Practical Malware Analysis Ida Pro Tutorial Chapter 5 Lab 5
Practical Malware Analysis Ch 5 Ida Pro Pptx In this video, you will be shown the solutions to chapter 5 lab 5 from practical malware analysis. it serves as an ida pro tutorial and goes through many of the features. Solutions for lab 5 within practical malware analysis. ida pro, an interactive disassembler, is a disassembler for computer programs that generates assembly language source code from.

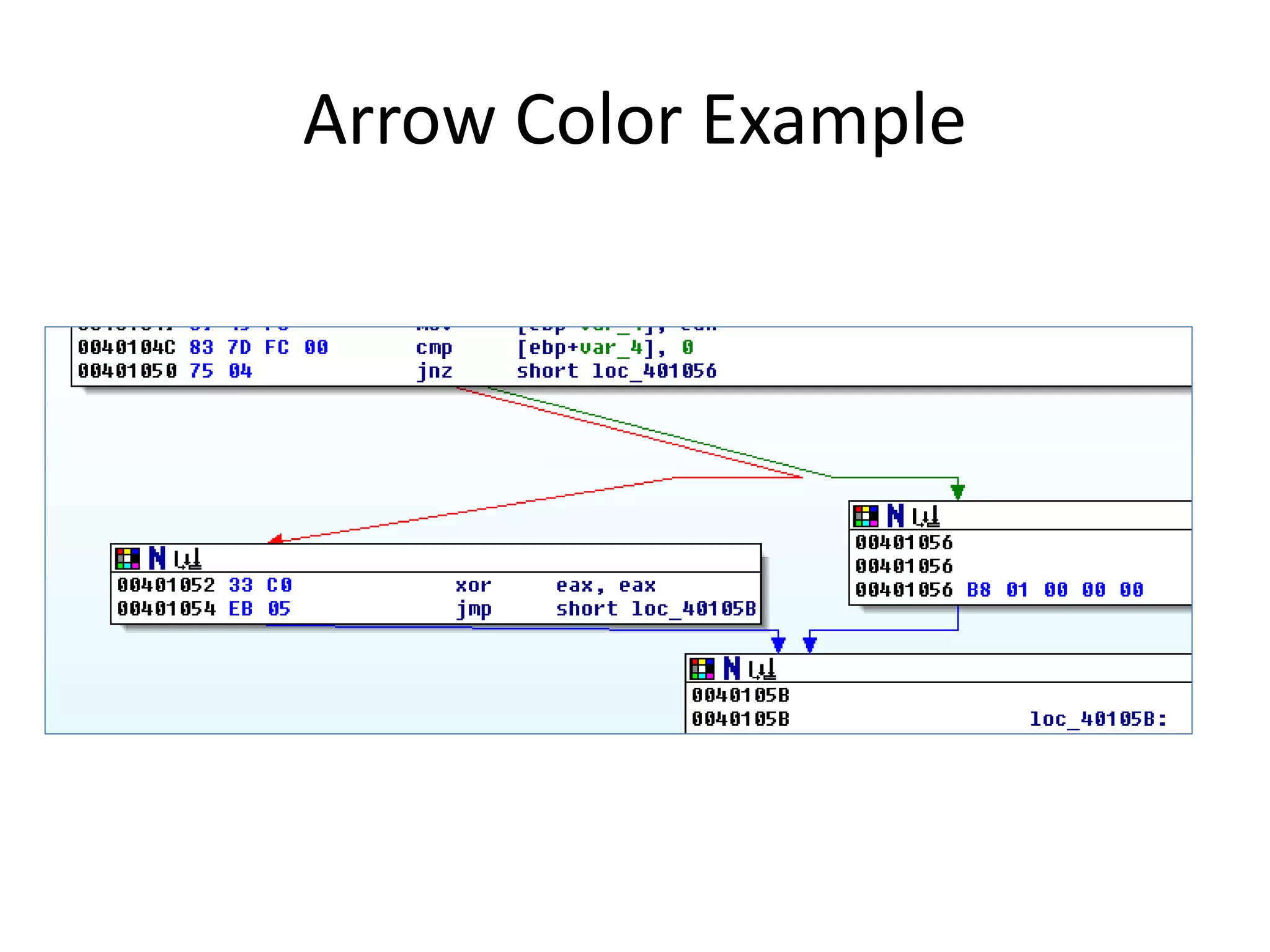
Practical Malware Analysis Ch 5 Ida Pro Pptx The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. This details reverse engineering activities and answers for labs contained in the book ‘practical malware analysis’ by michael sikorski and andrew honig, which is published by no starch press. The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Pslist first calls a procedure which checks dwplatformid and dwmajorversion, as seen in the figure below. the procedure returns 1 if dwplatformid == 2 and dwmajorversion == 5, else it returns 0.
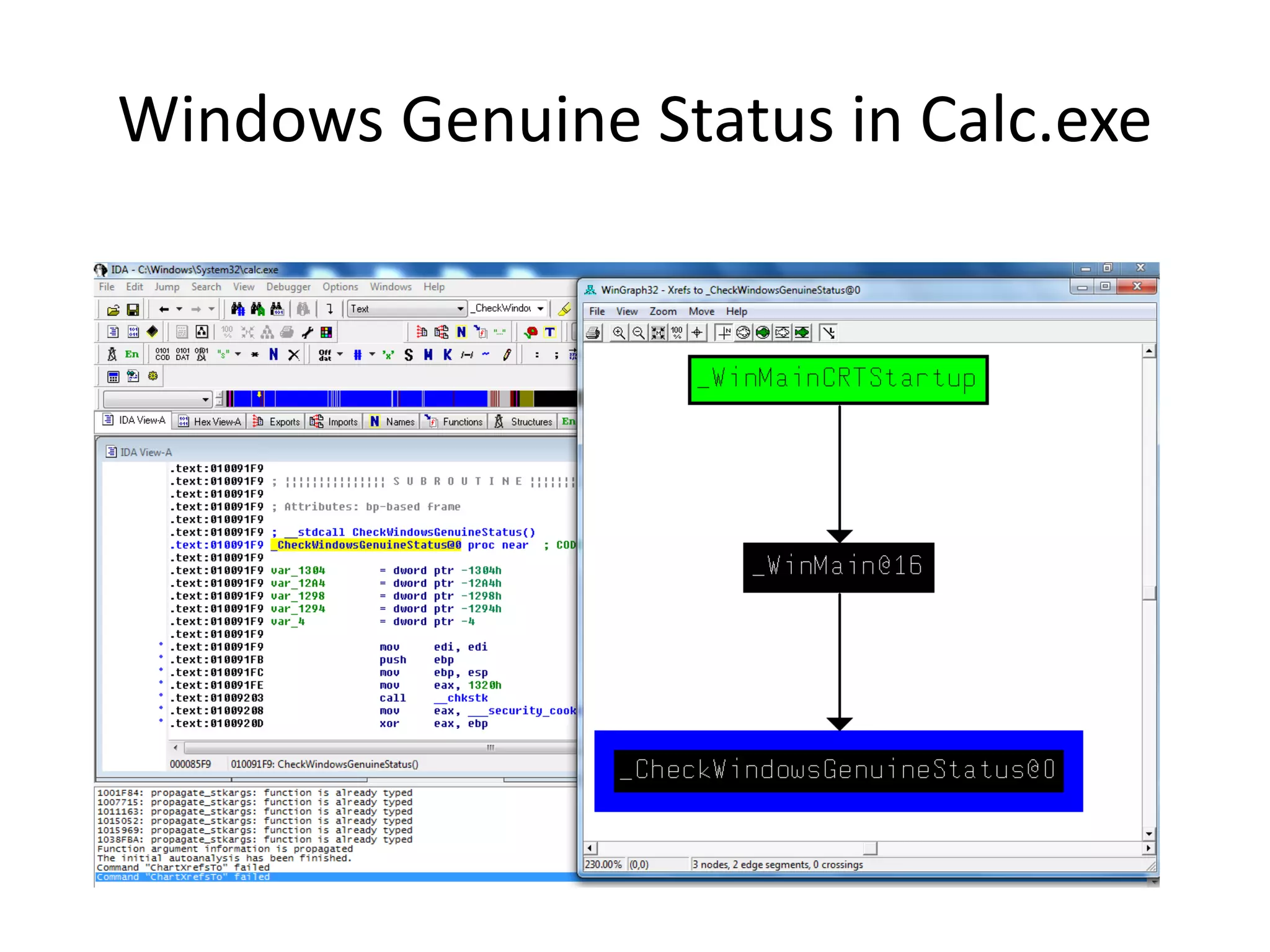
Practical Malware Analysis Ch 5 Ida Pro Pptx The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Pslist first calls a procedure which checks dwplatformid and dwmajorversion, as seen in the figure below. the procedure returns 1 if dwplatformid == 2 and dwmajorversion == 5, else it returns 0. My analysis of the disassembly labs in chapter 5 of "practical malware analysis". Lab 5 lab 5 focuses on using ida pro for malware analysis, requiring a windows machine and the textbook 'practical malware analysis'. participants will download lab files and ida pro, then follow specific instructions to analyze a dll file through various tasks, including finding function addresses and understanding code purpose. Third practical exercice of the practical malware analysis book. the goal of this lab is to give hands on experience with ida pro. Lab 5–1 this lab analyses the malware found in the file lab05–01.dll, and is a longer lab designed to demonstrate features of ida pro and give hands on experience.
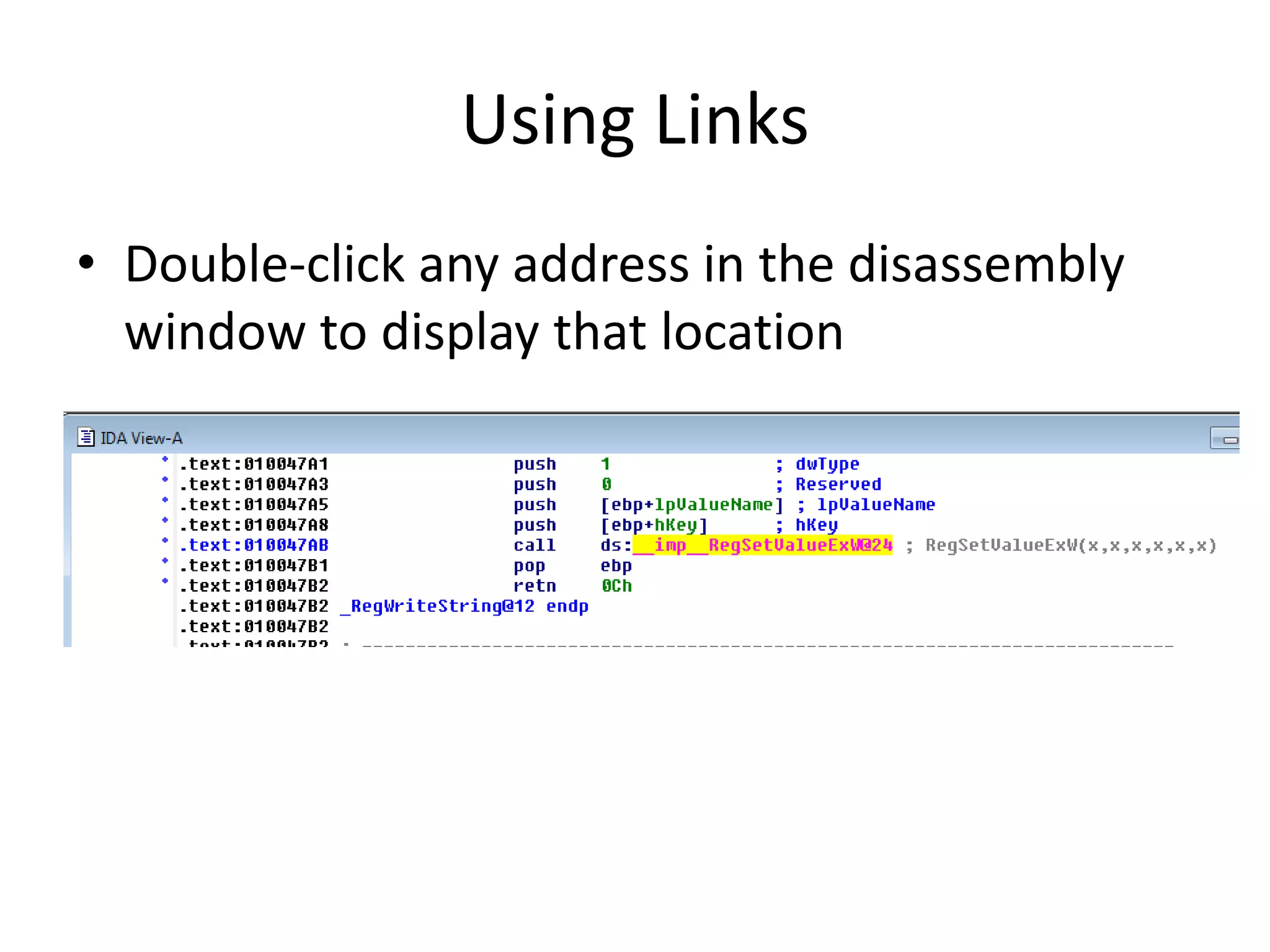
Practical Malware Analysis Ch 5 Ida Pro Pptx My analysis of the disassembly labs in chapter 5 of "practical malware analysis". Lab 5 lab 5 focuses on using ida pro for malware analysis, requiring a windows machine and the textbook 'practical malware analysis'. participants will download lab files and ida pro, then follow specific instructions to analyze a dll file through various tasks, including finding function addresses and understanding code purpose. Third practical exercice of the practical malware analysis book. the goal of this lab is to give hands on experience with ida pro. Lab 5–1 this lab analyses the malware found in the file lab05–01.dll, and is a longer lab designed to demonstrate features of ida pro and give hands on experience.
Comments are closed.