Networking Security Cisco Border Gateway Protocol Bgp Neighbors

Cisco Bgp Border Gateway Protocol Training Edu Lowcostlivin This section describes how to configure the firewall threat defense to route data, perform authentication, and redistribute routing information using the border gateway protocol (bgp). A group of one or more ip prefixes (lists of ip addresses accessible on a network) run by one or more network operators that maintain a single, clearly defined routing policy.
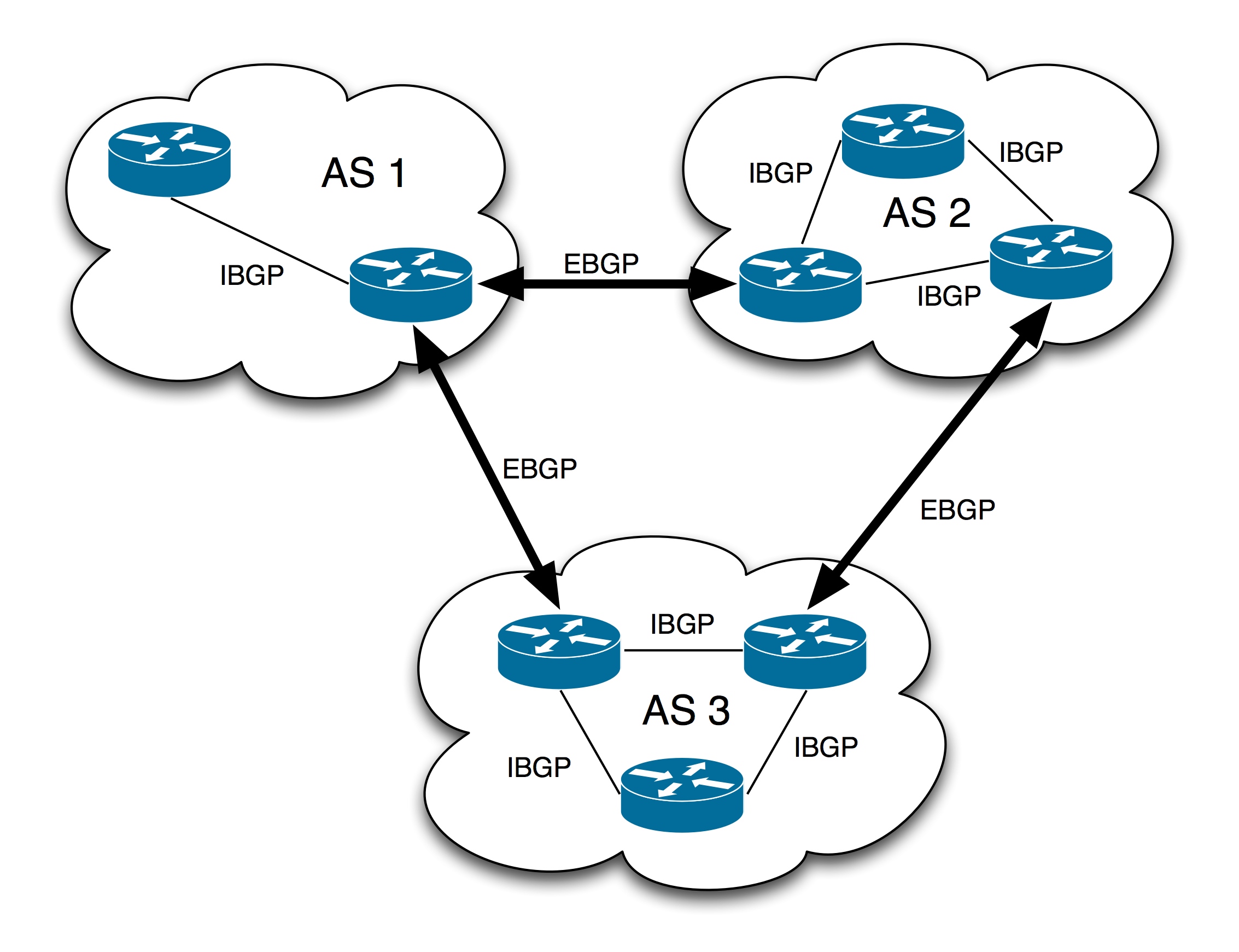
Bgp Border Gateway Protocol Bgp Optimale Routen Reflektion Cisco Importance of border gateway protocol (bgp) security: bgp is highly secure because it authenticates messages between routers using preconfigured passwords through which unauthorized traffic is filtered out. The security & sd wan > configure > routing settings page can be used to configure ebgp neighbors when bgp is toggled to enabled. to configure one, click "add a bgp neighbor," then configure the neighbor ip and remote as and source interface. When bgp runs between two peers in the same autonomous system (as), it is referred to as internal bgp (ibgp or interior border gateway protocol). when it runs between different autonomous systems, it is called external bgp (ebgp or exterior border gateway protocol). This document provides technical guidance and recommendations to improve the security and resilience of internet routing based on bgp.
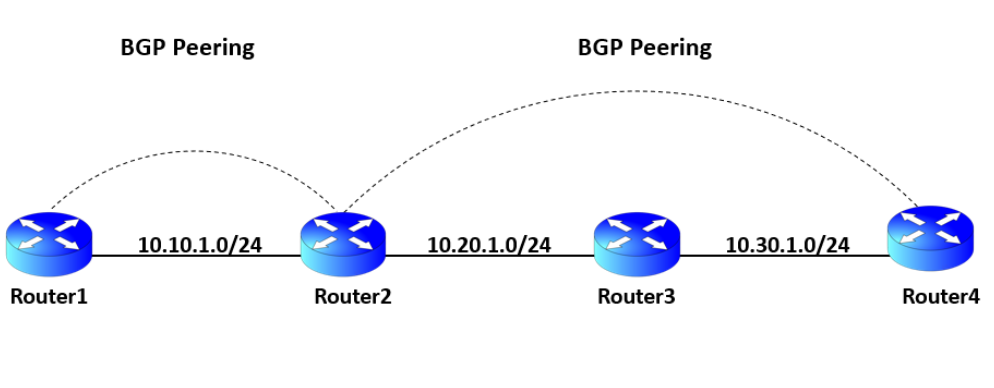
What Is Border Gateway Protocol Bgp When bgp runs between two peers in the same autonomous system (as), it is referred to as internal bgp (ibgp or interior border gateway protocol). when it runs between different autonomous systems, it is called external bgp (ebgp or exterior border gateway protocol). This document provides technical guidance and recommendations to improve the security and resilience of internet routing based on bgp. Border gateway protocol (bgp) is the fundamental routing protocol that is used on the internet. like most routing protocols, bgp depends upon the creation of neighbor adjacencies between bgp routers to exchange prefixes and routing information. Here is a guide for best practices for enhancing and securing border gateway protocol (bgp) with cisco and juniper hardware. In this post, i am going to cover a set of bgp configuration scenarios that will provide you with a good understanding of how to configure border gateway protocol on cisco routers. Your bgp security depends on thousands of networks implementing validation controls. start with what you can control: deploy rpki rov in enforcement mode, filter prefixes strictly at every peering point, and integrate bgp monitoring into your soc workflows.

Bgp Neighbor States Pdf Transmission Control Protocol Internet Border gateway protocol (bgp) is the fundamental routing protocol that is used on the internet. like most routing protocols, bgp depends upon the creation of neighbor adjacencies between bgp routers to exchange prefixes and routing information. Here is a guide for best practices for enhancing and securing border gateway protocol (bgp) with cisco and juniper hardware. In this post, i am going to cover a set of bgp configuration scenarios that will provide you with a good understanding of how to configure border gateway protocol on cisco routers. Your bgp security depends on thousands of networks implementing validation controls. start with what you can control: deploy rpki rov in enforcement mode, filter prefixes strictly at every peering point, and integrate bgp monitoring into your soc workflows.
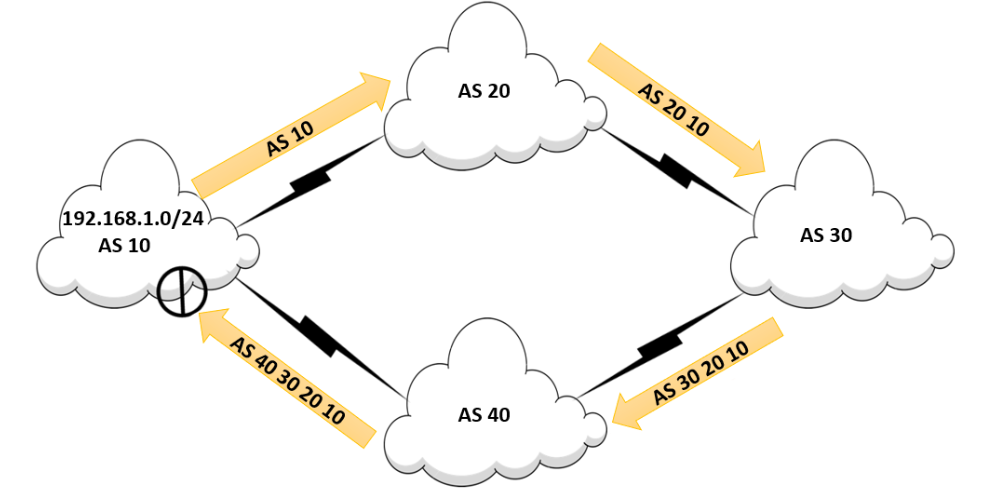
Border Gateway Protocol Bgp Routing Overview Study Ccnp In this post, i am going to cover a set of bgp configuration scenarios that will provide you with a good understanding of how to configure border gateway protocol on cisco routers. Your bgp security depends on thousands of networks implementing validation controls. start with what you can control: deploy rpki rov in enforcement mode, filter prefixes strictly at every peering point, and integrate bgp monitoring into your soc workflows.
Border Gateway Protocol Bgp Routing Overview Study Ccnp
Comments are closed.