Pgp Pdf Encryption Public Key Cryptography

Lab02 Public Key Cryptography Pdf Cryptography Public Key A commentary on the interoperability of encrypting pdf documents with public key cryptography. Symmetric key cryptography uses one secret key for both encrypting and decrypting data. public key cryptography uses two keys: a public key (shared with everyone) for encryption and a private key (kept secret) for decryption.

Lecture 2 Public Key Cryptography Pdf Cryptography Public Key Public key cryptography is an asymmetric scheme that uses a pair of keys for encryption: a public key, which encrypts data, and a corresponding private, or secret key for decryption. Pdf | on mar 7, 2012, hilal m. yousif al bayatti and others published pgp protocol and its applications | find, read and cite all the research you need on researchgate. Pgp encryption uses a serial combination of hashing, data compression, symmetric key cryptography, and finally public key cryptography; each step uses one of several supported algorithms. each public key is bound to a username or an e mail address. For situations where you can guide the user through creating and exporting their digital identity, public key encryption is a very effective way of controlling document distribution.

Pgp Encryption Decryption Public Key Used To Encrypt Secret Key Used Pgp encryption uses a serial combination of hashing, data compression, symmetric key cryptography, and finally public key cryptography; each step uses one of several supported algorithms. each public key is bound to a username or an e mail address. For situations where you can guide the user through creating and exporting their digital identity, public key encryption is a very effective way of controlling document distribution. Pgp gnupg uses a combination of encryption methodologies such as hashing, data compression, symmetric key cryptography, and public key cryptography to keep data secure. This document discusses how to use openpgp for encryption. it describes generating a public private key pair, signing the public key, exporting the public key, importing another user's public key, encrypting a file using the recipient's public key, and decrypting the encrypted file. As we discussed in the previous chapter, pgp is built on the foundation of public key cryptography. when you set up pgp, you generate a pair of keys: a public key and a private key. The encrypted document can only be decrypted by someone with a private key that complements one of the recipients' public keys. in particular, you cannot decrypt a document encrypted by you unless you included your own public key in the recipient list.
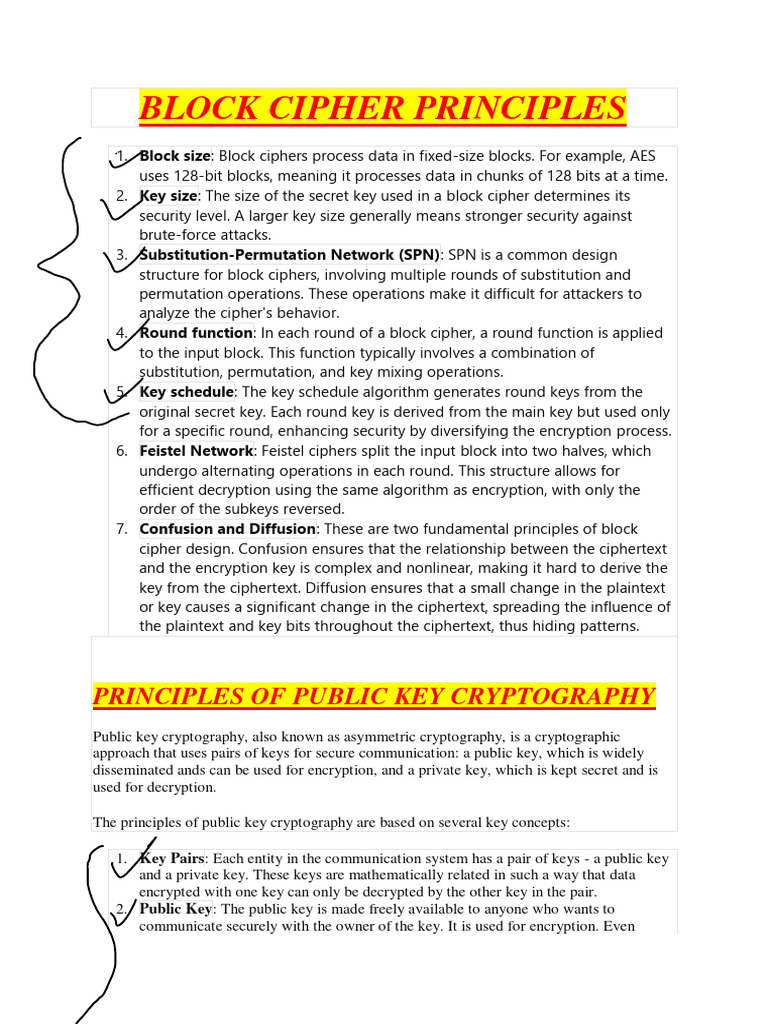
Principles Of Public Key Cryptography Pdf Public Key Cryptography Pgp gnupg uses a combination of encryption methodologies such as hashing, data compression, symmetric key cryptography, and public key cryptography to keep data secure. This document discusses how to use openpgp for encryption. it describes generating a public private key pair, signing the public key, exporting the public key, importing another user's public key, encrypting a file using the recipient's public key, and decrypting the encrypted file. As we discussed in the previous chapter, pgp is built on the foundation of public key cryptography. when you set up pgp, you generate a pair of keys: a public key and a private key. The encrypted document can only be decrypted by someone with a private key that complements one of the recipients' public keys. in particular, you cannot decrypt a document encrypted by you unless you included your own public key in the recipient list.

Lecture 06 Public Key Cryptography And Pki Pdf Public Key As we discussed in the previous chapter, pgp is built on the foundation of public key cryptography. when you set up pgp, you generate a pair of keys: a public key and a private key. The encrypted document can only be decrypted by someone with a private key that complements one of the recipients' public keys. in particular, you cannot decrypt a document encrypted by you unless you included your own public key in the recipient list.
Comments are closed.