Pdf Erratum To An Efficient Code Based Threshold Ring Signature
Pdf Erratum To An Efficient Code Based Threshold Ring Signature Pdf | on oct 16, 2017, guomin zhou and others published erratum to “an efficient code based threshold ring signature scheme with a leader participant model” | find, read and cite. Erratum erratum to (an efficient code based threshold ring signature scheme with a leader participant model) guominzhou,1pengzeng,2xiaohuiyuan,3,4 siyuanchen,2andkim kwangraymondchoo5.

Pdf An Efficient Code Based Threshold Ring Signature Scheme With A G. zhou, p. zeng, x. yuan, s. chen, and k. r. choo, “an efficient code based threshold ring signature scheme with a leader participant model,” security and communication networks, vol. 2017, 7 pages, 2017. In this paper, we proposed a novel threshold ring signature scheme based on the hard problems in coding theory. we prove that our method satisfies correctness, unforgeability, and anonymity. In this paper, we use the ags identification scheme, which is a coding theory zero knowledge authentication protocol, to produce a ring signature and a threshold ring signature. In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes.
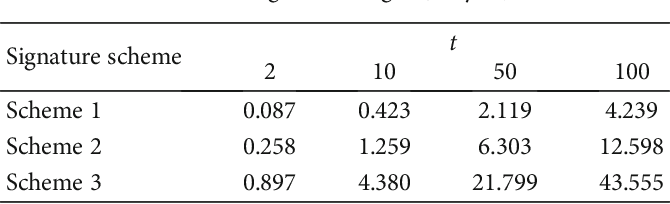
Table 2 From A New Code Based Linkable Threshold Ring Signature Scheme In this paper, we use the ags identification scheme, which is a coding theory zero knowledge authentication protocol, to produce a ring signature and a threshold ring signature. In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes. Threshold ring signature: subset of ring members cooperatively generate a signature so that the veri er cannot identify the identity of the actual signers. the rst code based threshold ring signature was proposed by aguilar et al. in 2008, it is based on the stern's identi cation scheme. In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes. In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes. There is a pressing need to design pkc schemes that are secure against quantum attacks. in this paper, we propose a novel code based threshold ring signature scheme with a.

Pdf An Efficient Multivariate Threshold Ring Signature Scheme Threshold ring signature: subset of ring members cooperatively generate a signature so that the veri er cannot identify the identity of the actual signers. the rst code based threshold ring signature was proposed by aguilar et al. in 2008, it is based on the stern's identi cation scheme. In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes. In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes. There is a pressing need to design pkc schemes that are secure against quantum attacks. in this paper, we propose a novel code based threshold ring signature scheme with a.

Pdf A New Code Based Linkable Threshold Ring Signature Scheme In this paper we also provide implementation results of the aguilar et al. scheme and our proposal, this is the first efficient implementation of this type of code based schemes. There is a pressing need to design pkc schemes that are secure against quantum attacks. in this paper, we propose a novel code based threshold ring signature scheme with a.

Pdf Efficient Threshold Signature Scheme
Comments are closed.