Practical Encryption Pdf

Encryption Pdf 2 Download Free Pdf Cryptography Key Cryptography So far in this book we’ve only talked about encryption and authentication with shared secret keys. but where do we get those shared secret keys from? if you have 10 friends you want to communicate with, you can meet them all and exchange a secret key with each of these friends for future use. Some useful books related to cybersecurity, linux and more. cybersec books practical cryptography in python.pdf at main · 0x00ctrl cybersec books.

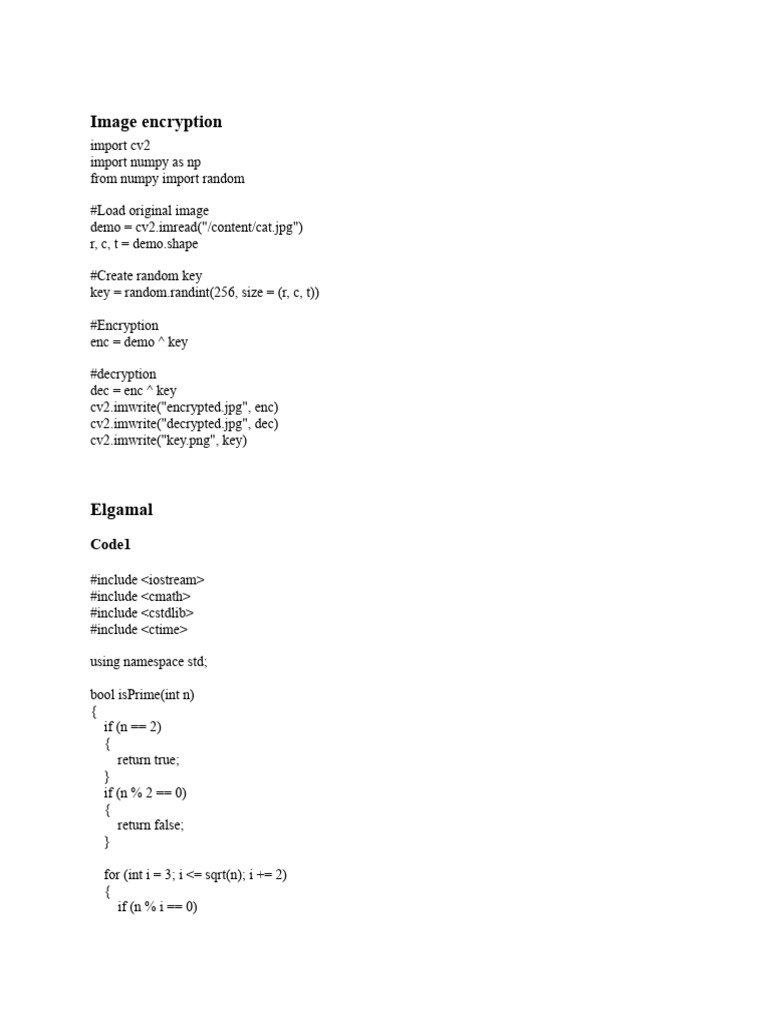
L3 Classical Encryption Techniques Pdf Cryptography Cryptanalysis Rngs slowly produce true random bits from analog sources, in a nondeterministic way, and with no guarantee of high entropy. prngs produce random looking bits quickly from digital sources, in a deterministic way, and with maximum entropy. Cns practical file free download as word doc (.doc .docx), pdf file (.pdf), text file (.txt) or read online for free. the document lists 10 experiments related to cryptography and cybersecurity. experiment 1 implements block cipher and play fair cipher encryption algorithms. The attack models and security goals for asymmetric encryption are about the same as for symmetric encryption, except that because the encryption key is public, any attacker can make encryption queries by using the public key to encrypt. This article presents the basic differences between the fundamental types of cryptography as well as practical examples of encrypting information using various cipher systems, which will help.

Practicalencryption Our design philosophy the context of cryptography introduction to cryptography block ciphers block cipher modes hash functions message authentication codes the secure channel implementation issues (i) generating randomness primes diffie hellman rsa introduction to cryptographic protocols key negotiation. Once it is completed, i will publish it as pdf and epub. be patient. This article presents the basic differences between the fundamental types of cryptography as well as practical examples of encrypting information using various cipher systems, which will help to understand them. It describes dozens of cryptography algorithms, gives practical advice on how to implement them into cryptographic software, and shows how they can be used to solve security problems.
Practical Exam Pdf Encryption Cryptography This article presents the basic differences between the fundamental types of cryptography as well as practical examples of encrypting information using various cipher systems, which will help to understand them. It describes dozens of cryptography algorithms, gives practical advice on how to implement them into cryptographic software, and shows how they can be used to solve security problems.
Comments are closed.