Quantum Computing And Its Potential Impact On Cybersecurity

The Impact Of Quantum Computing On Cybersecurity Pdf Quantum This systematic review examines the transformative impact of quantum computing (qc) on cybersecurity by analysing peer reviewed literature published between 2019 and 2024. This paper presents a comprehensive review of emerging quantum related cybersecurity threats and explores defense mechanisms designed to mitigate these risks.

Quantum Computing And Its Potential Impact On Cybersecurity In table 1, we present a comprehensive overview of the impact of quantum computing on various aspects of cybersecurity, highlighting unique risks and opportunities, proposed mitigations, and open research questions. Unlike regular computers, quantum computers can process huge amounts of data at incredible speeds, offering possibilities for breakthroughs in fields like medicine, energy, finance, artificial intelligence, and cybersecurity. What are the risks of quantum computing in cybersecurity? quantum computing can expose encrypted data, compromise authentication mechanisms, and disrupt digital identities. This section comprehensively reviews the advancements in quantum computing, the evolution of post quantum cryp tography (pqc), and their cumulative impact on digital in frastructure and cybersecurity.
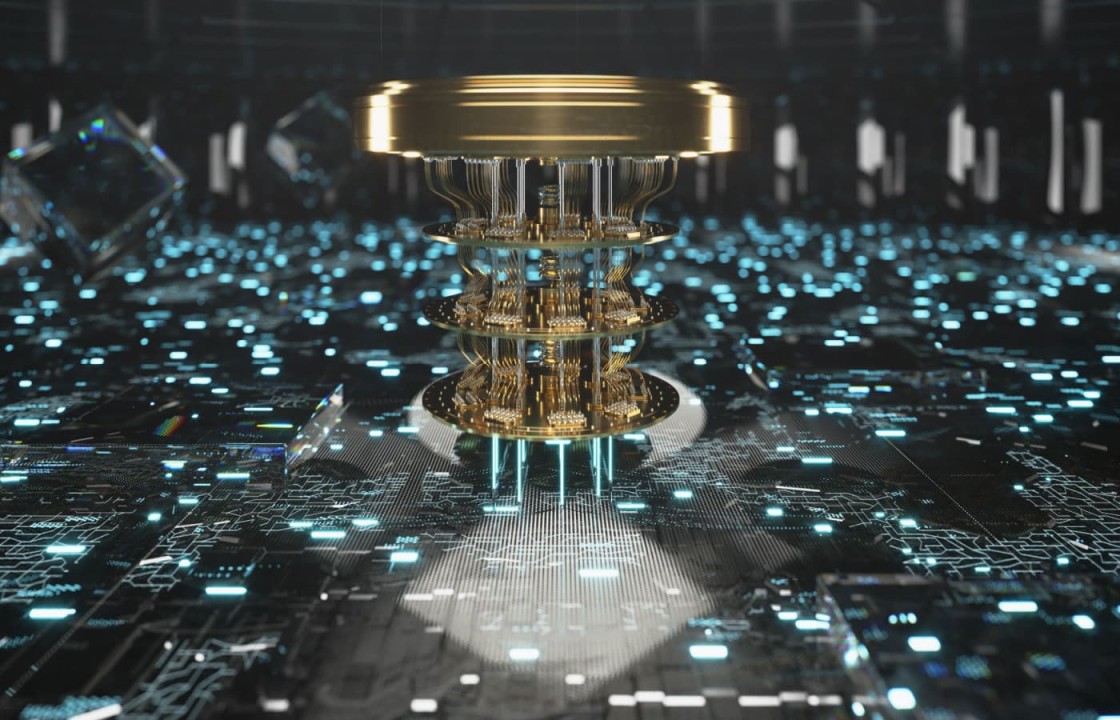
Quantum Computing And Its Impact On Ai Unlocking Limitless Potential What are the risks of quantum computing in cybersecurity? quantum computing can expose encrypted data, compromise authentication mechanisms, and disrupt digital identities. This section comprehensively reviews the advancements in quantum computing, the evolution of post quantum cryp tography (pqc), and their cumulative impact on digital in frastructure and cybersecurity. Quantum computers are likely to pose a severe threat to today’s encryption practices. updating encryption has never been more urgent. the main quantum risk is that future quantum computers will break today’s encryption, exposing digital signatures, secure logins, and sensitive data. Sometime around 2035 quantum computers are expected to become sufficiently powerful to compromise current widely used cryptographic standards, the foundation for online security. fortunately, there is a clear path for the transition to post quantum cryptography. Explore how quantum computing is transforming cybersecurity—its threats to current encryption and the rise of post quantum cryptography for future protection. While quantum computing may seem like a futuristic science fiction concept, the technology is indeed poised to exert major consequences across today’s cybersecurity capabilities.

Quantum Computing And Its Potential Impact On Cyber Security Quantum computers are likely to pose a severe threat to today’s encryption practices. updating encryption has never been more urgent. the main quantum risk is that future quantum computers will break today’s encryption, exposing digital signatures, secure logins, and sensitive data. Sometime around 2035 quantum computers are expected to become sufficiently powerful to compromise current widely used cryptographic standards, the foundation for online security. fortunately, there is a clear path for the transition to post quantum cryptography. Explore how quantum computing is transforming cybersecurity—its threats to current encryption and the rise of post quantum cryptography for future protection. While quantum computing may seem like a futuristic science fiction concept, the technology is indeed poised to exert major consequences across today’s cybersecurity capabilities.
Comments are closed.