Polymorphic Virus Detection And Prevention Guide
Polymorphic Virus How To Detect Prevent 7 Quick Tricks Learn how polymorphic viruses evade detection, impact cybersecurity, and how modern defenses like ngav stop advanced malware threats. Discover how polymorphic viruses mutate to evade detection, real world examples, and how to detect and prevent these evolving malware threats.

Polymorphic Virus How To Detect Prevent 7 Quick Tricks Polymorphic viruses: the invisible digital threat and how to secure your systems a comprehensive guide on polymorphic viruses. This blog explains how polymorphic viruses work, their key characteristics, real life examples, spread mechanisms, and the best practices for detecting and preventing them using heuristic analysis, behavioral detection, and advanced threat monitoring tools. Discover what polymorphic malware is, how it evades detection, examples, challenges & how to prevent polymorphic viruses in your systems with manageengine. Discover how polymorphic viruses mutate to bypass antivirus software. learn detection methods, real world examples, and defense strategies against shape shifting malware.
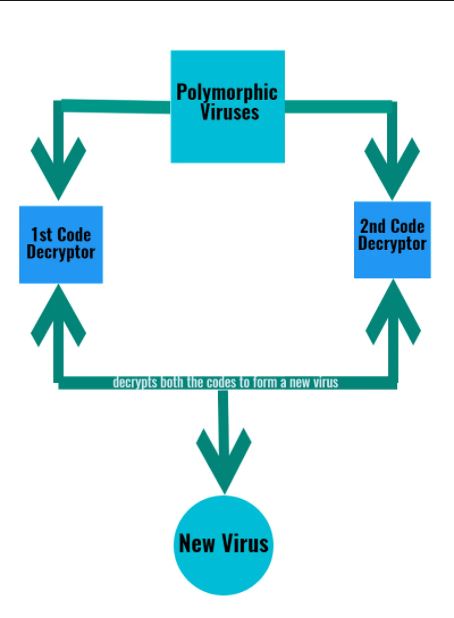
Polymorphic Virus Let S Tech It Easy Discover what polymorphic malware is, how it evades detection, examples, challenges & how to prevent polymorphic viruses in your systems with manageengine. Discover how polymorphic viruses mutate to bypass antivirus software. learn detection methods, real world examples, and defense strategies against shape shifting malware. Understanding how a polymorphic virus in cyber security works and learning prevention methods is essential for both individuals and organizations. here, we will discuss what a polymorphic virus is, how it works, real world examples, and the best practices to detect and prevent it in cyber security. A polymorphic virus, sometimes referred to as a metamorphic virus, is a type of malware that is programmed to repeatedly mutate its appearance or signature files through new decryption routines. This comprehensive guide will explore the concept of polymorphic malware, delve into its characteristics and techniques, and discuss how sentinelone endpoint protection provides an effective defense against these elusive threats. This article provides a comprehensive guide to understanding and combating polymorphic malware.
Comments are closed.