Pam Software Basics Course Resources
Pam Software Basics Course Resources This section contains background information regarding the software used within the pam software basics course, underwater acoustics and marine mammal bioacoustics references, and an acknowledgement of our dataset source. Symantec pam basics : the modules in this course cover a wide range of foundational information, including overviews of essential symantec pam concepts, upgrade best practices, and how to plan and implement a high availability pam cluster.
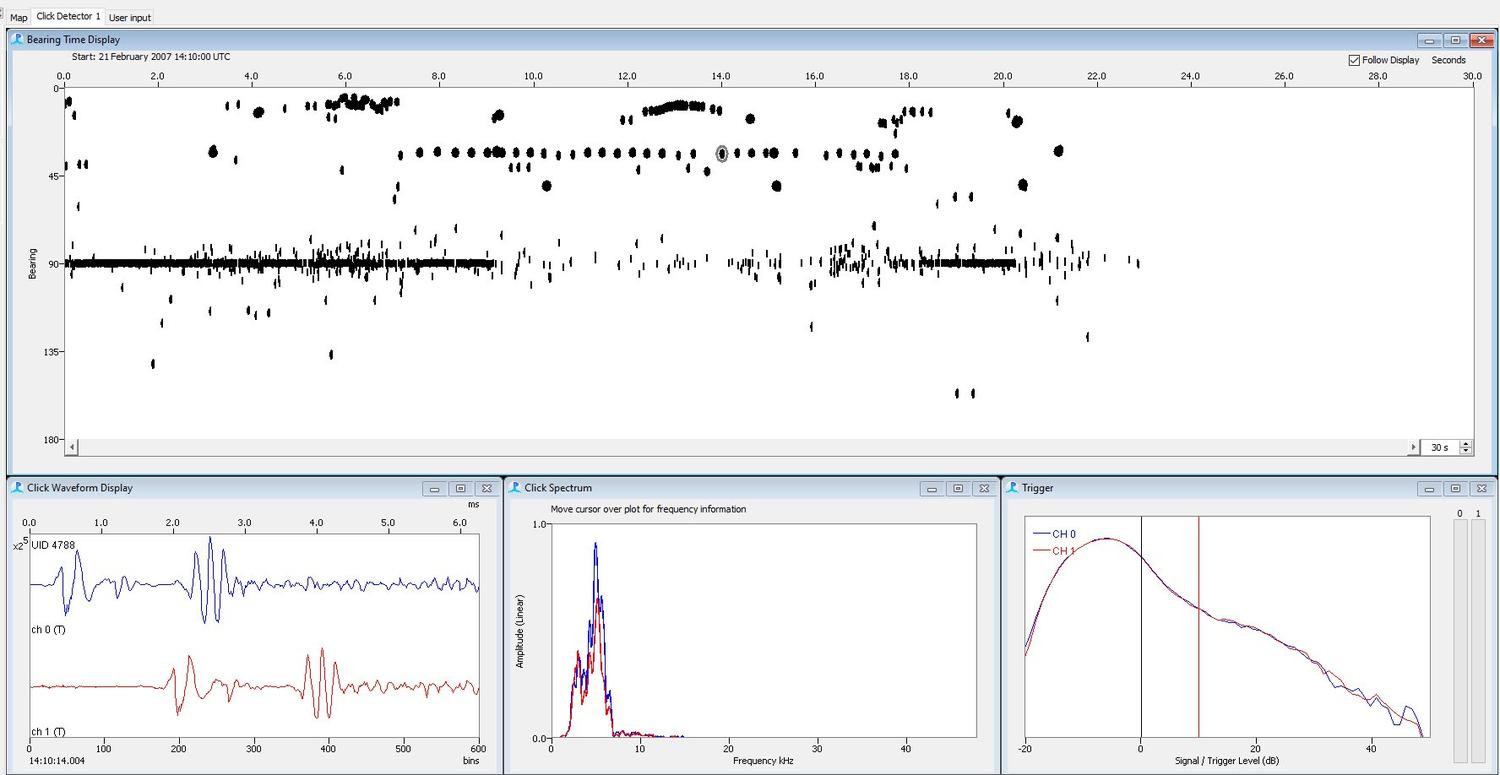
Pam Software Basics Course Resources Learn how manageengine pam360 privileged access management solution tackle your everyday privileged access security challenges and fortify your privileged data against misuse and emerging threats. join now!. Learn how modern pam solutions are structured, how they integrate with enterprise environments, and how organizations can leverage them to enhance security, enforce least privilege policies, and ensure compliance. You'll learn what pam is, why it's essential for system security, and how to configure pam files. this includes understanding file formats, module interfaces, control flags, and modules. Osa’s “pam software basics” is a fully online technical training course that introduces participants to the fundamental features of two widely used software programs in passive acoustic analysis and monitoring: raven lite and pamguard.
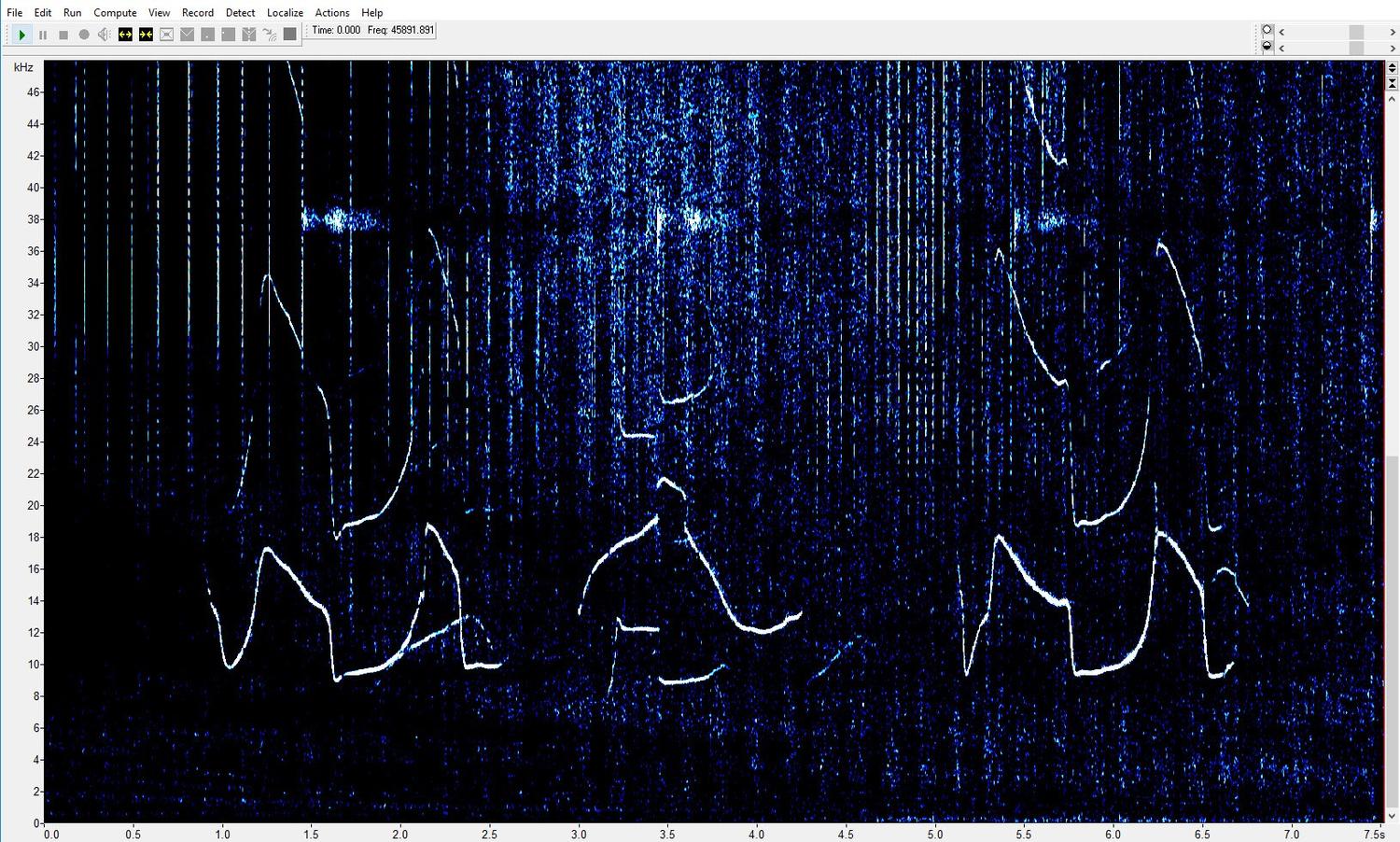
Pam Software Basics Course Resources You'll learn what pam is, why it's essential for system security, and how to configure pam files. this includes understanding file formats, module interfaces, control flags, and modules. Osa’s “pam software basics” is a fully online technical training course that introduces participants to the fundamental features of two widely used software programs in passive acoustic analysis and monitoring: raven lite and pamguard. This learning path provides cybersecurity professionals with the knowledge and skills to implement, secure, and manage privileged access management (pam) solutions. In the privileged access management (pam) course, students will learn what pam is, why it is used, and best practices for its uses. with hands on labs, students will gain skills needed to ensure the security of access to an organization’s privileged information. Whether you're new to passive acoustic monitoring or looking to refine your skills, this updated course will provide hands on training using two industry leading software tools. This course can help you understand the overall pam solution from an administrator’s perspective and equip you to efficiently perform regular access management activities.

Pam Software Basics Course Resources This learning path provides cybersecurity professionals with the knowledge and skills to implement, secure, and manage privileged access management (pam) solutions. In the privileged access management (pam) course, students will learn what pam is, why it is used, and best practices for its uses. with hands on labs, students will gain skills needed to ensure the security of access to an organization’s privileged information. Whether you're new to passive acoustic monitoring or looking to refine your skills, this updated course will provide hands on training using two industry leading software tools. This course can help you understand the overall pam solution from an administrator’s perspective and equip you to efficiently perform regular access management activities.

Pam Complete Pdf Machine Learning Spss Whether you're new to passive acoustic monitoring or looking to refine your skills, this updated course will provide hands on training using two industry leading software tools. This course can help you understand the overall pam solution from an administrator’s perspective and equip you to efficiently perform regular access management activities.

Basic Pam Pdf
Comments are closed.