Mitigating Identity Attack Surface In Cloud Environments
Mitigating Identity Attack Surface In Cloud Environments In this blog, we’ll dive deep into the concept of identity attack surface in cloud computing, explore common attack vectors, examine real world breaches, and provide actionable best practices to help you secure your cloud environment. Learn how to identify, manage, and secure the cloud attack surface. a cio’s guide to emerging threats, iam hardening, workload security & risk reduction.

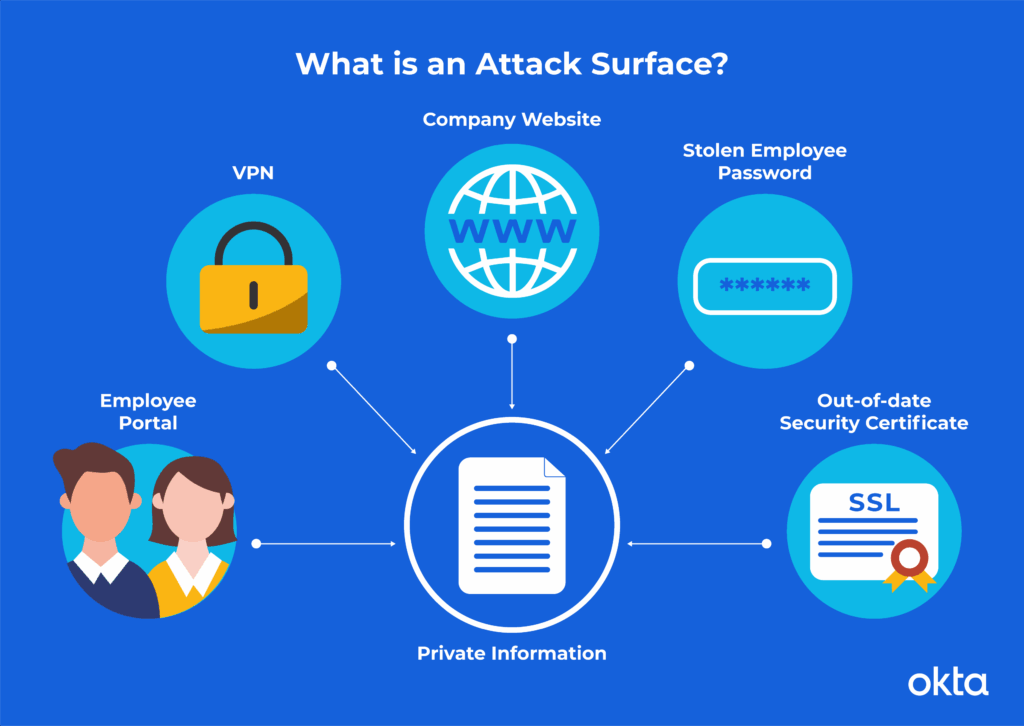
Mitigating Identity Attack Surface In Cloud Environments Compromised credentials are now the leading cause of cloud breaches, making identity your most critical attack surface. a new idc white paper explores why this shift is happening and where traditional defenses fall short. Modern enterprises operate in highly distributed environments where cloud adoption, remote work, and third party integrations have significantly expanded the identity attack surface. identity sprawl and overprivileged accounts create persistent security gaps that traditional perimeter defenses cannot effectively mitigate. Learn best practices for reducing your attack surface in cloud environments. covers misconfiguration prevention, access control, and cloud native security strategies. Don’t know what cloud attack surface is? learn what it is, why it's growing, how to reduce risks, & best practices for securing your cloud attack surface.
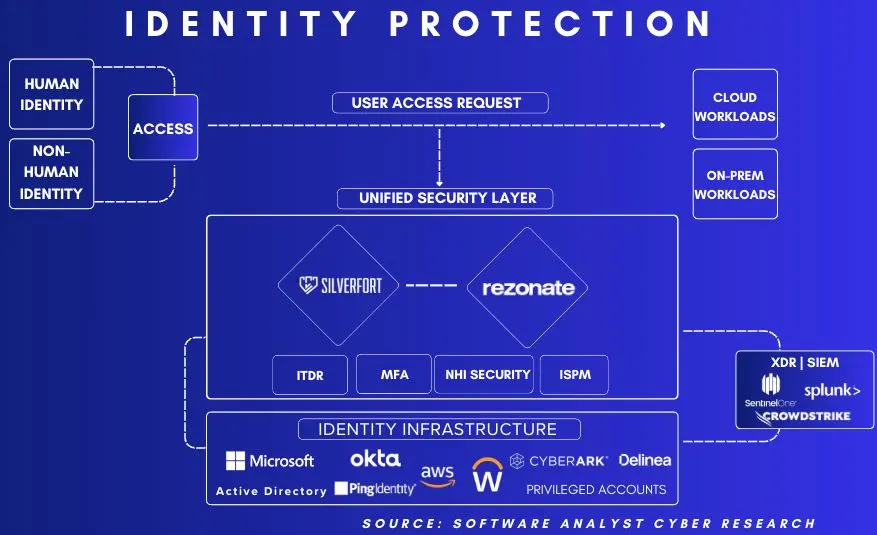
Mitigating Identity Attack Surface In Cloud Environments Learn best practices for reducing your attack surface in cloud environments. covers misconfiguration prevention, access control, and cloud native security strategies. Don’t know what cloud attack surface is? learn what it is, why it's growing, how to reduce risks, & best practices for securing your cloud attack surface. How do we protect sensitive data from attackers? learn how to strengthen protection in aws and reduce the attack surface in the cloud. Discover why to prioritize identity attack surface management, what tools and strategies are needed, and how iasm builds cyber resilience. Learn how cloud attack surface assessments work, why they differ from traditional approaches, and how combining attack surface management with unified vulnerability management enables effective exposure management. Proper identity and access management (iam) are critical to securing cloud resources. malicious actors can compromise accounts using phishing techniques, exposed credentials, or weak.

Cybercriminals Capitalize On Poorly Configured Cloud Environments How do we protect sensitive data from attackers? learn how to strengthen protection in aws and reduce the attack surface in the cloud. Discover why to prioritize identity attack surface management, what tools and strategies are needed, and how iasm builds cyber resilience. Learn how cloud attack surface assessments work, why they differ from traditional approaches, and how combining attack surface management with unified vulnerability management enables effective exposure management. Proper identity and access management (iam) are critical to securing cloud resources. malicious actors can compromise accounts using phishing techniques, exposed credentials, or weak.

Introducing Mandiant Advantage Attack Surface Management Google Cloud Learn how cloud attack surface assessments work, why they differ from traditional approaches, and how combining attack surface management with unified vulnerability management enables effective exposure management. Proper identity and access management (iam) are critical to securing cloud resources. malicious actors can compromise accounts using phishing techniques, exposed credentials, or weak.
Comments are closed.