Nested Easter Egg Owasp Juice Shop

Introduction Pwning Owasp Juice Shop Opening the easter egg file, there’s an obvious base64 string to decode. base64 is easy to spot because it contains ‘=’ as padding. while it can also contain ‘ ’ and ‘ ’ as special characters, ‘=’ is a dead giveaway. This challenge ask us to decrypt a hidden message located within another easter egg, emphasizing advanced cryptographic analysis to uncover the real easter egg within the application.
How To Install Owasp Juice Shop In Kali Linux Owasp Juice Shop Setup Now it is time to tackle the taunt of the developers and hunt down the real easter egg. this follow up challenge is basically about finding a secret url that when accessed will reward you with an easter egg that deserves the name. Subscribed 5 692 views 1 year ago challenge apply advanced cryptanalysis to find easter egg owasp juice shop more. In this writeup i will be exploring the cryptographic challenges within owasp juice shop. while trying to read the confidential document we come across this ftp directory, which we will visit for the next section. from the ftp directory there is an interesting document titled ’eastere.gg’. In the first challenge that we did, we can download a file for this nested easter egg challengue, the easter egg file that we downloaded show us this text. so we see that it is a base64.
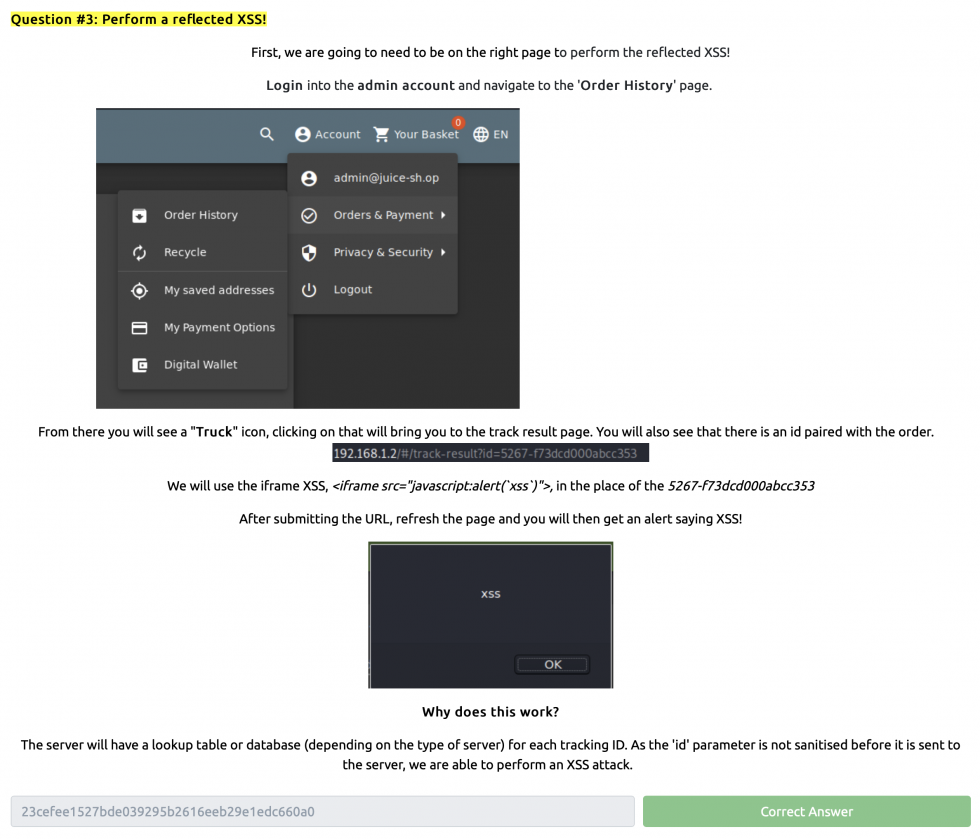
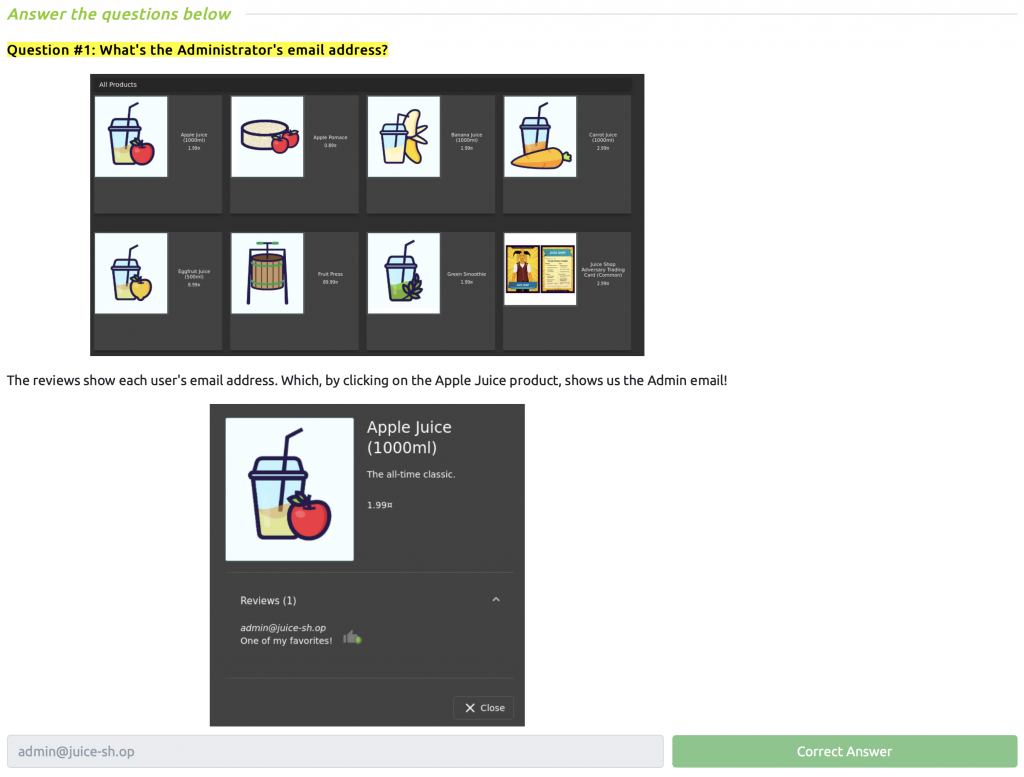
Hack The Owasp Juice Shop Tryhackme Burp Suite Fundamentals Jbc In this writeup i will be exploring the cryptographic challenges within owasp juice shop. while trying to read the confidential document we come across this ftp directory, which we will visit for the next section. from the ftp directory there is an interesting document titled ’eastere.gg’. In the first challenge that we did, we can download a file for this nested easter egg challengue, the easter egg file that we downloaded show us this text. so we see that it is a base64. It features a variety of vulnerabilities based on real world applications to help users practice hacking skills. the application is built using node.js, express, and angular, and includes challenges of different difficulty levels that users can exploit. We have to apply some advanced cryptanalysis to find the real easter egg and peel through several layers of tough as nails encryption for this challenge. as we know from previous part, hidden easter egg is hidden in ftp dir. The provided content is a comprehensive walkthrough guide for the owasp juice shop, an intentionally vulnerable web application used for security training on tryhackme, covering various owasp top 10 vulnerabilities. It can be used in security trainings, awareness demos, ctfs, and as a guinea pig for security tools! juice shop encompasses vulnerabilities from the entire owasp top ten along with many other security flaws found in real world applications.
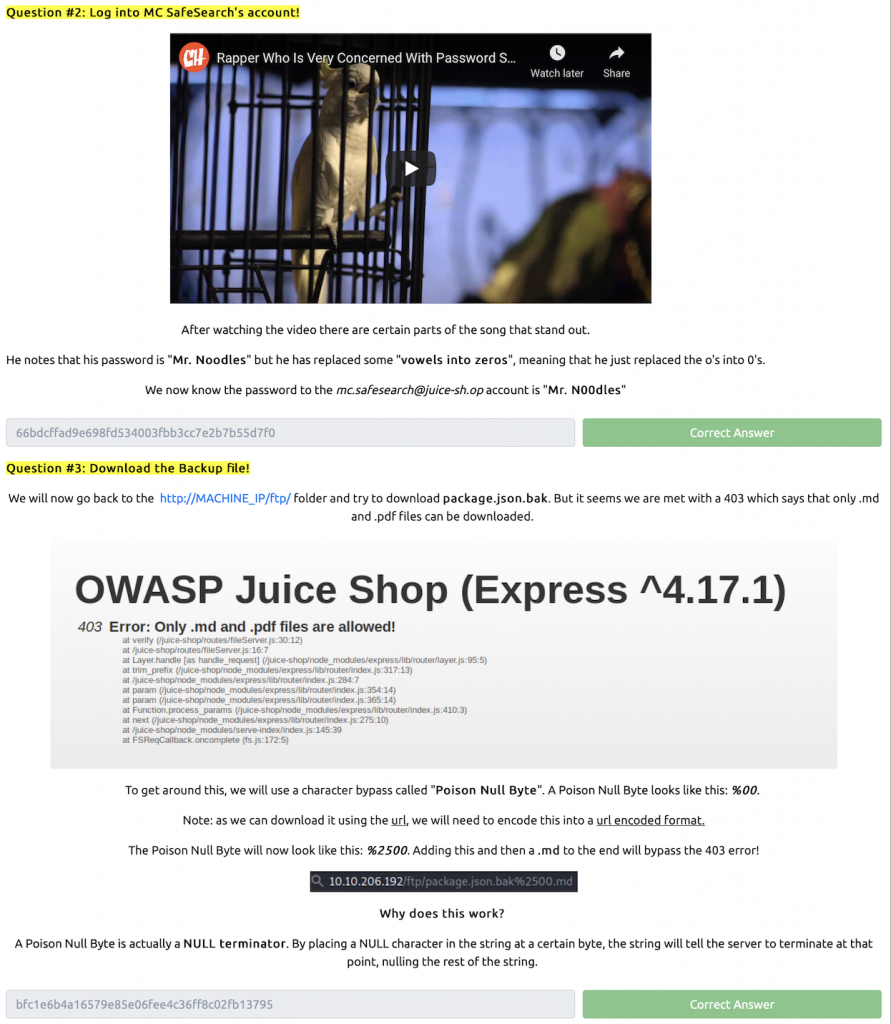
Hack The Owasp Juice Shop Tryhackme Burp Suite Fundamentals Jbc It features a variety of vulnerabilities based on real world applications to help users practice hacking skills. the application is built using node.js, express, and angular, and includes challenges of different difficulty levels that users can exploit. We have to apply some advanced cryptanalysis to find the real easter egg and peel through several layers of tough as nails encryption for this challenge. as we know from previous part, hidden easter egg is hidden in ftp dir. The provided content is a comprehensive walkthrough guide for the owasp juice shop, an intentionally vulnerable web application used for security training on tryhackme, covering various owasp top 10 vulnerabilities. It can be used in security trainings, awareness demos, ctfs, and as a guinea pig for security tools! juice shop encompasses vulnerabilities from the entire owasp top ten along with many other security flaws found in real world applications.
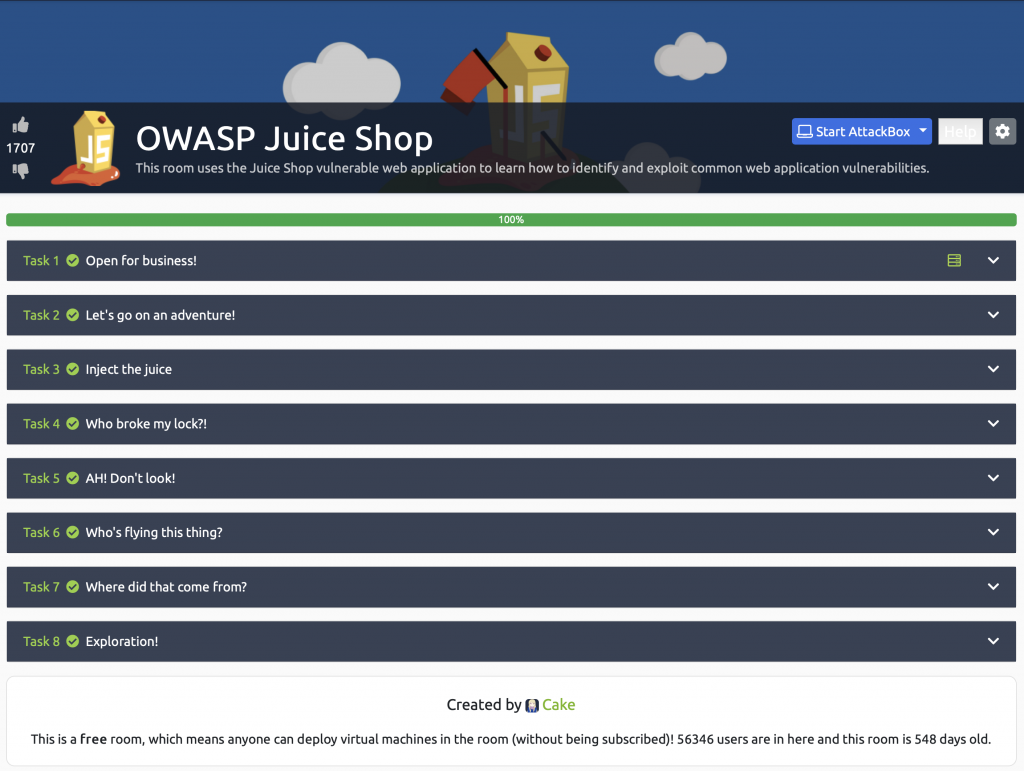
Hack The Owasp Juice Shop Tryhackme Burp Suite Fundamentals Jbc The provided content is a comprehensive walkthrough guide for the owasp juice shop, an intentionally vulnerable web application used for security training on tryhackme, covering various owasp top 10 vulnerabilities. It can be used in security trainings, awareness demos, ctfs, and as a guinea pig for security tools! juice shop encompasses vulnerabilities from the entire owasp top ten along with many other security flaws found in real world applications.
Hack The Owasp Juice Shop Tryhackme Burp Suite Fundamentals Jbc
Comments are closed.