Phishing Prevention Do Don T Never Cheat Sheet Intrust It
Phishing Prevention Cheat Sheet Free Download Aeko Tech This guide reminds you how to avoid falling victim to phishing. download and share this phishing prevention cheat sheet with your team. We’ve created a one page cheat sheet with phishing prevention tips. the do’s, don’ts and nevers will help you and your team protect company data and personal information.
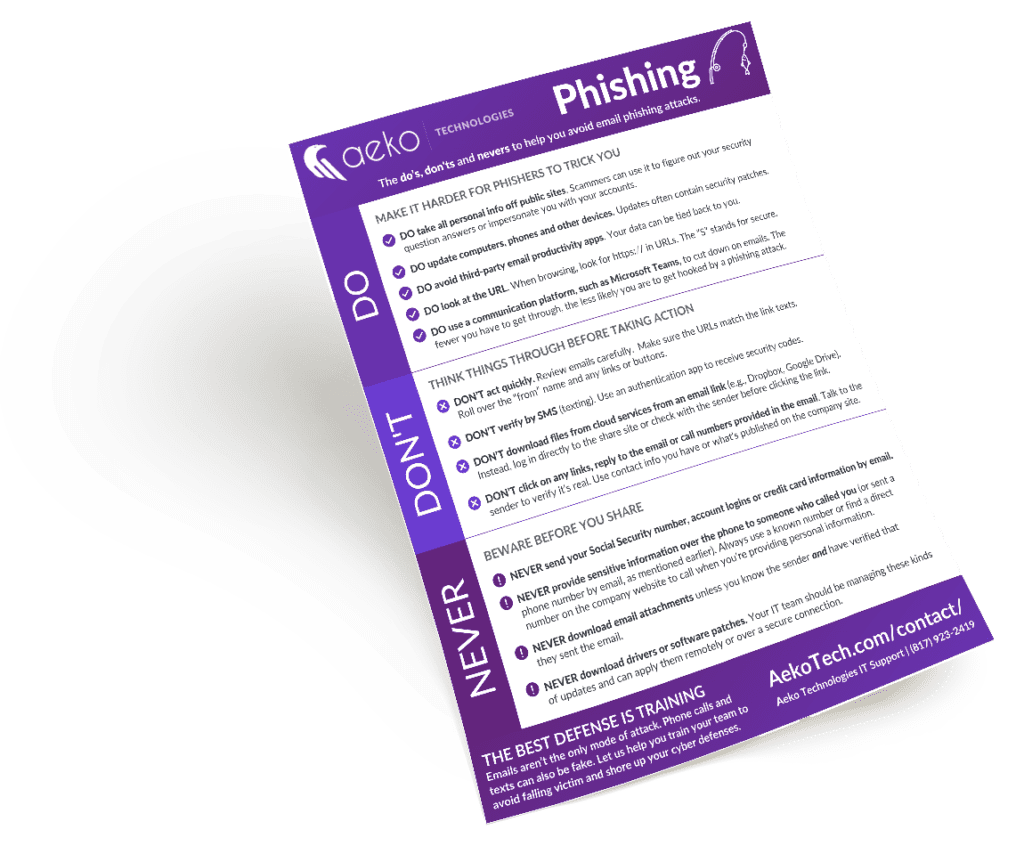
Phishing Prevention Cheat Sheet Free Download Aeko Tech Download our cheat sheet to help inform or remind your team of the do's, don'ts and nevers to avoid falling victim to phishing attacks. We’ll explain and provide nine phishing scam prevention tips so you can know what to do when you encounter a phishing email and the things to look out for if there’s a cybercriminal in your waters. Need help implementing best practices to prevent phishing attacks or do you have other cybersecurity or it support needs for your business? contact us or book a meeting for a no obligation consultation. Our simple cheat sheet shows your team at a glance the do's, don'ts and nevers of phishing prevention. download it, post it, share it and, above all, talk about it!.

Phishing Prevention Tips Cheat Sheet Aeko Tech Fort Worth Need help implementing best practices to prevent phishing attacks or do you have other cybersecurity or it support needs for your business? contact us or book a meeting for a no obligation consultation. Our simple cheat sheet shows your team at a glance the do's, don'ts and nevers of phishing prevention. download it, post it, share it and, above all, talk about it!. Learn the do's don'ts and nevers of phishing prevention with this one page cheat sheet. download to post and share with your team. Use the tools in the prevent phishing and malware toolbox to get helpful links to trusted dns tools, adblockers and more to help protect yourself against falling victim to phishing and viruses. The most powerful tool in their arsenal is simple trickery. phishing was the second most common cause of data breaches. this term describes how an attacker can gain information or access by impersonating a third party: like a colleague, business, government agency, friend, or relative. It's time to dive deeper into our cybersecurity tips for the month, starting with phishing: phishing attempts occur through the sending of harmful links, emails or attachments that could.

Phishing Prevention Do Don T Never Cheat Sheet Intrust It Learn the do's don'ts and nevers of phishing prevention with this one page cheat sheet. download to post and share with your team. Use the tools in the prevent phishing and malware toolbox to get helpful links to trusted dns tools, adblockers and more to help protect yourself against falling victim to phishing and viruses. The most powerful tool in their arsenal is simple trickery. phishing was the second most common cause of data breaches. this term describes how an attacker can gain information or access by impersonating a third party: like a colleague, business, government agency, friend, or relative. It's time to dive deeper into our cybersecurity tips for the month, starting with phishing: phishing attempts occur through the sending of harmful links, emails or attachments that could.

Know The Types Of Phishing Attacks The most powerful tool in their arsenal is simple trickery. phishing was the second most common cause of data breaches. this term describes how an attacker can gain information or access by impersonating a third party: like a colleague, business, government agency, friend, or relative. It's time to dive deeper into our cybersecurity tips for the month, starting with phishing: phishing attempts occur through the sending of harmful links, emails or attachments that could.

Phishing Scam 04 Pdf Phishing Security
Comments are closed.