Network Mobile Network Forensic Pdf Computer Network Digital

Network Forensic Pdf Computer Network Security Network & mobile network forensic free download as pdf file (.pdf), text file (.txt) or read online for free. the document outlines the curriculum for digital forensics, specifically focusing on network forensics and its methodologies, tools, and processes. However, the popularity of computer and mobile networking brings various drawbacks mostly associated with security and data breaches.
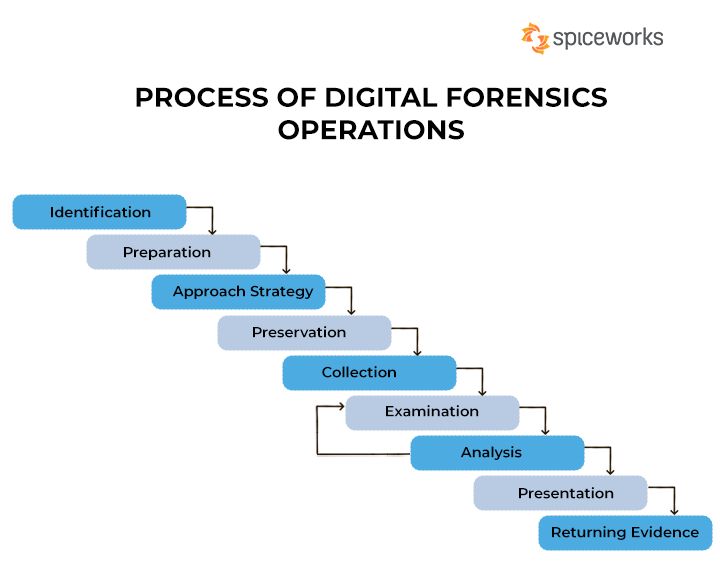
What Is Digital Forensic Methodology Or Process Darwin S Data This guide provides basic information on mobile forensics tools and the preservation, acquisition, examination and analysis, and reporting of digital evidence present on mobile devices. As a mobile digital forensic investigator, you are expected to have a working understanding of smart cards file management. this will help you explain how artifacts are stored on and extracted from u sim cards. Key topics include cybercrime investigations, incident response, privacy protection, chain of custody, and professional conduct. the handbook also covers tools, file systems, network forensics, malware analysis, mobile device forensics, and emerging challenges in the field. Digital forensics techniques play an essential role in investigation since more and more people are using mobile devices. the techniques can be described in file system, creating an evidence and how the data can be acquired.

Essential Guide To The Digital Forensics Process Fidelis Security Key topics include cybercrime investigations, incident response, privacy protection, chain of custody, and professional conduct. the handbook also covers tools, file systems, network forensics, malware analysis, mobile device forensics, and emerging challenges in the field. Digital forensics techniques play an essential role in investigation since more and more people are using mobile devices. the techniques can be described in file system, creating an evidence and how the data can be acquired. Abstract evices in contemporary society has revolutionized communication, commerce, and social interaction. with this widespread adoption of mobile technology comes the need for robust digital forensic methodologies. The mobile forensics process aims to recover digital evidence from a mobile device in a way that will preserve the evidence in a forensically sound condition. this evidence might be used to prove being a cybercriminal or a cybercrime victim. While intrusion detection helps strengthen and improve a computer network’s security, network forensics is primarily associated with the need to identify the evidence related to a security breach. Network forensics is a branch of digital forensics focused on monitoring and analyzing computer network traffic for information gathering, legal evidence or intrusion detection.
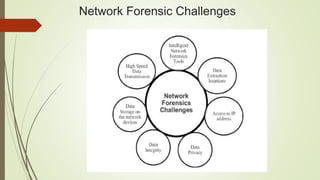
Network Forensic Pptx Abstract evices in contemporary society has revolutionized communication, commerce, and social interaction. with this widespread adoption of mobile technology comes the need for robust digital forensic methodologies. The mobile forensics process aims to recover digital evidence from a mobile device in a way that will preserve the evidence in a forensically sound condition. this evidence might be used to prove being a cybercriminal or a cybercrime victim. While intrusion detection helps strengthen and improve a computer network’s security, network forensics is primarily associated with the need to identify the evidence related to a security breach. Network forensics is a branch of digital forensics focused on monitoring and analyzing computer network traffic for information gathering, legal evidence or intrusion detection.

Pdf Comprehensive Study Of Network Forensic While intrusion detection helps strengthen and improve a computer network’s security, network forensics is primarily associated with the need to identify the evidence related to a security breach. Network forensics is a branch of digital forensics focused on monitoring and analyzing computer network traffic for information gathering, legal evidence or intrusion detection.
Comments are closed.