Pdf Engineering Authentication Process With Cloud Computing

Study Of Authentication And Authorization In Cloud Computing Pdf In this paper, an optimized infrastructure for secure authentication and authorization in cloud environment using sso (single sign on) is proposed. In this paper, we discussed the comprehensive and detailed frameworks constructed to assure successful authentication in cloud computing.
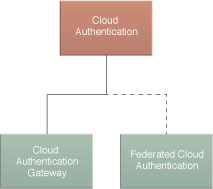
Cloud Computing Patterns Compound Patterns Cloud Authentication In this paper, an optimized infrastructure for secure authentication and authorization in cloud environment using sso (single sign on) is proposed. This paper will include overview for cloud computing, security overview including different authentication methods, followed by that will be a literature review for some of the proposed models and frameworks to handle authentication and a comparison between them. For the effective user authentication in the cloud computing environment, the authentication technologies described above should be used by combining them suitably or a secure user authentication method for the right purpose of cloud computing should be developed. The proposed process is a combination of ahp and cloud user behavior, and they put forward bam, a cloud user behavior authentication model based on multi partite graphs.

Cloud Computing Pdf For the effective user authentication in the cloud computing environment, the authentication technologies described above should be used by combining them suitably or a secure user authentication method for the right purpose of cloud computing should be developed. The proposed process is a combination of ahp and cloud user behavior, and they put forward bam, a cloud user behavior authentication model based on multi partite graphs. Here are studied and compared details about cloud computing services and providers, with particular emphasis the service oriented cloud computing architecture in terms of authentication and authorization. Abstract: cloud computing is a most widespread and popular form of computing, promising high reliability for customers and providers both at the same point of time for many fields, where cloud storage security is based on authentication and authorization in cloud computing. This paper discussed cloud computing characteristics and focused on the security issues, which can be solved by our prototype of authentication. further research could be realized to improve and to extend the present work by including and resolving the interoperability issues in the cloud. Authentication is central to any security issue, involving the verification process of the identity of a person or a process to access a secured system. therefore, authentication is extremely important to guarantee the smooth flow of information without troubles.
Comments are closed.