Pdf Cryptographic Solution Based Secure Elliptic Curve Cryptography

Ecommerce Security Through Elliptic Curve Cryptography Pdf Keeping in mind the security perspective, the concept of elliptic curve cryptography (ecc) is taken into consideration. so, in this paper, we have proposed a cryptographic solution based secure ecc enabled rfid mutual authentication protocol for iov. Keeping in mind the security perspective, the concept of elliptic curve cryptography (ecc) is taken into consideration. so, in this paper, we have proposed a cryptographic solution based secure ecc enabled rfid mutual authentication protocol for iov.

Elliptic Curve Cryptography 30 Download Scientific Diagram This article provides a comprehensive overview of ecc, the mathematical foundations underpinning its security, its key protocols—including ecdh, ecdsa, and ecies—and its applications in contemporary digital security, from secure web communications to cryptocurrencies. To ensure the security and integrity of the data, various cryptographic techniques are used. therefore, in this paper, we propose a secure and optimized hybrid cryptographic scheme for the secure sharing of data by combining advanced encryption standard (aes) and elliptic curve cryptography (ecc). The purpose of this paper is to discuss the theoretical basis, security analysis, and practical application cases of elliptic curve cryptography, to provide readers with a comprehensive. Here we introduce the novel approach of securely utilising the transport layer security secure socket layer (tls ssl) protocol with a modified elliptic curve cryptographic (ecc) algorithm which supports the security parameters of confidentiality, authentication and integrity.
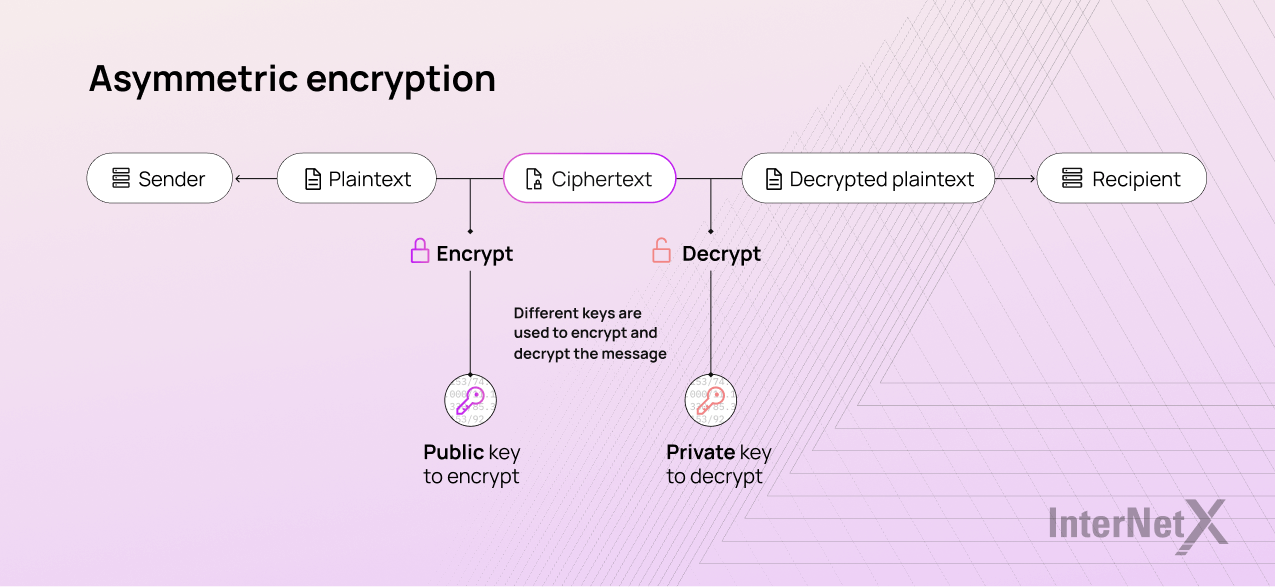
Elliptic Curve Cryptography Ecc The purpose of this paper is to discuss the theoretical basis, security analysis, and practical application cases of elliptic curve cryptography, to provide readers with a comprehensive. Here we introduce the novel approach of securely utilising the transport layer security secure socket layer (tls ssl) protocol with a modified elliptic curve cryptographic (ecc) algorithm which supports the security parameters of confidentiality, authentication and integrity. Abstract elliptic curve cryptography (ecc) has emerged as a cornerstone of modern cryptographic systems, offering robust security with unparalleled efficiency. this paper provides a critical analysis of ecc’s mathematical foundations, practical applications, and evolving challenges in securing data across industries such as iot, blockchain. Elliptic curve based encryption enhances security in machine learning by encrypting both data and models. for example, in medical applications, patient data, including diagnoses and medical histories, is encrypted before sharing. This is the case for the elliptic curve difie hellman (ecdh). for ecdh, to prove that the key exchange is secure in the presence of an eavesdropper, we need to rely on a variant of the ecdlp. However, this approach gives rise to issues of trust and confidence. the value of cryptocurrency assets is based on their digital security (assured by code and cryptography) and public confidence in the decentralized system (rather than in third party intermediaries as in traditional banking).
How Does The Elliptic Curve Cryptography Ecc Algorithm Work Abstract elliptic curve cryptography (ecc) has emerged as a cornerstone of modern cryptographic systems, offering robust security with unparalleled efficiency. this paper provides a critical analysis of ecc’s mathematical foundations, practical applications, and evolving challenges in securing data across industries such as iot, blockchain. Elliptic curve based encryption enhances security in machine learning by encrypting both data and models. for example, in medical applications, patient data, including diagnoses and medical histories, is encrypted before sharing. This is the case for the elliptic curve difie hellman (ecdh). for ecdh, to prove that the key exchange is secure in the presence of an eavesdropper, we need to rely on a variant of the ecdlp. However, this approach gives rise to issues of trust and confidence. the value of cryptocurrency assets is based on their digital security (assured by code and cryptography) and public confidence in the decentralized system (rather than in third party intermediaries as in traditional banking).
Data Security Using Elliptic Curve Cryptography Pdf This is the case for the elliptic curve difie hellman (ecdh). for ecdh, to prove that the key exchange is secure in the presence of an eavesdropper, we need to rely on a variant of the ecdlp. However, this approach gives rise to issues of trust and confidence. the value of cryptocurrency assets is based on their digital security (assured by code and cryptography) and public confidence in the decentralized system (rather than in third party intermediaries as in traditional banking).
Enhanced Security Using Elliptic Curve Cryptography Combined With Hill
Comments are closed.