Padding En V2 Pdf Cryptography Encryption

Encryption Pdf 2 Download Free Pdf Cryptography Key Cryptography Padding en v2 free download as pdf file (.pdf), text file (.txt) or view presentation slides online. padding is a cryptographic technique that modifies plaintext before encryption to achieve certain goals. In this section, we construct tailored padding schemes with which one can apply a combination of tdps to a single padded message to achieve encryption, signature, or both in the form of a signcryption primitive.

Lab1 Encryption Pdf Key Cryptography Cryptography In public key cryptography, padding is the process of preparing a message for encryption or signing using a specification or scheme such as pkcs#1 v2.2, oaep, pss, pssr, ieee p1363 emsa2 and emsa5. With this technical guideline, the federal office for information security (bsi) provides an assessment of the security and long term orientation for selected cryptographic mechanisms. In cryptography, optimal asymmetric encryption padding (oaep) is a padding scheme often used together with rsa encryption. oaep was introduced by bellare and rogaway,[1] and subsequently standardized in pkcs#1 v2 and rfc 2437. We discuss data con dentiality, data integrity, and the important concept of authenticated en cryption. part ii develops the concepts of public key encryption and digital signatures, which allow alice and bob to communicate securely, without having a pre shared secret key.

Padding Cryptography Semantic Scholar In cryptography, optimal asymmetric encryption padding (oaep) is a padding scheme often used together with rsa encryption. oaep was introduced by bellare and rogaway,[1] and subsequently standardized in pkcs#1 v2 and rfc 2437. We discuss data con dentiality, data integrity, and the important concept of authenticated en cryption. part ii develops the concepts of public key encryption and digital signatures, which allow alice and bob to communicate securely, without having a pre shared secret key. Public key cryptography based on the rsa algorithm, covering cryptographic primitives, encryption schemes, signature schemes with appendix, and asn.1 syntax for representing keys and for identifying the schemes. this document represents a republication of pkcs #1 v2.2 from rsa laboratories' public key cryptography standards (pkcs) series. by. Section 2 summarizes rsa optimal asymmetric encryption padding as de ned in pkcs #1 v2.0 . section 3 describes a chosen ciphertext against this algorithm. section 4 explores the practicality of the assumptions necessary for is standardized in ieee 1363, where the relevant message en coding method for encryption is called. 1 introduction henbacher presented an adaptive chosen cipher text attack against pkcs #1 v1.5 rsa blo k type 2 padding [1]. the attack needs roughly one million oracle queries to succeed for a 1024 bit rsa key. he concluded that rsa encryption should include an integrity check and that the phase between decryption and inte. Pdf encryption makes use of rc4 and aes algorithms with different key length. pypdf supports all of them until pdf 2.0, which is the latest pdf standard. pypdf use an extra dependency to do encryption or decryption for aes algorithms.
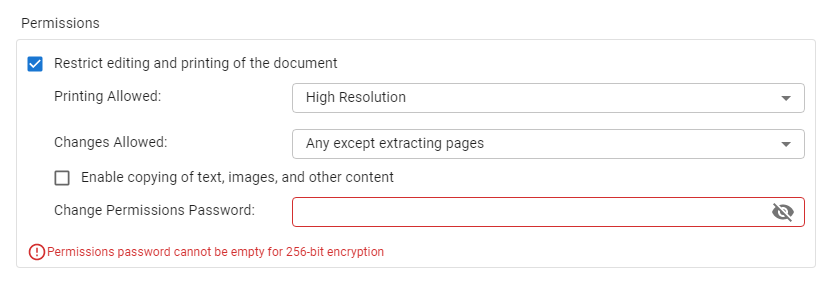
How To Specify Encryption For A Pdf Visual Paradigm Blog Public key cryptography based on the rsa algorithm, covering cryptographic primitives, encryption schemes, signature schemes with appendix, and asn.1 syntax for representing keys and for identifying the schemes. this document represents a republication of pkcs #1 v2.2 from rsa laboratories' public key cryptography standards (pkcs) series. by. Section 2 summarizes rsa optimal asymmetric encryption padding as de ned in pkcs #1 v2.0 . section 3 describes a chosen ciphertext against this algorithm. section 4 explores the practicality of the assumptions necessary for is standardized in ieee 1363, where the relevant message en coding method for encryption is called. 1 introduction henbacher presented an adaptive chosen cipher text attack against pkcs #1 v1.5 rsa blo k type 2 padding [1]. the attack needs roughly one million oracle queries to succeed for a 1024 bit rsa key. he concluded that rsa encryption should include an integrity check and that the phase between decryption and inte. Pdf encryption makes use of rc4 and aes algorithms with different key length. pypdf supports all of them until pdf 2.0, which is the latest pdf standard. pypdf use an extra dependency to do encryption or decryption for aes algorithms.
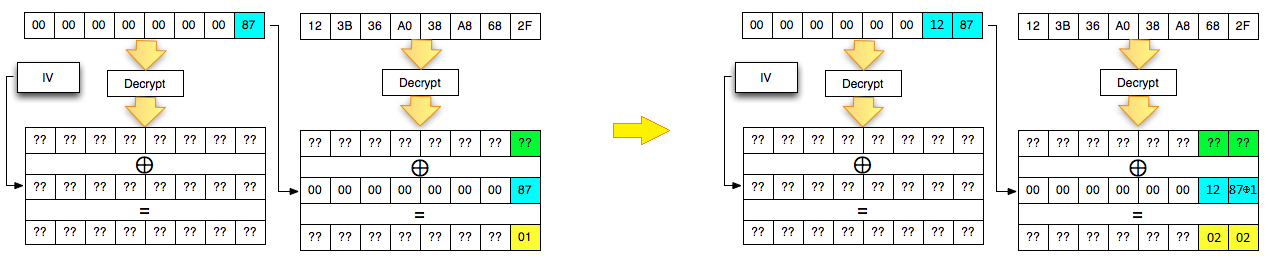
Cryptography 1 introduction henbacher presented an adaptive chosen cipher text attack against pkcs #1 v1.5 rsa blo k type 2 padding [1]. the attack needs roughly one million oracle queries to succeed for a 1024 bit rsa key. he concluded that rsa encryption should include an integrity check and that the phase between decryption and inte. Pdf encryption makes use of rc4 and aes algorithms with different key length. pypdf supports all of them until pdf 2.0, which is the latest pdf standard. pypdf use an extra dependency to do encryption or decryption for aes algorithms.
Comments are closed.