Network Forensic Pdf Computer Network Security

9 Computer Network And Network Security Pdf Each day, cyber related criminals explore and devise complicated means of infiltrating and exploiting individual and corporate networks' security. Charlie has developed and taught graduate level courses in network security, data communications, incident response and network forensics, and software security at several colleges and universities in the greater boston area, including boston university and brandeis university.

Network Forensic Process Model And Framework An Alternative Scenario While intrusion detection helps strengthen and improve a computer network’s security, network forensics is primarily associated with the need to identify the evidence related to a security breach. Network forensic free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses network forensics, focusing on the analysis of data packets and the importance of network log mining in investigating cybercrimes. With the rapid growth and use of internet, network forensics has become an integral part of computer forensics. this paper surveys the tools and techniques (efficient, easy to use and cost effective) available to conduct network forensics. We provide an overview of network forensic techniques, tools, and challenges and discuss analyzing network traffic to gather evidence of cyberattacks. it consists of two types of analysis which are real time and post incident.
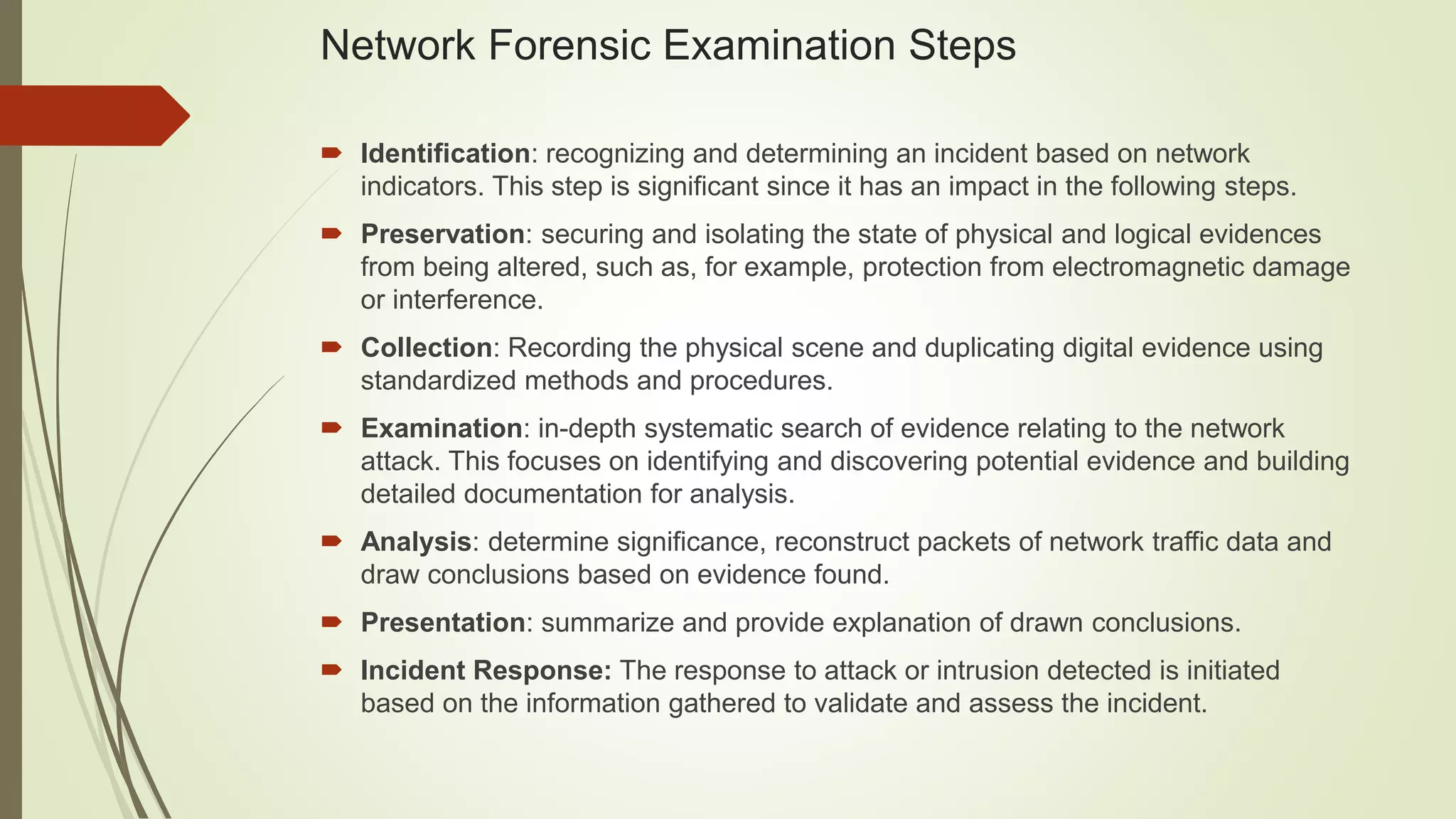
Network Forensic Pptx With the rapid growth and use of internet, network forensics has become an integral part of computer forensics. this paper surveys the tools and techniques (efficient, easy to use and cost effective) available to conduct network forensics. We provide an overview of network forensic techniques, tools, and challenges and discuss analyzing network traffic to gather evidence of cyberattacks. it consists of two types of analysis which are real time and post incident. Abbreviations: network forensics; network security; computer forensics; computer intrusion ssd: solid detection state drive and prevention systems; idip: integrated digital research process; ids: intrusion detection system;. It provides complete knowledge of network security and the cyber forensics, differentiates between network security and network forensics, defines the terminolo gies of digital forensics and compares computer forensics and network forensics. Network forensics is a sub branch of digital forensics relating to the monitoring and analysis of computer network traffic for the purposes of information gathering, legal evidence, or intrusion detection. Cyber trespass: it means to access someone’s computer or network without the right authorization of the owner and disturb, alter, misuse, or damage data or system by using wireless internet connection.

Evaluating Network Forensics Applying Advanced Tools Pdf Computer Abbreviations: network forensics; network security; computer forensics; computer intrusion ssd: solid detection state drive and prevention systems; idip: integrated digital research process; ids: intrusion detection system;. It provides complete knowledge of network security and the cyber forensics, differentiates between network security and network forensics, defines the terminolo gies of digital forensics and compares computer forensics and network forensics. Network forensics is a sub branch of digital forensics relating to the monitoring and analysis of computer network traffic for the purposes of information gathering, legal evidence, or intrusion detection. Cyber trespass: it means to access someone’s computer or network without the right authorization of the owner and disturb, alter, misuse, or damage data or system by using wireless internet connection.
What Is Network Forensic Why It Is Important Ip2location Network forensics is a sub branch of digital forensics relating to the monitoring and analysis of computer network traffic for the purposes of information gathering, legal evidence, or intrusion detection. Cyber trespass: it means to access someone’s computer or network without the right authorization of the owner and disturb, alter, misuse, or damage data or system by using wireless internet connection.

Network Forensic Pdf Computer Network Security
Comments are closed.