Network What Is Ssh Protocol
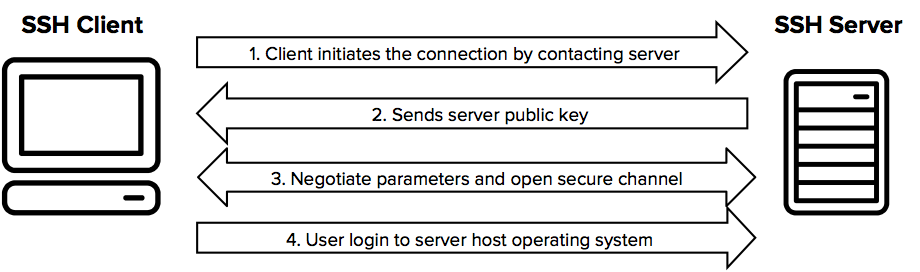
Ssh Protocol Is The Standard For Strong Authentication Secure Ssh (secure shell) is a network protocol that establishes encrypted connections between computers for secure remote access. it operates on tcp port 22 and provides authentication, encryption, and integrity to protect data transmitted over unsecured networks. The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution.
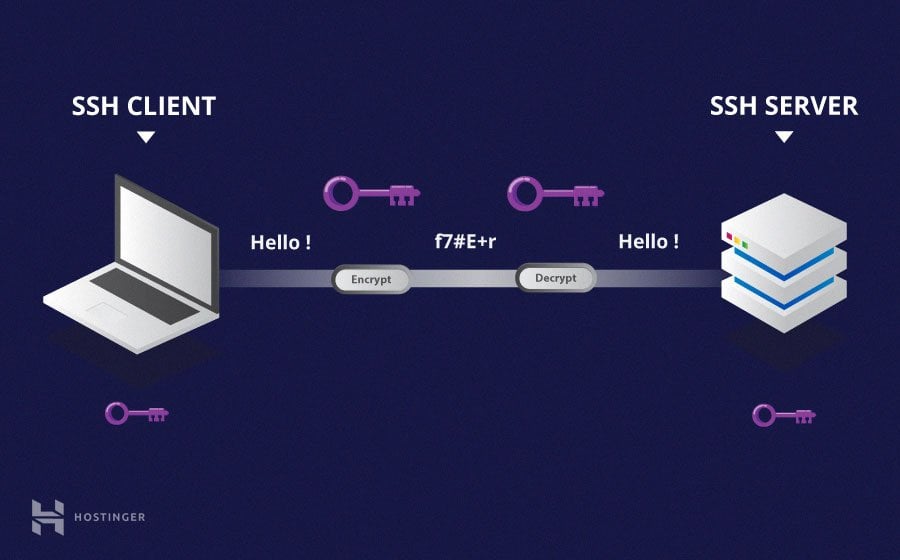
Secure Shell Protocol Ssh Msblab The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption. Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. Ssh (short for secure shell) is a network protocol that provides a secure way for two computers to connect remotely. ssh employs encryption to ensure that hackers cannot interpret the traffic between two connected devices.

Ssh Protocol Explained N Able Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. Ssh (short for secure shell) is a network protocol that provides a secure way for two computers to connect remotely. ssh employs encryption to ensure that hackers cannot interpret the traffic between two connected devices. If you’ve ever needed to remotely access or manage a server, chances are you’ve used ssh (secure shell). ssh is the go to protocol for securely connecting to machines over a network, allowing for. Ssh uses this technique to authenticate users and securely exchange keys without exposing sensitive information. public key is shared openly, while the private key remains secret. The secure shell (ssh) protocol is a fundamental technology for secure remote access and communication over unsecured networks. established in the mid 1990s, ssh was developed to replace older, less secure protocols such as telnet and ftp, which transmitted data, including passwords, in plain text. Ssh stands for secure shell. ssh is a network protocol used to secure communication between remote devices over an unsecured connection. ssh is a solution that provides strong end to end encryption, secure authentication, and encrypted data transmission and reception.
Comments are closed.