Nis2 Compliance A Step By Step Guide For Companies
Nis2 Compliance Guide For Ot Systems Final Pdf Computer Security This nis2 checklist is your practical guide to achieving full compliance with the eu’s updated cybersecurity directive. whether you’re an essential entity, a key supplier, or just preparing for legal alignment, our 10 step breakdown simplifies your path to nis2 compliance. This comprehensive guide transforms nis2’s complex regulatory framework into a practical, step by step compliance checklist that empowers organizations to achieve certification efficiently while building robust cybersecurity foundations that extend beyond mere regulatory compliance.
Nis2 Compliance A Step By Step Guide For Companies Companies required to meet these standards face the challenge of adapting their processes and systems accordingly. here is a guide that will show you the basic step by step steps to meet nis2 requirements. Looking for an in depth guide to nis2 compliance? we've reviewed the legislation and created a checklist to better prepare for the new eu directive. Checklist nis2 compliance this nis2 compliance checklist provides a step by step best practices guide to help organisations streamline their nis2 compliance journey and position themselves. This guide provides a step by step approach to achieving nis2 compliance in practice – from scope assessment and determining your cybersecurity maturity level through a self assessment, to a structured overview of all statutory nis2 requirements, including a comprehensive compliance checklist.

The Nis2 Directive A Step By Step Compliance Guide Checklist nis2 compliance this nis2 compliance checklist provides a step by step best practices guide to help organisations streamline their nis2 compliance journey and position themselves. This guide provides a step by step approach to achieving nis2 compliance in practice – from scope assessment and determining your cybersecurity maturity level through a self assessment, to a structured overview of all statutory nis2 requirements, including a comprehensive compliance checklist. The following 13 steps provide an overview of the nis2 implementing regulations to help you establish robust cybersecurity measures, manage risks, and maintain business continuity. Your supply chain should be included in your risk assessment to evaluate your suppliers’ security level and con rm you can identify them as nis2 compliant vendors. 5. technical compliance and certifications ensure the use of multi factor authentication and secured communication systems for critical services, including voice, video, and text communications, especially for remote or privileged access. With its stringent requirements for managing cyber risks, securing supply chains, and reporting incidents, it’s essential for organizations to ensure compliance. this article outlines the crucial steps for aligning with nis2 standards, drawn from our comprehensive nis2 compliance checklist.
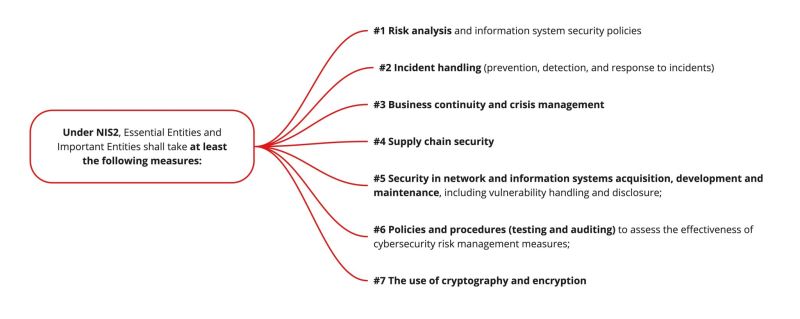
Yogosha On Linkedin Nis2 Directive Step By Step Guide To Compliance The following 13 steps provide an overview of the nis2 implementing regulations to help you establish robust cybersecurity measures, manage risks, and maintain business continuity. Your supply chain should be included in your risk assessment to evaluate your suppliers’ security level and con rm you can identify them as nis2 compliant vendors. 5. technical compliance and certifications ensure the use of multi factor authentication and secured communication systems for critical services, including voice, video, and text communications, especially for remote or privileged access. With its stringent requirements for managing cyber risks, securing supply chains, and reporting incidents, it’s essential for organizations to ensure compliance. this article outlines the crucial steps for aligning with nis2 standards, drawn from our comprehensive nis2 compliance checklist.

Guide To Nis2 Compliance 5. technical compliance and certifications ensure the use of multi factor authentication and secured communication systems for critical services, including voice, video, and text communications, especially for remote or privileged access. With its stringent requirements for managing cyber risks, securing supply chains, and reporting incidents, it’s essential for organizations to ensure compliance. this article outlines the crucial steps for aligning with nis2 standards, drawn from our comprehensive nis2 compliance checklist.
Comments are closed.