Monitoring And Auditing Llm Interactions For Security Breaches

Monitoring And Auditing Llm Interactions For Security Breaches Learn how monitoring and auditing can help secure large language models (llms) against data leakage, adversarial attacks, and misuse. discover key concepts, techniques, and best practices for robust llm security. This guide shows you how to implement comprehensive audit logging for llm interactions using practical code examples, industry frameworks, and proven monitoring strategies that meet enterprise requirements.

Monitoring And Auditing Llm Interactions For Security Breaches This guide covers what llm security monitoring actually requires, how it differs from traditional application monitoring, which attacks each layer catches, and how to integrate ai security events into your existing soc workflows. This article examines audit logging requirements for ai and llm environments, exploring unique challenges and how comprehensive logging solutions ensure security, compliance, and operational integrity. Our latest blog post delves into the crucial role monitoring and auditing play in securing llm interactions. it outlines key concepts, proven techniques, and best practices for crafting a. Explore llm security vulnerabilities with this developer’s checklist, covering risks, mitigation strategies, and best practices for safe ai deployment.

Monitoring And Auditing Llm Interactions For Security Breaches Our latest blog post delves into the crucial role monitoring and auditing play in securing llm interactions. it outlines key concepts, proven techniques, and best practices for crafting a. Explore llm security vulnerabilities with this developer’s checklist, covering risks, mitigation strategies, and best practices for safe ai deployment. Monitor malicious user activity by scanning your llm logs for the most critical security and safety risks and mitigate threats before they cause reputational damage or financial losses. This guide explores comprehensive best practices for auditing and ensuring compliance in llm deployments, covering documentation requirements, data governance, output monitoring, explainability techniques, and establishing audit trails that satisfy regulators while enabling practical llm applications in regulated industries. Log based insider threat detection (itd) detects malicious user activities by auditing log entries. recently, large language models (llms) with strong common sense knowledge have emerged in the domain of itd. Access controls and audit trails are critical for securing sensitive llm interactions. without them, organizations risk data leaks, regulatory fines, and loss of trust. learn how to implement them effectively in 2026.

Monitoring Llm Security Reducing Llm Risks Langfuse Blog Monitor malicious user activity by scanning your llm logs for the most critical security and safety risks and mitigate threats before they cause reputational damage or financial losses. This guide explores comprehensive best practices for auditing and ensuring compliance in llm deployments, covering documentation requirements, data governance, output monitoring, explainability techniques, and establishing audit trails that satisfy regulators while enabling practical llm applications in regulated industries. Log based insider threat detection (itd) detects malicious user activities by auditing log entries. recently, large language models (llms) with strong common sense knowledge have emerged in the domain of itd. Access controls and audit trails are critical for securing sensitive llm interactions. without them, organizations risk data leaks, regulatory fines, and loss of trust. learn how to implement them effectively in 2026.
Example Monitoring Llm Security Langfuse Log based insider threat detection (itd) detects malicious user activities by auditing log entries. recently, large language models (llms) with strong common sense knowledge have emerged in the domain of itd. Access controls and audit trails are critical for securing sensitive llm interactions. without them, organizations risk data leaks, regulatory fines, and loss of trust. learn how to implement them effectively in 2026.
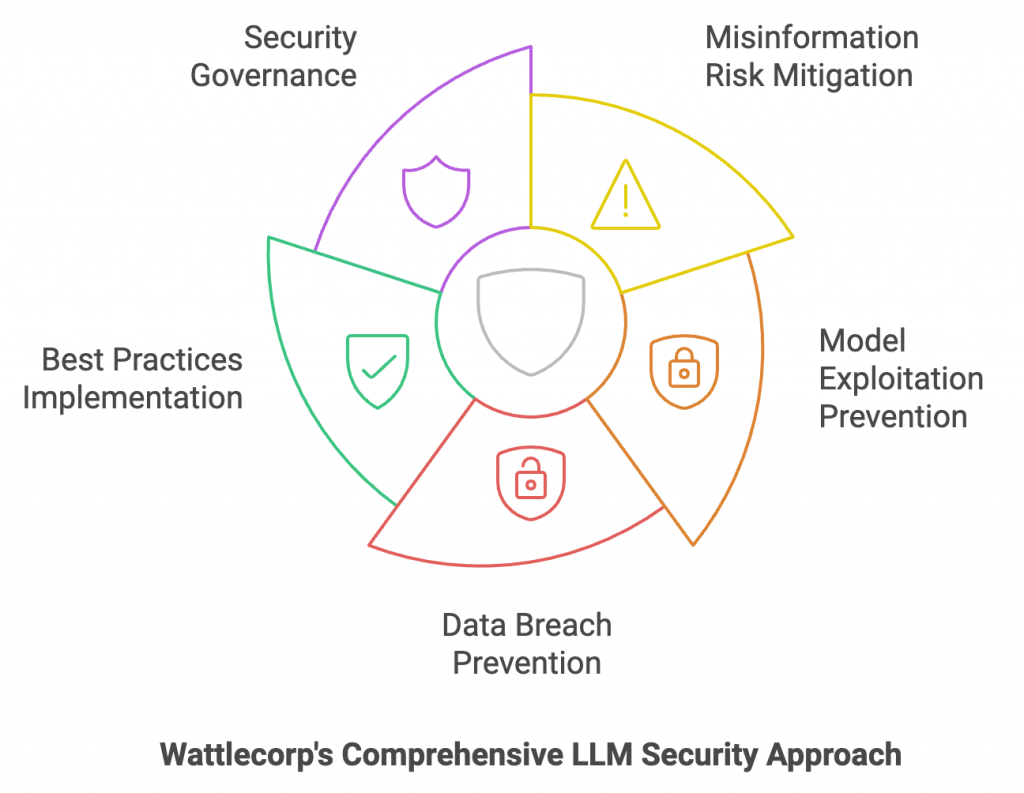
Llm Security Risks Checklists Best Practices Wattlecorp
Comments are closed.