Myid With Intel Authenticate 4
Creating The Credential Profile Myid allows you to control the lifecycle of these credentials, from issuing, enabling and disabling, requesting replacements, to cancellation and revocation, and has been integrated with intel authenticate. After clicking “next,” you will start the process to set up your new multifactor authentication (mfa). there are four options available to complete the mfa set up process; instructions for each option follow below.

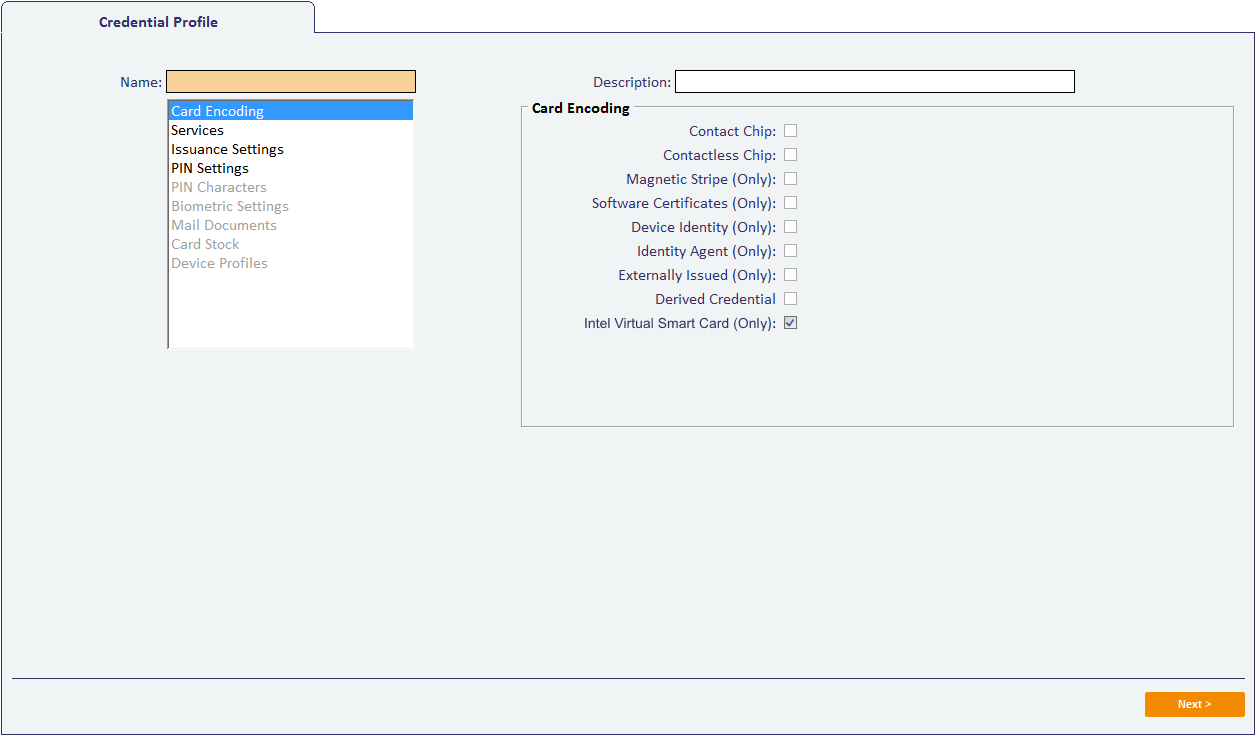
Discover Intercede Myid With Intel Authenticate At Rsa 2019 Intercede Tighten identity protection on your smart workspace with the intel authentication solution and new intel core vpro based computers. cyberattacks are growing at an alarming rate, and it’s this risk that keeps the it decision makers up at night. The intel® authenticate mobile application is the device companion app for the intel® authenticate identity and access management solution. this application enables the hardened device based proximity factor for user multifactor authentication (mfa). It moves multifactor authentication function into the hardware layer, so that key identity data and policy decisions are not exposed to software based attacks. with intel authenticate technology, secure login is no longer a time consuming process, allowing classes to start quickly and seamlessly. This document provides details of setting up and using intel authenticate virtual smart cards for myid ®. intel ® authenticate virtual smart cards can be issued to a user and collected to a device that contains intel's identity protection technology.

Top Tips For Using Myid Myid It moves multifactor authentication function into the hardware layer, so that key identity data and policy decisions are not exposed to software based attacks. with intel authenticate technology, secure login is no longer a time consuming process, allowing classes to start quickly and seamlessly. This document provides details of setting up and using intel authenticate virtual smart cards for myid ®. intel ® authenticate virtual smart cards can be issued to a user and collected to a device that contains intel's identity protection technology. By implementing intel authenticate technology, you will empower your it team with hardware enhanced protection of identity information and processing, and policy driven, enterprise level identity validation. This document provides details of setting up and using intel authenticate virtual smart cards for myid®. intel® authenticate virtual smart cards can be issued to a user and collected to a device that contains intel's identity protection technology. Our software tokens work with authentication service to turn most electronic devices, including phones, laptops and tablets, into a two factor token. the software is self contained and does not require data connectivity to function, the tokens work completely offline. This document has been created to show how myid multi factor authentication can be made to highly available, load balanced and redundant based on the various agents authenticating to the myid servers.

Download Intel Authenticate Apks For Android Apkmirror By implementing intel authenticate technology, you will empower your it team with hardware enhanced protection of identity information and processing, and policy driven, enterprise level identity validation. This document provides details of setting up and using intel authenticate virtual smart cards for myid®. intel® authenticate virtual smart cards can be issued to a user and collected to a device that contains intel's identity protection technology. Our software tokens work with authentication service to turn most electronic devices, including phones, laptops and tablets, into a two factor token. the software is self contained and does not require data connectivity to function, the tokens work completely offline. This document has been created to show how myid multi factor authentication can be made to highly available, load balanced and redundant based on the various agents authenticating to the myid servers.

Myid Mfa Intercede Our software tokens work with authentication service to turn most electronic devices, including phones, laptops and tablets, into a two factor token. the software is self contained and does not require data connectivity to function, the tokens work completely offline. This document has been created to show how myid multi factor authentication can be made to highly available, load balanced and redundant based on the various agents authenticating to the myid servers.

â žintelâ Authenticate On The App Store
Comments are closed.