Mitigation Techniques Of Side Channel Attacks Stellarix

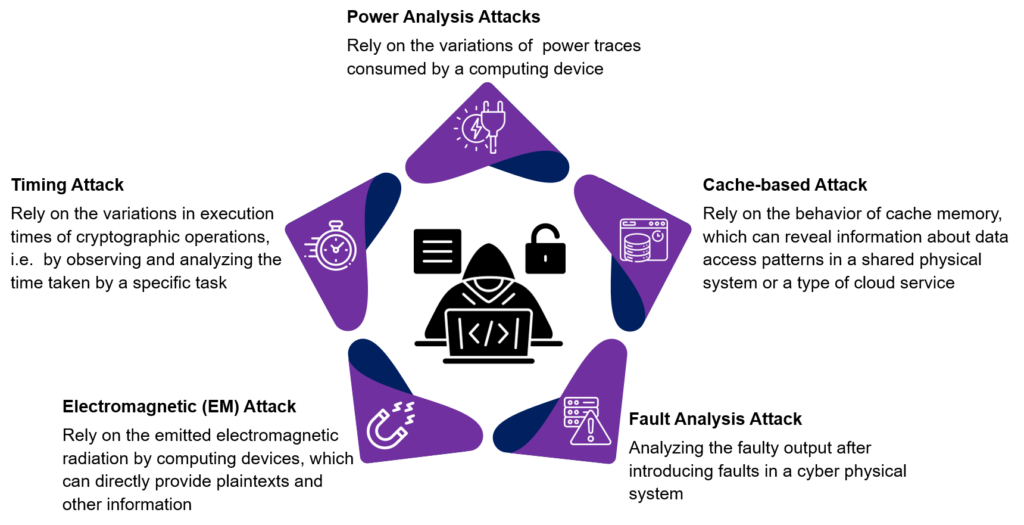
Mitigating Timing Side Channel Attacks In Software Defined Networks Explore side channel attacks in homomorphic encryption and learn key hardware, software, and ai driven techniques to mitigate security risks. A side channel attack, also known as a sidebar attack or an implementation attack, is a security breach that gathers information either from the systemu2019s execution process or by process manipulation. these attacks are based on observing and analyzing the physical behavior of encryption.

Mitigation Techniques Of Side Channel Attacks In Homomorphic Encryption In this paper we aim to present a review on the various side channel attacks possible. also, the techniques proposed to mitigate such an attack have been stated. The proposed hybrid cryptographic framework is designed to address a range of side channel attacks (sca) and cryptanalysis based threats. This paper reviews the evolution, methodologies, and implications of side channel attacks, as well as countermeasures developed to mitigate these threats, focusing on modern systems and. The power overhead could be reduced by attack detection and and turning on the mitigation techniques only during an attack through event driven duty cycling. this calls for the design of low overhead power and em attack detectors.

Mitigation Techniques Of Side Channel Attacks Stellarix This paper reviews the evolution, methodologies, and implications of side channel attacks, as well as countermeasures developed to mitigate these threats, focusing on modern systems and. The power overhead could be reduced by attack detection and and turning on the mitigation techniques only during an attack through event driven duty cycling. this calls for the design of low overhead power and em attack detectors. In addition to secure design principles, various countermeasures can be employed to mitigate side channel attacks. these include masking and hiding techniques, noise injection and randomization, and shielding and protective coatings. In this article, i’ll walk you through what side channel attacks are, why they’re so dangerous, and how we can begin to mitigate their risks in our systems. at its core, a side channel. Although techniques like post quantum cryptography, lightweight cryptography, and methods to prevent attacks such as the poisson attack effectively secure cryptographic algorithms, the cryptographic process remains vulnerable to side channel attacks (sca). Developers can employ a number of security best practices to help protect against various types of side channel attacks and provide defense in depth.
Mitigation Techniques Of Side Channel Attacks Stellarix In addition to secure design principles, various countermeasures can be employed to mitigate side channel attacks. these include masking and hiding techniques, noise injection and randomization, and shielding and protective coatings. In this article, i’ll walk you through what side channel attacks are, why they’re so dangerous, and how we can begin to mitigate their risks in our systems. at its core, a side channel. Although techniques like post quantum cryptography, lightweight cryptography, and methods to prevent attacks such as the poisson attack effectively secure cryptographic algorithms, the cryptographic process remains vulnerable to side channel attacks (sca). Developers can employ a number of security best practices to help protect against various types of side channel attacks and provide defense in depth.

Mitigation Techniques Of Side Channel Attacks Stellarix Although techniques like post quantum cryptography, lightweight cryptography, and methods to prevent attacks such as the poisson attack effectively secure cryptographic algorithms, the cryptographic process remains vulnerable to side channel attacks (sca). Developers can employ a number of security best practices to help protect against various types of side channel attacks and provide defense in depth.

Mitigation Techniques Of Side Channel Attacks Stellarix
Comments are closed.