Networking Ssh Secure Shell Youtube
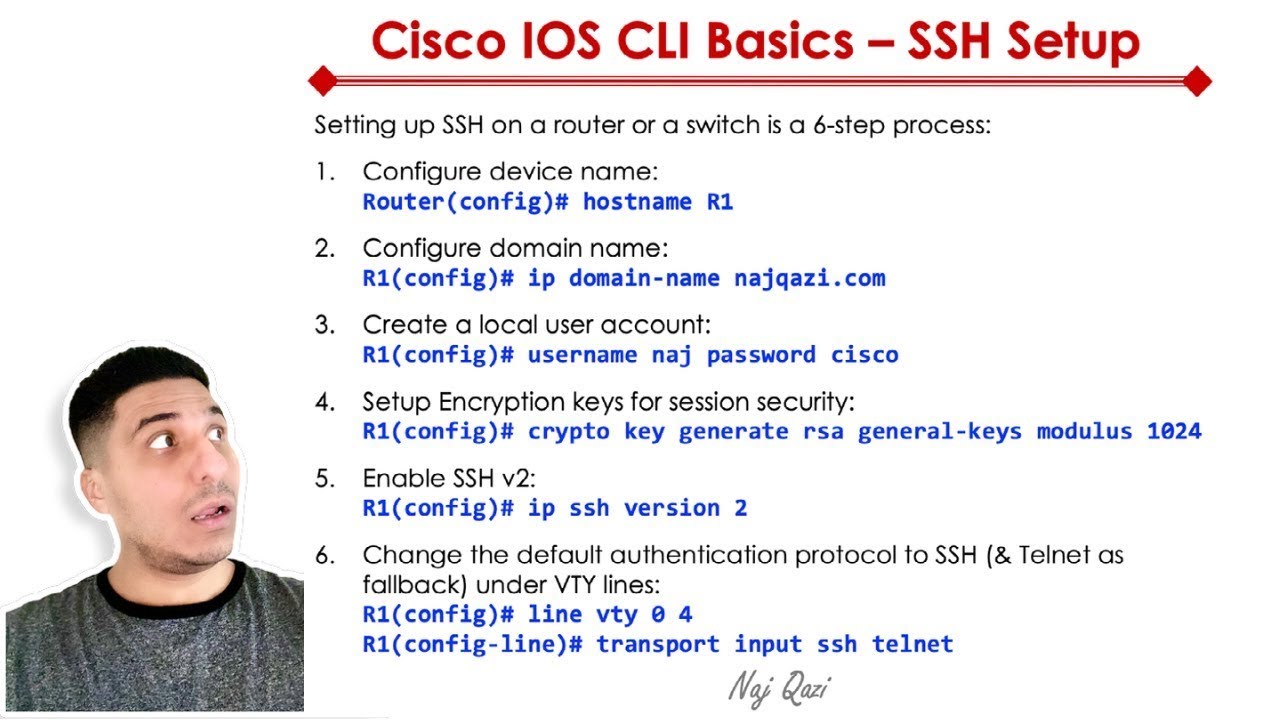
Secure Shell Ssh Overview And Configuration Youtube To allow only one ssh keyholder ensure you have the user's public key at home username .ssh authorized keys (with correct perms and owned by the user), then: passwordauthentication no. Ssh authenticates you using public key cryptography. you create a pair of keys: a private key that resides on your client computer and a public key that your dropbox server uses.
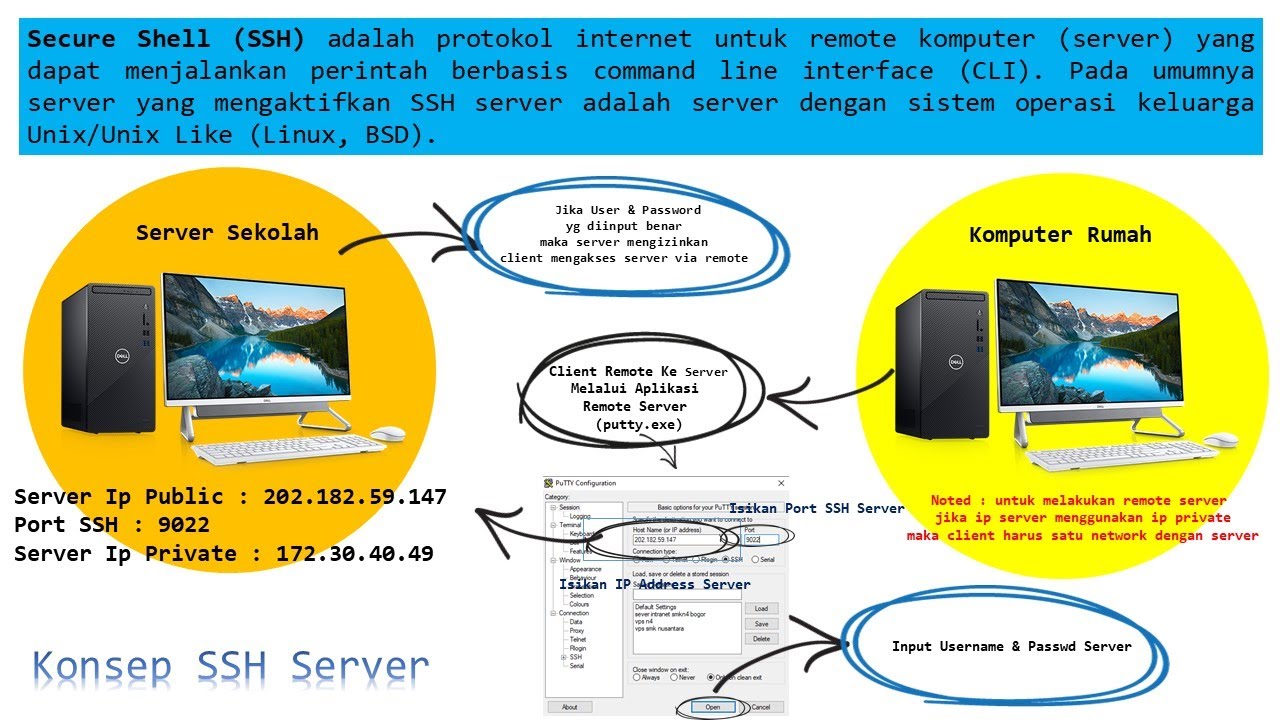
Konsep Ssh Secure Shell Server Youtube Ssh is a powerful and secure tool for remote communication and management. as a beginner, understanding how to use ssh will open up a world of possibilities in managing remote servers, transferring files, and deploying applications securely. This wikihow article will teach you how to install an ssh client on windows (as linux and macos already have ssh), and how to connect to a remote host with a secure shell. Learn how to use ssh to securely connect to a remote server. this step by step guide covers setup, syntax, key auth, troubleshooting, and best practices. Start with this beginner friendly ssh tutorial to manage servers securely and confidently. you’ll learn what ssh is, how it works, and how to log in on macos, linux, or windows. the guide covers generating and protecting ssh keys, creating strong passphrases, and using shell commands for real tasks.
Secure Shell Ssh Kelompok 13 Youtube Learn how to use ssh to securely connect to a remote server. this step by step guide covers setup, syntax, key auth, troubleshooting, and best practices. Start with this beginner friendly ssh tutorial to manage servers securely and confidently. you’ll learn what ssh is, how it works, and how to log in on macos, linux, or windows. the guide covers generating and protecting ssh keys, creating strong passphrases, and using shell commands for real tasks. This guide provides an in depth overview of ssh, including its configuration, public private key based authentication, advanced features, x11 forwarding, and best practices for secure usage. We need ssh (secure shell) because it allows us to securely log into our servers over the network. this is a step by step walkthrough that goes beyond just the commands. In this ssh tutorial, we will learn how ssh works and the various mechanisms that it utilizes to securely encrypt a connection. The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption.
What Is Ssh Secure Shell Youtube This guide provides an in depth overview of ssh, including its configuration, public private key based authentication, advanced features, x11 forwarding, and best practices for secure usage. We need ssh (secure shell) because it allows us to securely log into our servers over the network. this is a step by step walkthrough that goes beyond just the commands. In this ssh tutorial, we will learn how ssh works and the various mechanisms that it utilizes to securely encrypt a connection. The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption.
Comments are closed.