Protecting Sensitive Data In A Borderless World
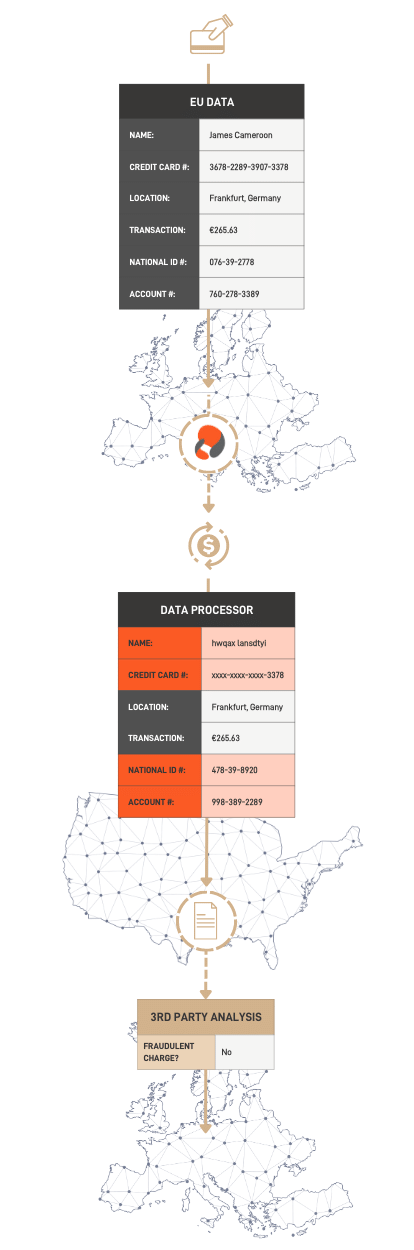
Global Business With Borderless Data邃 Protegrity By protecting sensitive data at a granular level and separating it from non sensitive data, exate allows organisations to meet data residency, localisation, and sovereignty requirements without limiting global operations. Learn how to secure data in today’s borderless world with discovery, classification, tokenization, and automated enforcement—stay compliant with gdpr & ccpa.

Protecting Sensitive Data In A Networked World Fortune Media Unlock the power of borderless data with our data protection strategies. learn how to safeguard your sensitive information across borders and thrive in a connected world. Google cloud vows to sovereignty with its data boundary. it ensures restricting data processing to the eu or u.s. and uses client side encryption to prevent unauthorized access, even by google itself. its user data shield provides continuous security testing to validate sovereignty postures. Our platform frees businesses from the constraints typically associated with accessing and protecting sensitive data, so they can create better customer experiences, make intelligent decisions, and fuel innovation. At platview technologies, we help businesses strengthen identity protection from the ground up through intelligent monitoring, early threat detection, breach exposure analysis, and digital identity defense strategies that stay ahead of evolving attacks.

Protecting The Global Supply Chain With Borderless Data Our platform frees businesses from the constraints typically associated with accessing and protecting sensitive data, so they can create better customer experiences, make intelligent decisions, and fuel innovation. At platview technologies, we help businesses strengthen identity protection from the ground up through intelligent monitoring, early threat detection, breach exposure analysis, and digital identity defense strategies that stay ahead of evolving attacks. As global ai and cloud systems process petabytes of sensitive data per day, the world faces an urgent question: how can we guarantee data sovereignty, trust, and compliance in a borderless digital economy?. Use of pets to enable the processing of sensitive or confidential data securely within less trustworthy digital environments. how to benchmark the effectiveness of pets across use cases. Data sovereignty means a business must ensure its data handling practices – collection, storage, processing, distribution, and security – comply with the specific data privacy regulations and guidelines of the host country for data originating there. In our digitally connected world, data rarely stays confined within national boundaries. this reality creates a fundamental challenge: how do we protect individual privacy rights when data moves across jurisdictions with different legal systems and protection standards?.

The Role Of Ai In Protecting Sensitive Data As global ai and cloud systems process petabytes of sensitive data per day, the world faces an urgent question: how can we guarantee data sovereignty, trust, and compliance in a borderless digital economy?. Use of pets to enable the processing of sensitive or confidential data securely within less trustworthy digital environments. how to benchmark the effectiveness of pets across use cases. Data sovereignty means a business must ensure its data handling practices – collection, storage, processing, distribution, and security – comply with the specific data privacy regulations and guidelines of the host country for data originating there. In our digitally connected world, data rarely stays confined within national boundaries. this reality creates a fundamental challenge: how do we protect individual privacy rights when data moves across jurisdictions with different legal systems and protection standards?.
Protecting Sensitive Data Online And Offline Eclipse Consulting Data sovereignty means a business must ensure its data handling practices – collection, storage, processing, distribution, and security – comply with the specific data privacy regulations and guidelines of the host country for data originating there. In our digitally connected world, data rarely stays confined within national boundaries. this reality creates a fundamental challenge: how do we protect individual privacy rights when data moves across jurisdictions with different legal systems and protection standards?.

Protecting Sensitive Data Across Borders The Eor Advantage Crs
Comments are closed.