Open Source Software Security Fluid Attacks

Open Source Software Security Fluid Attacks Fluid attacks publishes all its application source code as open source on gitlab for auditability, transparency, and code quality assurance. Fluid attacks is an all in one aspm platform combining sast, dast, sca, cspm, ai, and pentesters to find, prioritize, and fix real appsec risks. a software supply chain framework powered by nix. high performance functions to work with the async io.

Application Security Testing Solutions Fluid Attacks Fluid attacks was founded in 2001 by mauricio gómez, rafael Álvarez, david cardona, and luis bustamante, initially under the name fluidsignal. the company began by providing the setup of secure networks, mainly based on linux. Project summary master repository of all oss tools built and maintained by fluid attacks. fluid attacks is a colombian company. most products are distributed as a standalone binary: * asserts * forces * melts * reviews * skims additional instructions may be available on the specific product documentation. The tool provides detailed mappings of dependency trees to visualize component relationships and continuously scans for known vulnerabilities in open source and third party components. Uncover 13 security risks in open source software and learn best practices for managing and securing open source dependencies.
Blog Seguridad En Aplicaciones Fluid Attacks The tool provides detailed mappings of dependency trees to visualize component relationships and continuously scans for known vulnerabilities in open source and third party components. Uncover 13 security risks in open source software and learn best practices for managing and securing open source dependencies. 💬 on our subprocessors: for fluid attacks, transparency is a fundamental principle of security. that is why, in the area of customer data management, we would like to inform you that we have now subscribed to the cloud monitoring subprocessor datadog and are no longer using coralogix and mixpanel. Fluid attacks' solutions enable organizations to identify, prioritize, and remediate vulnerabilities in their software throughout the sdlc. supported by ai, automated tools, and pentesters, fluid attacks accelerates companies' risk exposure mitigation and strengthens their cybersecurity posture. The fluid attacks scanner does software composition analysis, sca, a technique for detecting open source packages with security vulnerabilities in applications. Explore the fluid attacks arsenal of pentesting tools. used for network scanning, exploit development, etc., these tools power manual security assessments.
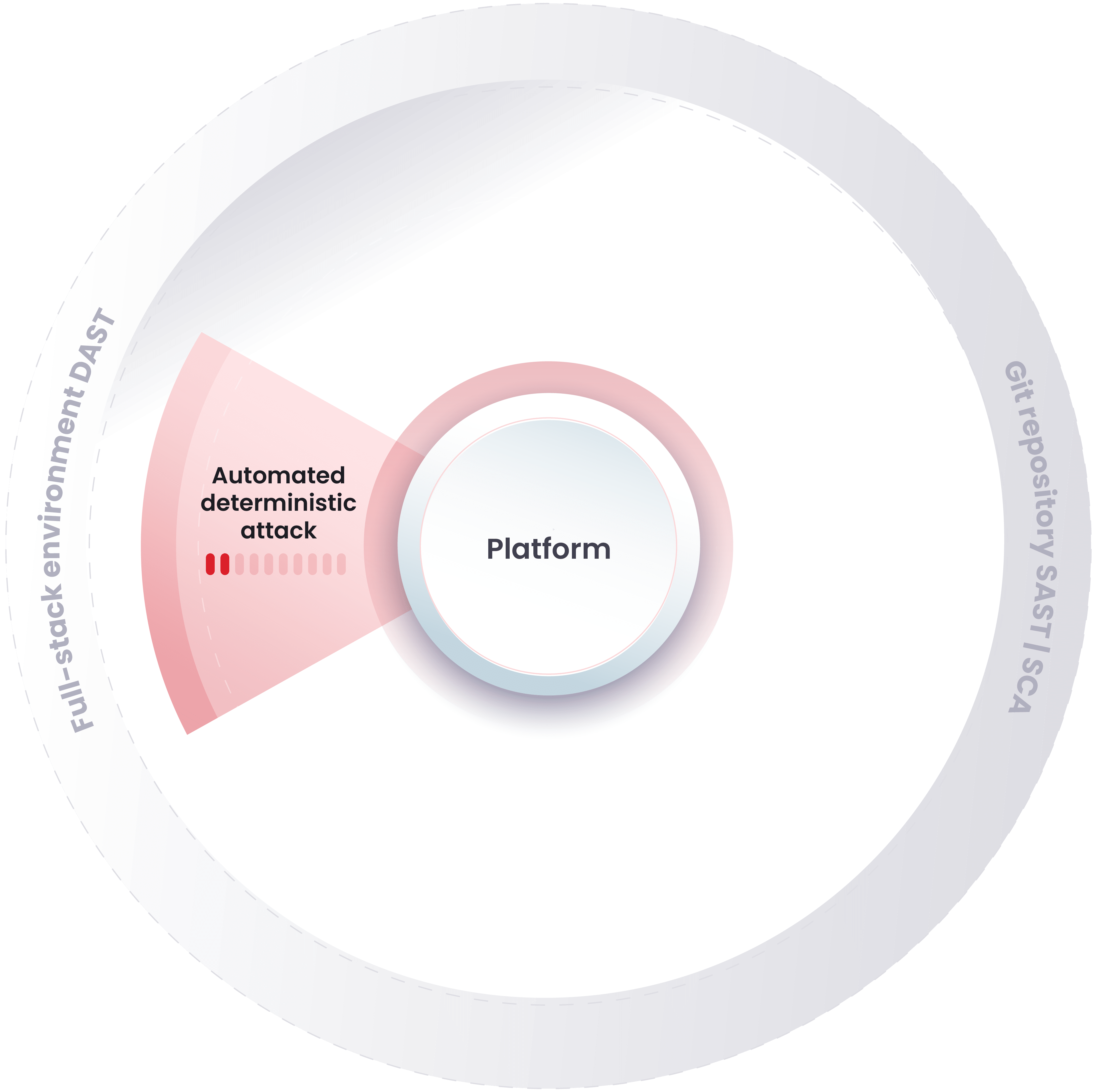
Application Security Testing Solutions Fluid Attacks 💬 on our subprocessors: for fluid attacks, transparency is a fundamental principle of security. that is why, in the area of customer data management, we would like to inform you that we have now subscribed to the cloud monitoring subprocessor datadog and are no longer using coralogix and mixpanel. Fluid attacks' solutions enable organizations to identify, prioritize, and remediate vulnerabilities in their software throughout the sdlc. supported by ai, automated tools, and pentesters, fluid attacks accelerates companies' risk exposure mitigation and strengthens their cybersecurity posture. The fluid attacks scanner does software composition analysis, sca, a technique for detecting open source packages with security vulnerabilities in applications. Explore the fluid attacks arsenal of pentesting tools. used for network scanning, exploit development, etc., these tools power manual security assessments.
Comments are closed.