Phishing Nist
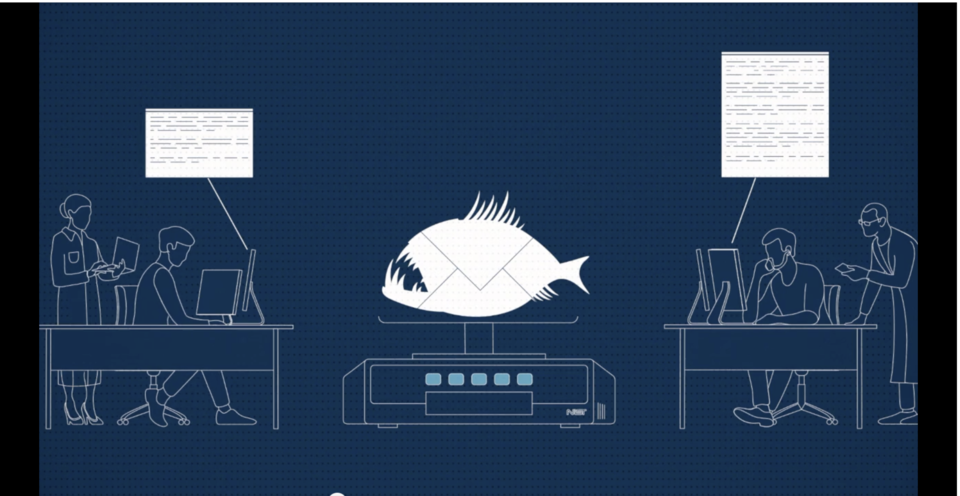
Nist Phishing Scale Phishing is one of the most common types of cyber crime. these scams use convincing emails or other messages, such as text messages or social media messages, to trick users into opening harmful links, downloading malicious software, or submitting sensitive information, such as credentials. What is the nist phish scale? the nist phish scale is a federal scoring system that’s used to determine human phishing detection difficulty. this system has two main components: firstly, the observable characteristics (visual cues) in a phishing email.

Sbcc Protecting Your Small Business From Phishing Risks The nist phish scale is a method created for cybersecurity and phishing awareness training implementers to rate an email's human phishing detection difficulty as part of their cybersecurity awareness and phishing training programs. The nist phish scale is a method for training implementers to rate an email’s human phishing detection difficulty, evaluating both the properties of a phishing email itself and the characteristics of the email’s recipients. The nist phish scale is available at no cost for academic use. to proceed, organizations must establish a research license agreement with nist. for any commercial applications, interested companies are required to obtain a commercialization license. Understanding how a phishing attack works is the first step to stopping one. in this guide, you will learn what phishing is, how attackers carry it out, every major variant, the warning signs to watch for, and the exact steps to protect yourself and your organisation.

Nist On Phishing Awareness The nist phish scale is available at no cost for academic use. to proceed, organizations must establish a research license agreement with nist. for any commercial applications, interested companies are required to obtain a commercialization license. Understanding how a phishing attack works is the first step to stopping one. in this guide, you will learn what phishing is, how attackers carry it out, every major variant, the warning signs to watch for, and the exact steps to protect yourself and your organisation. Recent efforts have focused on the nist phish scale, a method for rating the human detection difficulty of phishing emails considering both the characteristics of the email and the user context of the email's recipient. the nist phish scale is available at no cost for academic use. Phishing is the use of convincing emails or other messages to trick us into opening harmful links or downloading malicious software. these messages are often disguised as a trusted source, such as your bank, credit card company, or even a leader within your own business. Phishing resistant authenticators should be paired with a comprehensive phishing prevention program that includes user awareness and training, email protection controls, data loss prevention tools, and network security capabilities. Nist disclaimer: any mention of commercial products or reference to commercial organizations is for information only; it does not imply recommendation or endorsement by the national institute of standards and technology nor does it imply that the products mentioned are necessarily the best available for the purpose.

Phishing Nist Recent efforts have focused on the nist phish scale, a method for rating the human detection difficulty of phishing emails considering both the characteristics of the email and the user context of the email's recipient. the nist phish scale is available at no cost for academic use. Phishing is the use of convincing emails or other messages to trick us into opening harmful links or downloading malicious software. these messages are often disguised as a trusted source, such as your bank, credit card company, or even a leader within your own business. Phishing resistant authenticators should be paired with a comprehensive phishing prevention program that includes user awareness and training, email protection controls, data loss prevention tools, and network security capabilities. Nist disclaimer: any mention of commercial products or reference to commercial organizations is for information only; it does not imply recommendation or endorsement by the national institute of standards and technology nor does it imply that the products mentioned are necessarily the best available for the purpose.
Phishing Nist Phishing resistant authenticators should be paired with a comprehensive phishing prevention program that includes user awareness and training, email protection controls, data loss prevention tools, and network security capabilities. Nist disclaimer: any mention of commercial products or reference to commercial organizations is for information only; it does not imply recommendation or endorsement by the national institute of standards and technology nor does it imply that the products mentioned are necessarily the best available for the purpose.
Comments are closed.