Phishing Attacks Cybersecurity Glossary

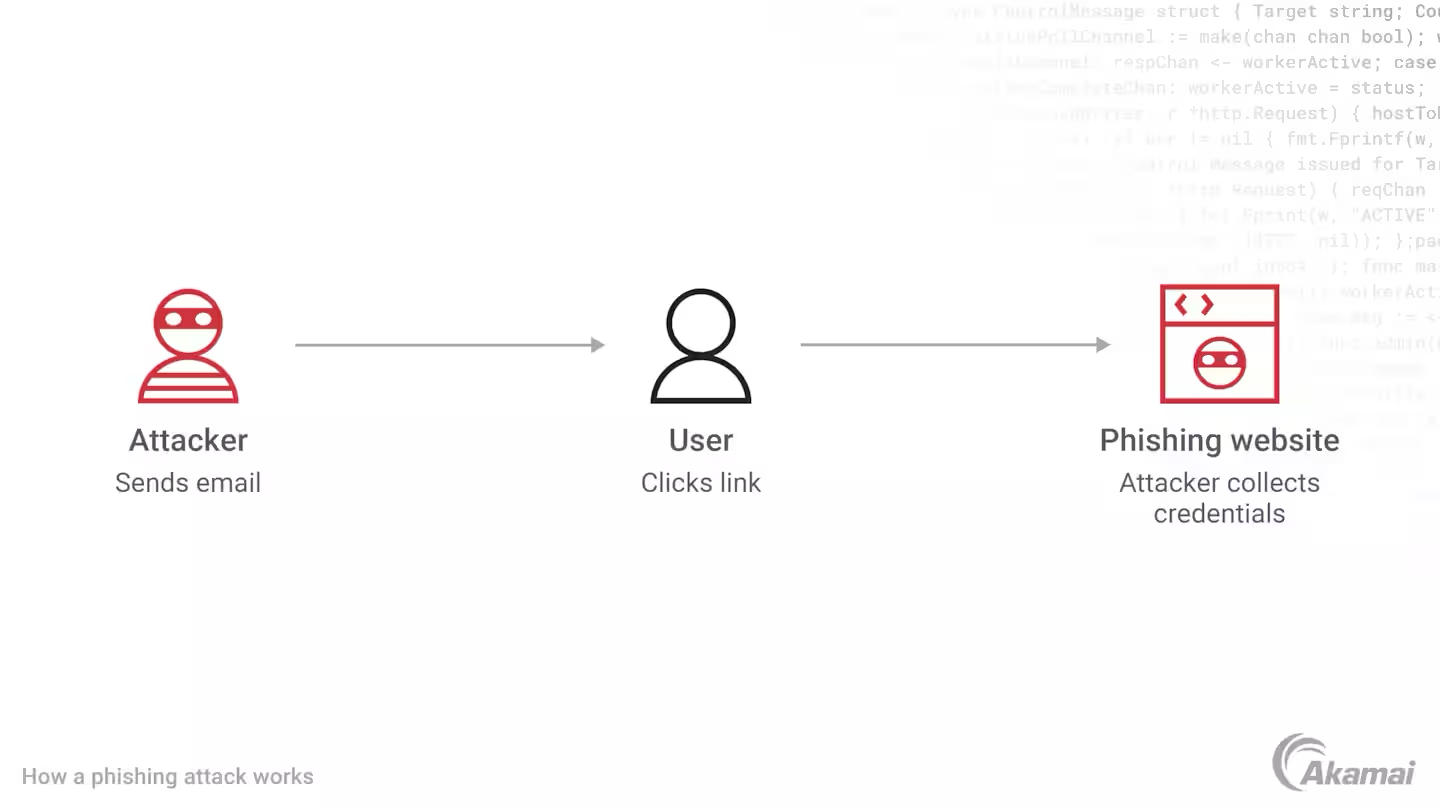
Phishing Attacks Cybersecurity Glossary Hoxhunt's cybersecurity glossary is here to help you navigate the terminology around phishing and cybersecurity. An attack in which the subscriber is lured (usually through an email) to interact with a counterfeit verifier or relying party and tricked into revealing information that can be used to masquerade as that subscriber to the real verifier or relying party.

Phishing Attacks Cybersecurity Glossary Phishing attacks are deceptive attempts by cybercriminals to trick individuals into revealing sensitive information or downloading malicious software. according to cisa, phishing typically involves harmful links, emails, or attachments designed to appear as though they are from a reputable source. Phishing is a cyber threat that uses social engineering to trick people into providing sensitive information that could compromise an organization. learn about the 19 different kinds of attacks. This post aims to help english learners grasp vital cybersecurity terms, particularly those related to phishing attacks, by exploring the entries in this phishing glossary. A set of straightforward definitions for common cyber security terms used on the ncsc website.

Phishing Attacks Definition Types And Prevention Strategies Netsmartz This post aims to help english learners grasp vital cybersecurity terms, particularly those related to phishing attacks, by exploring the entries in this phishing glossary. A set of straightforward definitions for common cyber security terms used on the ncsc website. A glossary of definitions for various different cybersecurity terms and concepts. The niccs glossary contains key cybersecurity terms that enable clear communication and a common understanding of cybersecurity definitions. Learn about the different types of phishing attacks and how the can impact your business in our complete phishing glossary. A technique in which an attacker gains access to an email account and, through the course of monitoring email threads, will inject phishing urls, malware, or other malicious information into the email conversation.
Phishing Technology Glossary Definitions G2 A glossary of definitions for various different cybersecurity terms and concepts. The niccs glossary contains key cybersecurity terms that enable clear communication and a common understanding of cybersecurity definitions. Learn about the different types of phishing attacks and how the can impact your business in our complete phishing glossary. A technique in which an attacker gains access to an email account and, through the course of monitoring email threads, will inject phishing urls, malware, or other malicious information into the email conversation.

Phishing Attacks Explained Easydmarc Glossary Learn about the different types of phishing attacks and how the can impact your business in our complete phishing glossary. A technique in which an attacker gains access to an email account and, through the course of monitoring email threads, will inject phishing urls, malware, or other malicious information into the email conversation.
Phishing Attacks
Comments are closed.