Part V Exploration Intruder Payload Processing
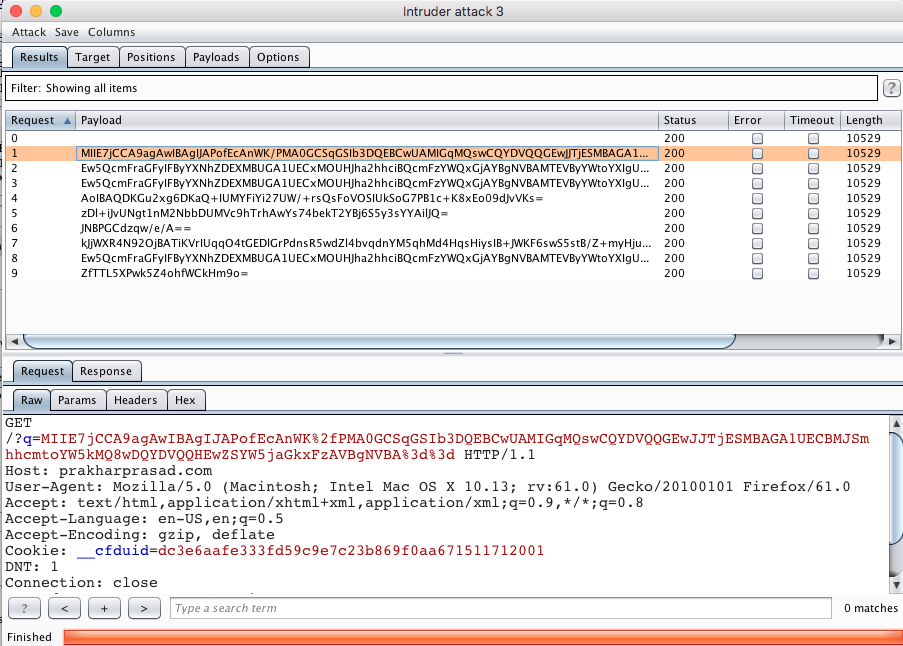
Part V Exploration Intruder Payload Processing Exploration intruder payload processing in the post, we'll utilise iintruderpayloadprocessor as a way to explore different extender api interfaces. You can configure payload processing rules so that burp intruder modifies payloads before it inserts them into the request. this is useful for a variety of purposes, such as when you need to: generate unusual payloads. wrap payloads up within a wider structure or encoding scheme prior to use.

Part V Exploration Intruder Payload Processing In this guide, we’ll focus on payload configuration a key step in mastering intruder attacks. whether you’re a beginner or looking to sharpen your skills, this breakdown will help you. Configure an appropriate position and payload (the tickets are stored at values between 1 and 100), then start the attack. you should find that at least five tickets will be returned with a status code of 200, indicating that they exist. When using burp suite intruder to perform an attack, the first step is to examine the positions within the request where we want to insert our payloads. these positions inform intruder about the locations where our payloads will be introduced (as we will explore in upcoming tasks). The payloads tab also enables us to modify intruder’s behavior regarding payloads, such as defining pre processing rules for each payload (e.g., adding a prefix or suffix, performing match and replace, or skipping payloads based on a defined regex).
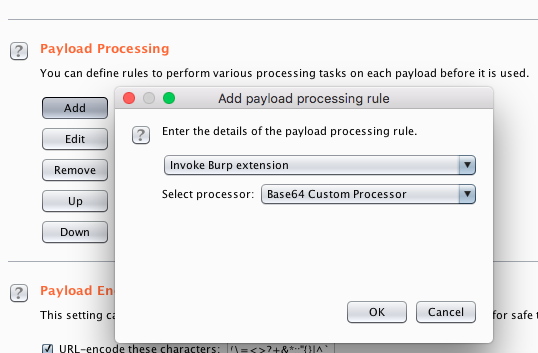
Part V Exploration Intruder Payload Processing When using burp suite intruder to perform an attack, the first step is to examine the positions within the request where we want to insert our payloads. these positions inform intruder about the locations where our payloads will be introduced (as we will explore in upcoming tasks). The payloads tab also enables us to modify intruder’s behavior regarding payloads, such as defining pre processing rules for each payload (e.g., adding a prefix or suffix, performing match and replace, or skipping payloads based on a defined regex). The battering ram attack type in burp suite intruder differs from sniper in that it places the same payload in every position simultaneously, rather than substituting. This article will cover the burp suite: intruder write up under the web fundamentals on thm. introduction welcome to the burp suite intruder room! in this room, we will explore burp suite's intruder module, which offers automated request manipulation. In this lesson, we will examine a short post to create a plugin for an example use case. this plugin will process the payload from the intruder and will execute the payload after processing. Your ultimate destination for mastering the art of ethical hacking. join the elite community of penetration testers and security researchers. © 2026 pentesterworld. all rights reserved.
Comments are closed.