Practical Cryptography Intro To Encryption Encoding Hashing On Cli

Lec 7 Intro To Cryptography Pdf Cryptography Encryption Join me as i perform encryption, encoding and hashing on the linux command line. A modern practical book about cryptography for developers with code examples, covering core concepts like: hashes (like sha 3 and blake2), mac codes (like hmac and gmac), key derivation functions (like scrypt, argon2), key agreement protocols (like dhke, ecdh), symmetric ciphers (like aes and chacha20, cipher block modes, authenticated.
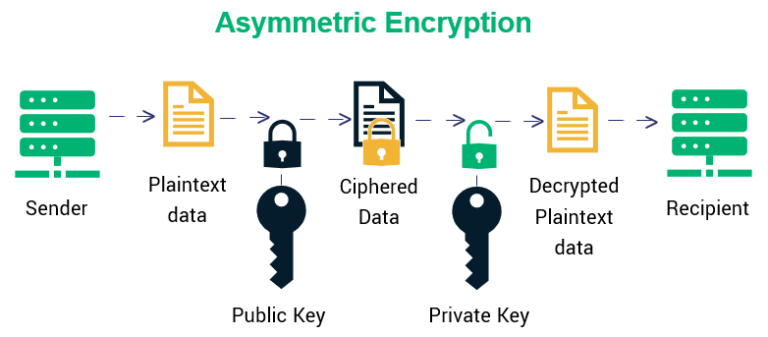
Cryptography Encryption And Hashing Information Technology Rngs slowly produce true random bits from analog sources, in a nondeterministic way, and with no guarantee of high entropy. prngs produce random looking bits quickly from digital sources, in a deterministic way, and with maximum entropy. A modern practical book about cryptography for developers with code examples, covering core concepts like: hashes (like sha 3 and blake2), mac codes (like hmac and gmac), key derivation functions (like scrypt, argon2), key agreement protocols (like dhke, ecdh), symmetric ciphers (like aes and chacha20, cipher block modes, authenticated. This hands on lab will equip you with essential knowledge and skills related to encoding schemes, hash algorithms, and the use of tools like openssl and gnu privacy guard (gpg). Encryption is an encoding technique in which a message is encoded by using an encryption algorithm in such a way that only authorized personnel can access the message or information.
-768.webp)
Encryption Vs Encoding Vs Hashing Geeksforgeeks This hands on lab will equip you with essential knowledge and skills related to encoding schemes, hash algorithms, and the use of tools like openssl and gnu privacy guard (gpg). Encryption is an encoding technique in which a message is encoded by using an encryption algorithm in such a way that only authorized personnel can access the message or information. The dramatic increase of information transmitted electronically has led to an increased reliance on cryptography. this book discusses the theories and concepts behind modern cryptography and demonstrates how to develop and implement cryptographic algorithms using c programming language. This book will teach you the basics of applied cryptography in almost free of math style, following a step by step approach with lots of code examples and practical exercises (hands on experience), just like when you learn web development, databases or mobile apps. At the end of this course you should have a thorough understanding of encryption and the importance of things like key lengths, ciphers, hashing algorithms and certificate authorities. In this article, we’ll explore symmetric encryption (aes), asymmetric encryption (rsa), hybrid encryption, digital signatures, and hashing using openssl on linux.
Comments are closed.