Ppt Eavesdropping Attack Network Projects Research Ideas Powerpoint
Ppt Eavesdropping Attack Network Projects Research Ideas Powerpoint Download presentation by click this link. while downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server. This coloured powerpoint icon depicts an eavesdropping attack, a malicious act of intercepting private communications. it is a great visual aid for presentations on cyber security and data privacy.

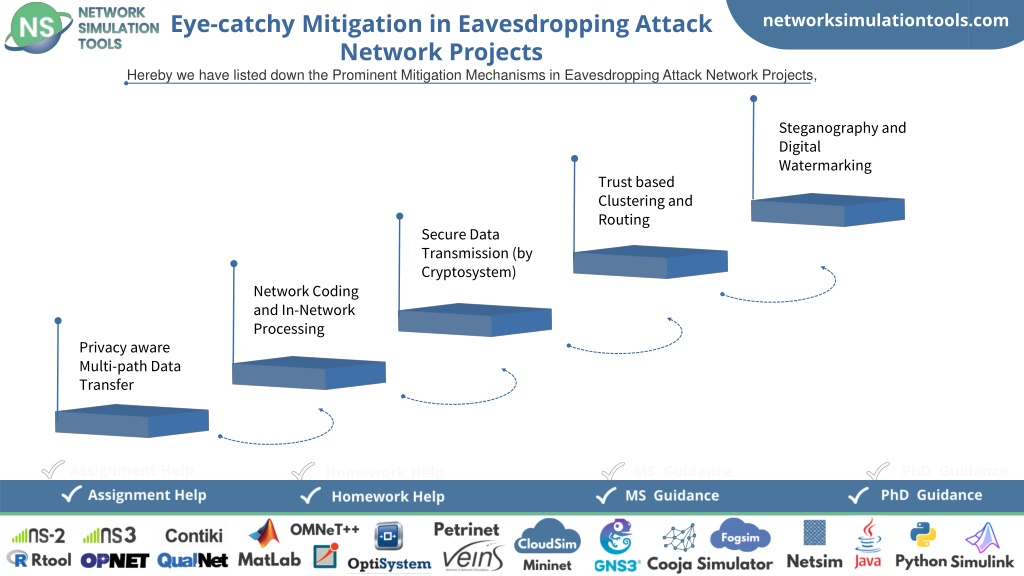
Ppt Eavesdropping Attack Network Projects Research Ideas Powerpoint Eavesdropping ppt 22012024 free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. It also outlines prevention methods such as strong password generation, multi factor authentication, and innovative research ideas like bio key generation and honey encryption. additionally, the document offers guidance and assignment help for phd and ms students in this domain. What is a man in the middle (mitm) attack? an mitm attack refers to a broad range of active eavesdropping techniques in which an attacker attempts to intercept, read, or alter information moving between two or more computers. Attack scenarios – kracker jack wavesec an open source software solution for securing wireless networks uses frees wan ipsec implementation will thwart passive eavesdropping of wireless network communications.
Ppt Eavesdropping Attack Network Projects Research Ideas Powerpoint What is a man in the middle (mitm) attack? an mitm attack refers to a broad range of active eavesdropping techniques in which an attacker attempts to intercept, read, or alter information moving between two or more computers. Attack scenarios – kracker jack wavesec an open source software solution for securing wireless networks uses frees wan ipsec implementation will thwart passive eavesdropping of wireless network communications. Create your espionage eavesdropping presentation with our editable espionage eavesdropping powerpoint presentation template. this powerpoint template available in warm colors eg : pink, white and editable shapes icons, all shapes and design elements are fully editable. Crystalgraphics is the award winning provider of the world’s largest collection of templates for powerpoint and google slides. so, take your time and look at what we have for eavesdropping. we think you’ll like what you see!. An eavesdropping attack is a covert and unapproved interference of correspondence between two parties. the eavesdropper acquires unapproved access to sensitive data, like passwords, financial details, or proprietary innovations, without the information or consent of the communicating parties. Understand network eavesdropping with sniffer tools from how they work to their uses in security and attack prevention. learn about passive and active sniffer modes, ways to detect sniffing, and the vulnerabilities they expose.

Top 10 Eavesdropping Attack Ppt Templates With Professional Designs Create your espionage eavesdropping presentation with our editable espionage eavesdropping powerpoint presentation template. this powerpoint template available in warm colors eg : pink, white and editable shapes icons, all shapes and design elements are fully editable. Crystalgraphics is the award winning provider of the world’s largest collection of templates for powerpoint and google slides. so, take your time and look at what we have for eavesdropping. we think you’ll like what you see!. An eavesdropping attack is a covert and unapproved interference of correspondence between two parties. the eavesdropper acquires unapproved access to sensitive data, like passwords, financial details, or proprietary innovations, without the information or consent of the communicating parties. Understand network eavesdropping with sniffer tools from how they work to their uses in security and attack prevention. learn about passive and active sniffer modes, ways to detect sniffing, and the vulnerabilities they expose.
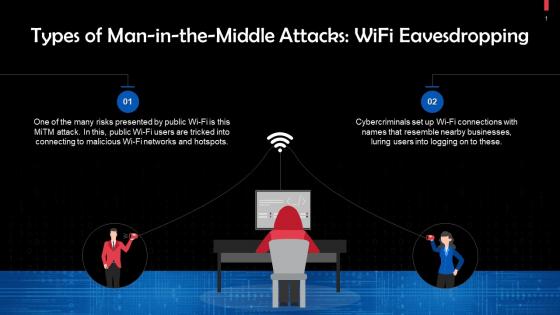
Eavesdropping Attack Powerpoint Presentation And Slides Ppt Sample An eavesdropping attack is a covert and unapproved interference of correspondence between two parties. the eavesdropper acquires unapproved access to sensitive data, like passwords, financial details, or proprietary innovations, without the information or consent of the communicating parties. Understand network eavesdropping with sniffer tools from how they work to their uses in security and attack prevention. learn about passive and active sniffer modes, ways to detect sniffing, and the vulnerabilities they expose.

Detection Of Eavesdropping Attack Network Projects Network Simulation
Comments are closed.