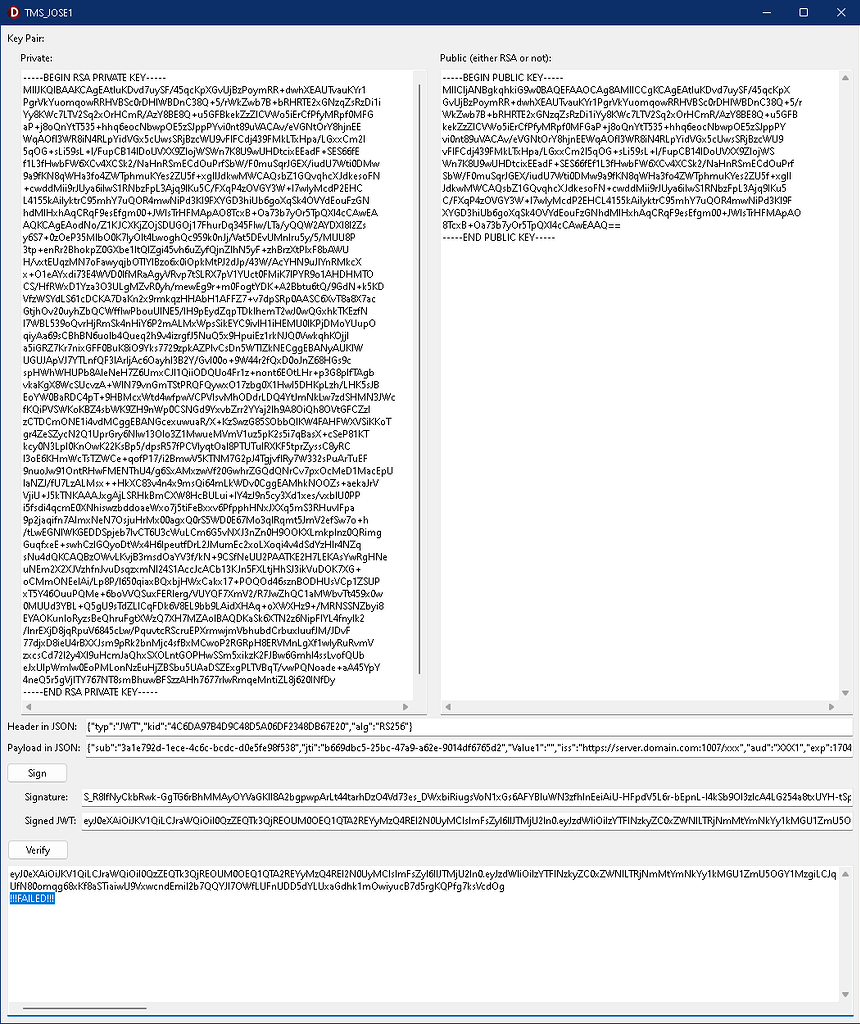
Rsa Sign Verify Jwt Fails Tms Cryptography Pack Tms Support Center This tool leverages the web crypto api for rsa operations. it allows you to generate rsa key pairs (pem or jwk format), encrypt data using rsa oaep (optimal asymmetric encryption padding), decrypt data, sign messages using rsa pss (probabilistic signature scheme), and verify pss signatures. We discuss the core rsa primitives for sign and verify. note: the raw rsa sign and verify primitives should not be used directly .more. Enjoy playing with the above rsa sign verify examples. try to modify the code, e.g. use 4096 bit keys, try to tamper the public key at the signature verification step or the signature. In doing so i have developed a method to test and verify rsa signatures. this example uses rsa512 along with sha1 for simplicity but can be altered to support better hashing or higher bit rsa keys. After the keys are generated, we shall compute rsa digital signatures and verify signatures by a simple modular exponentiation (by encrypting and decrypting the message hash). Performing low level operations using crypto 's rsa primitives can be useful at times, so this page will demonstrate performing rsa encryption, decryption and signing using the low level primitives.
Rsa Sign Verify Examples Practical Cryptography For Developers Enjoy playing with the above rsa sign verify examples. try to modify the code, e.g. use 4096 bit keys, try to tamper the public key at the signature verification step or the signature. In doing so i have developed a method to test and verify rsa signatures. this example uses rsa512 along with sha1 for simplicity but can be altered to support better hashing or higher bit rsa keys. After the keys are generated, we shall compute rsa digital signatures and verify signatures by a simple modular exponentiation (by encrypting and decrypting the message hash). Performing low level operations using crypto 's rsa primitives can be useful at times, so this page will demonstrate performing rsa encryption, decryption and signing using the low level primitives.
Rsa Sign Verify Examples Practical Cryptography For Developers After the keys are generated, we shall compute rsa digital signatures and verify signatures by a simple modular exponentiation (by encrypting and decrypting the message hash). Performing low level operations using crypto 's rsa primitives can be useful at times, so this page will demonstrate performing rsa encryption, decryption and signing using the low level primitives.
Comments are closed.