Pdf Side Channel Attacks In Code Based Cryptography
No Ai Did Not Break Post Quantum Cryptography The purpose of this article is to describe what kind of attacks have been proposed against code based constructions and what is missing. The cfs, stern and kks signature schemes are post quantum secure because they are based on hard problems of coding theory. the purpose of this article is to describe what kind of attacks have been proposed against code based constructions and what is missing.
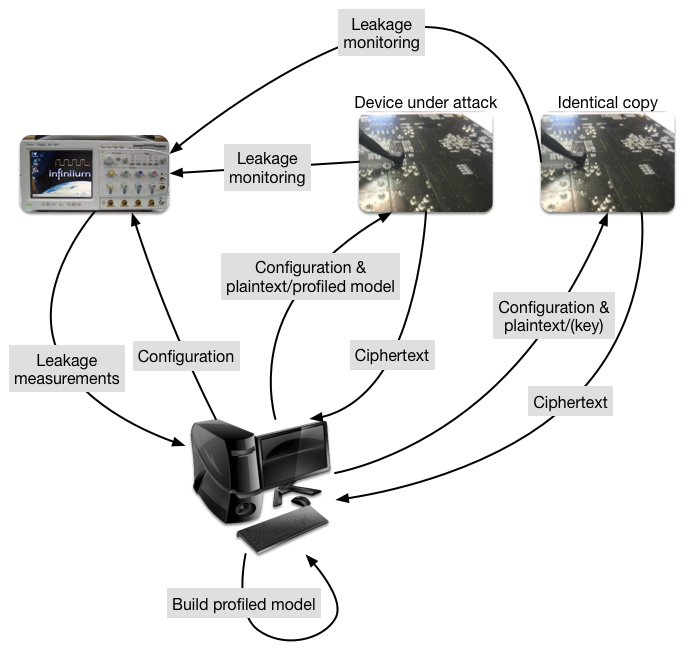
A Data Augmentation Method For Side Channel Attacks On Cryptographic For the the art of re s side chanels atacks against code based [5]. cryptosystems which. The purpose of this article is to describe what kind of attacks have been proposed against code based constructions and what is missing. Side channel attacks pose significant risks to the security of cryptographic systems.by understanding the information flows associated with these attacks, we can develop effective countermeasures to protect sensitive data. This paper provides a comprehensive characterization of side channel vulnerabilities and countermeasures, as well as evaluations of cryptographic applications related to side channel attacks.

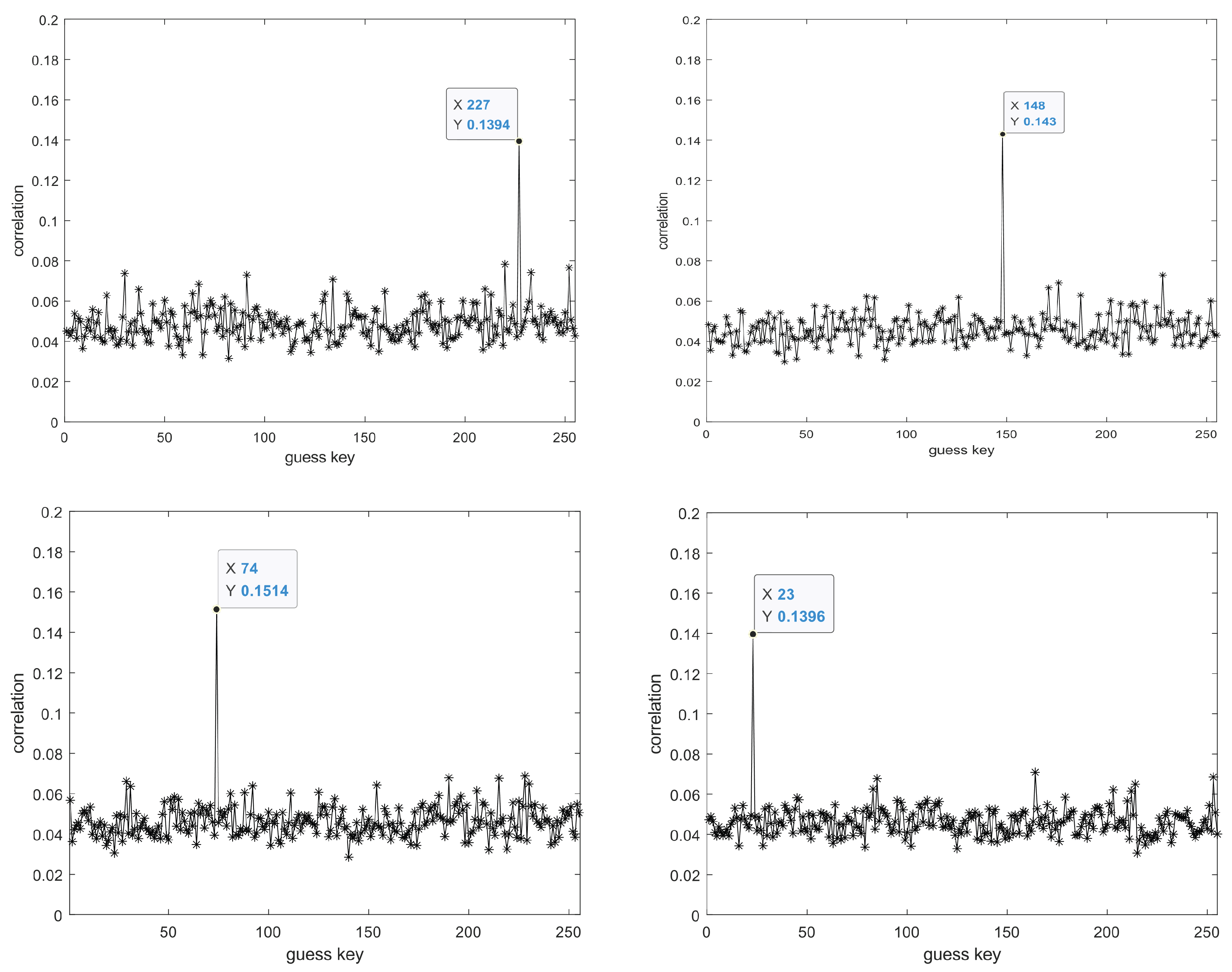
Side Channel Attack Of Lightweight Cryptography Based On Mixcolumn Side channel attacks pose significant risks to the security of cryptographic systems.by understanding the information flows associated with these attacks, we can develop effective countermeasures to protect sensitive data. This paper provides a comprehensive characterization of side channel vulnerabilities and countermeasures, as well as evaluations of cryptographic applications related to side channel attacks. Abstract side channel attacks are easy to implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. these attacks pose a serious threat to the security of cryptographic modules. Particular attention is given to the practical vulnerabilities of these schemes against cryptanalytic attacks, such as side channel attacks, fault injection attacks, and specific techniques for key and message recovery. Frequency based side channel attack is much prevalent in mobile devices such as pdas, cell phones and pagers. it has been proved that this attack is powerful even when the traces are misaligned, whereas the previously researched dema are weak [4]. A vast array of attack techniques that exploit side channels has been devel oped and studied over several decades, and side channel attacks are a serious threat to computer security in many settings.

Side Channel Attack Of Lightweight Cryptography Based On Mixcolumn Abstract side channel attacks are easy to implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. these attacks pose a serious threat to the security of cryptographic modules. Particular attention is given to the practical vulnerabilities of these schemes against cryptanalytic attacks, such as side channel attacks, fault injection attacks, and specific techniques for key and message recovery. Frequency based side channel attack is much prevalent in mobile devices such as pdas, cell phones and pagers. it has been proved that this attack is powerful even when the traces are misaligned, whereas the previously researched dema are weak [4]. A vast array of attack techniques that exploit side channels has been devel oped and studied over several decades, and side channel attacks are a serious threat to computer security in many settings.
Comments are closed.