Pdf Modification In Elliptic Curve Cryptography Based Mutual

Elliptic Curve Cryptography And Applications Pdf Public Key To overcome this there are numerous authentication procedures that have been documented. the mutual authentication system for the smart grid that is based on elliptic curve cryptography and biometrics was thus introduced by a.a. khan et al.’s. this protocol is secure from various attacks. In this paper, we propose an efficient biometric based remote user authentication scheme using smart cards, in which the computation cost is relatively low compared with other related schemes.

Pdf Applications Of Elliptic Curve Cryptography This paper derives a privacy preserving authentication scheme using a tamper resistant device at the smart appliance and pseudo identities, and shows that the authentication process is made very efficient by means of hash based message authentication code (hmac). The mutual authentication system for the smart grid that is based on elliptic curve cryptography and biometrics was thus introduced by a.a. khan et al.’s. this protocol is secure from various attacks. Download the full pdf of modification in elliptic curve cryptography based mutual. includes comprehensive summary, implementation details, and key takeaways.shivali meenakshi. In this paper, a lightweight mutual authentication protocol that can be applied in a mobile cloud environment is proposed, based on elliptic curve cryptography (ecc) and 1 way hash functions that can be used to provide high levels of security at minimum overhead.

Pdf An Advanced Elliptic Curve Cryptography Based Mutual Download the full pdf of modification in elliptic curve cryptography based mutual. includes comprehensive summary, implementation details, and key takeaways.shivali meenakshi. In this paper, a lightweight mutual authentication protocol that can be applied in a mobile cloud environment is proposed, based on elliptic curve cryptography (ecc) and 1 way hash functions that can be used to provide high levels of security at minimum overhead. In this paper, we propose an efficient biometric based remote user authentication scheme using smart cards, in which the computation cost is relatively low compared with other related schemes. View a pdf of the paper titled modification in elliptic curve cryptography based mutual authentication scheme for smart grid communication using biometric approach, by shivali meenakshi. We then propose a secure and efficient two‐factor authentication and key agreement protocol for sip using elliptic curve cryptography (ecc). we analyze the security of the proposed scheme and. In the present paper, we design an ecc based mutual authentication protocol for smart grid communication using biometric approach.
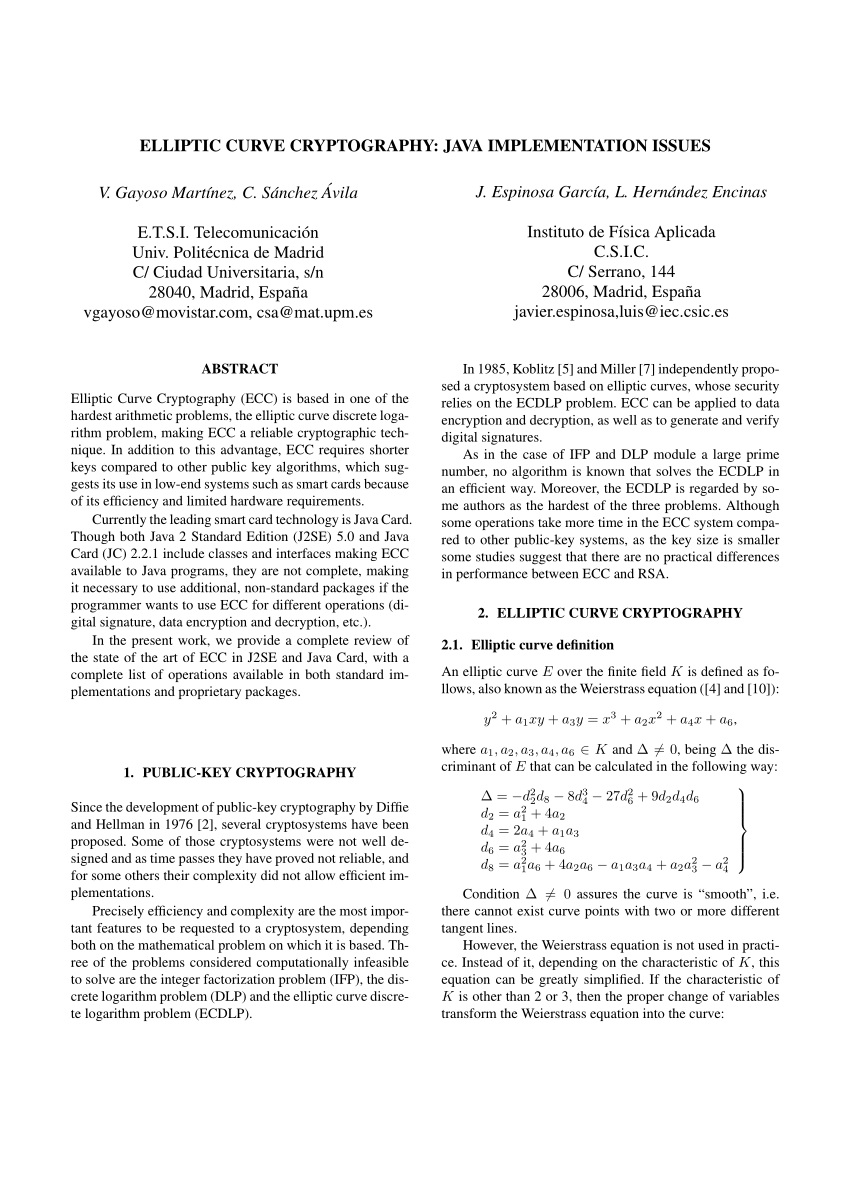
Pdf Elliptic Curve Cryptography Java Implementation Issues In this paper, we propose an efficient biometric based remote user authentication scheme using smart cards, in which the computation cost is relatively low compared with other related schemes. View a pdf of the paper titled modification in elliptic curve cryptography based mutual authentication scheme for smart grid communication using biometric approach, by shivali meenakshi. We then propose a secure and efficient two‐factor authentication and key agreement protocol for sip using elliptic curve cryptography (ecc). we analyze the security of the proposed scheme and. In the present paper, we design an ecc based mutual authentication protocol for smart grid communication using biometric approach.

Pdf Evaluating Elliptic Curve Cryptography In Constrained We then propose a secure and efficient two‐factor authentication and key agreement protocol for sip using elliptic curve cryptography (ecc). we analyze the security of the proposed scheme and. In the present paper, we design an ecc based mutual authentication protocol for smart grid communication using biometric approach.
Comments are closed.