Package Manager Bakapps Cyber Security
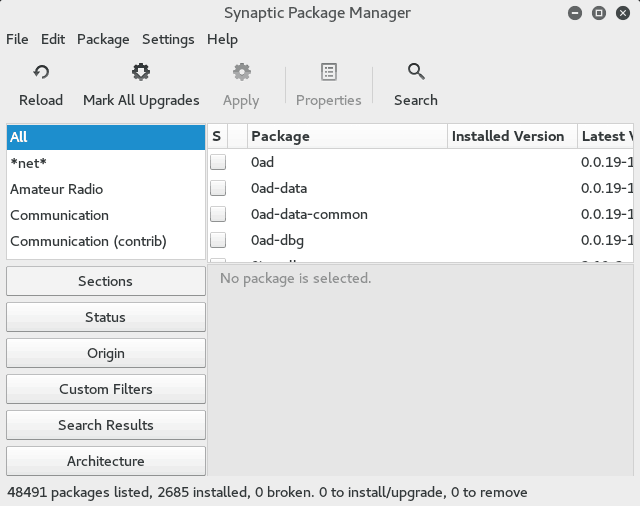
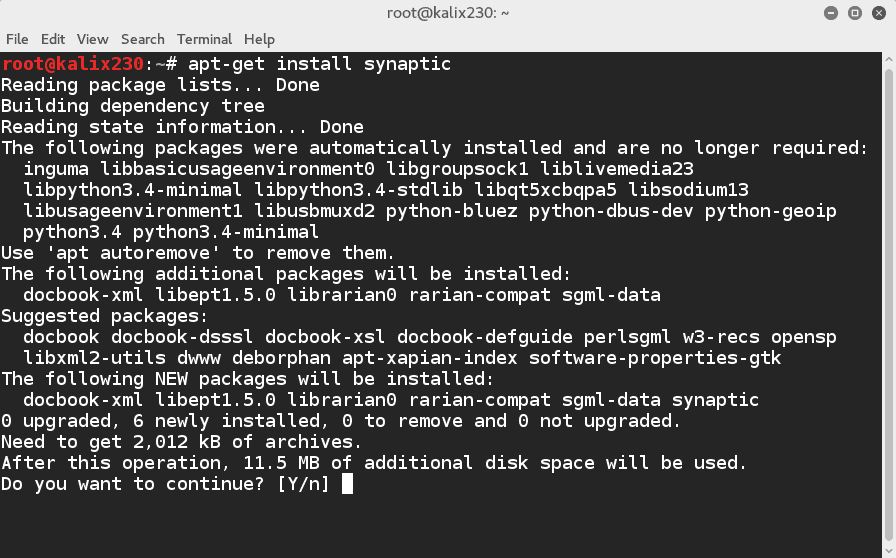
Package Manager Bakapps Cyber Security One package that i install on every kali installation is synaptic package manager. it is a gui based utility that lets me search for packages across a variety of repositories and install them with two clicks. This document focuses on how developers can securely use package managers as part of their software development life cycle.

Package Manager Bakapps Cyber Security Tackle the complexities of securing software packages, managing vulnerabilities, creating security policies, and meeting compliance standards using package security manager. Learn about package manager dependencies of hidden security risks, common risks in npm and pip dependencies, and how to protect your projects from malicious packages. Enisa technical advisory on package managers explains package manager security risks and how dependency chains expand attack surfaces. We analyzed security properties of package managers, and we uncovered several design level vulnerabilities. to demonstrate the seriousness of these issues, we con structed an automated end to end attack tool against cpan, the popular package manager for perl.
Package Manager Bakapps Cyber Security Enisa technical advisory on package managers explains package manager security risks and how dependency chains expand attack surfaces. We analyzed security properties of package managers, and we uncovered several design level vulnerabilities. to demonstrate the seriousness of these issues, we con structed an automated end to end attack tool against cpan, the popular package manager for perl. The european union agency for cybersecurity (enisa) has released its inaugural technical advisory on the secure use of package managers, offering guidance to developers on safely integrating third party code into their projects. There are essentially two main ways an attacker can use — metadata replay and mirror control. the underlying method in both these ways is that instead of a legitimate repository of distribution. Package managers, however prevalent, feel as if they are still infants in terms of security, considering the various supply chain attacks we have seen in the previous few years. By understanding and utilizing package managers, you can ensure that your system remains secure, stable, and up to date. this lecture has provided an overview of the key concepts and tasks involved in package management, setting the stage for more detailed exploration in subsequent lectures.
Comments are closed.