Mev Attacks Explained Blockchain Vulnerabilities

Understanding Mev Attacks Cow Dao Learn what mev (maximal extractable value) is in blockchain networks. understand how miners and validators extract value through transaction ordering, including front running, sandwich attacks, and liquidation strategies. explore mev's impact on defi fairness, gas fees, and current solutions like flashbots and pbs. Rather than being inherent costs of using the blockchain, mev attacks exploit vulnerabilities in the transaction processing model to extract additional value at the expense of traders. what is mev? mev refers to the value that can be extracted from a blockchain transaction beyond standard fees.
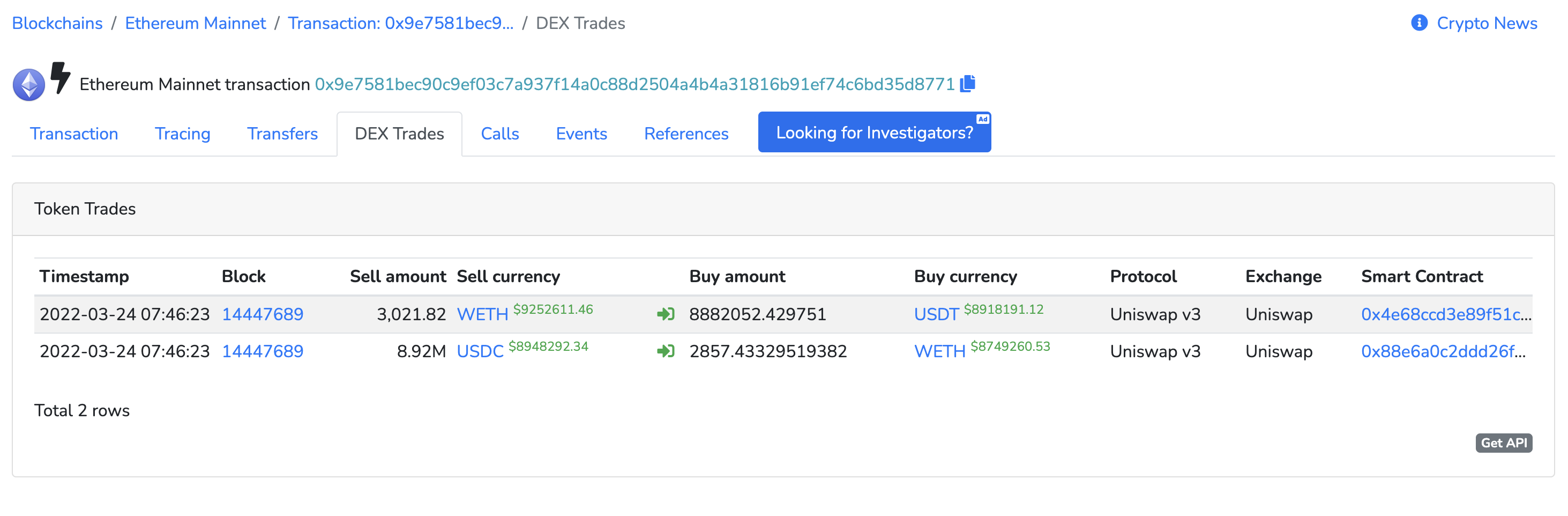
What Is Backrunning Mev Attacks Explained By Cow Protocol Medium All users are at risk of malicious mev, even those making small trades, across major chains like ethereum, bnb chain, polygon, and solana. these attacks are possible because most blockchains expose pending transactions in a public mempool, allowing bots to see and act on them before confirmation. In short, an mev attack leverages another transaction and market instability to extract economic value from the blockchain. this can be done through arbitrage or blockchain specific attacks such as sandwiches. This article will demystify mev bots, exploring their impact, the debates surrounding their use in decentralized finance (defi) and touch upon security relevant aspects of mev. Mev attacks can manipulate markets, harm users, traders and liquidity providers, and destabilize the blockchain network. mev is the profit that miners validators can make by manipulating.
What Is Backrunning Mev Attacks Explained By Cow Protocol Medium This article will demystify mev bots, exploring their impact, the debates surrounding their use in decentralized finance (defi) and touch upon security relevant aspects of mev. Mev attacks can manipulate markets, harm users, traders and liquidity providers, and destabilize the blockchain network. mev is the profit that miners validators can make by manipulating. Learn what an mev attack is, how it works, and how users can reduce risk in web3. what is an mev attack? an mev attack (maximal extractable value attack) occurs when someone like a block producer or privileged actor, frequently an automated bot, manipulates the order of transactions. Uncover maximal extractable value (mev): learn about arbitrage, front running, and other defi exploits. discover mitigation strategies and the future of fair blockchain interactions. Jito and mev on solana: a different blockchain technology playbook solana's mev story is structurally different from ethereum's. solana has no traditional public mempool; transactions are forwarded directly to the current leader. that made the classical sandwich attack harder in theory but far from impossible in practice. One such challenge is the phenomenon of miner extractable value (mev) exploits, which can severely impact the efficiency and fairness of blockchain systems. as the demand for crypto exchange development continues to grow, addressing mev vulnerabilities has become a critical priority for developers and exchanges alike.
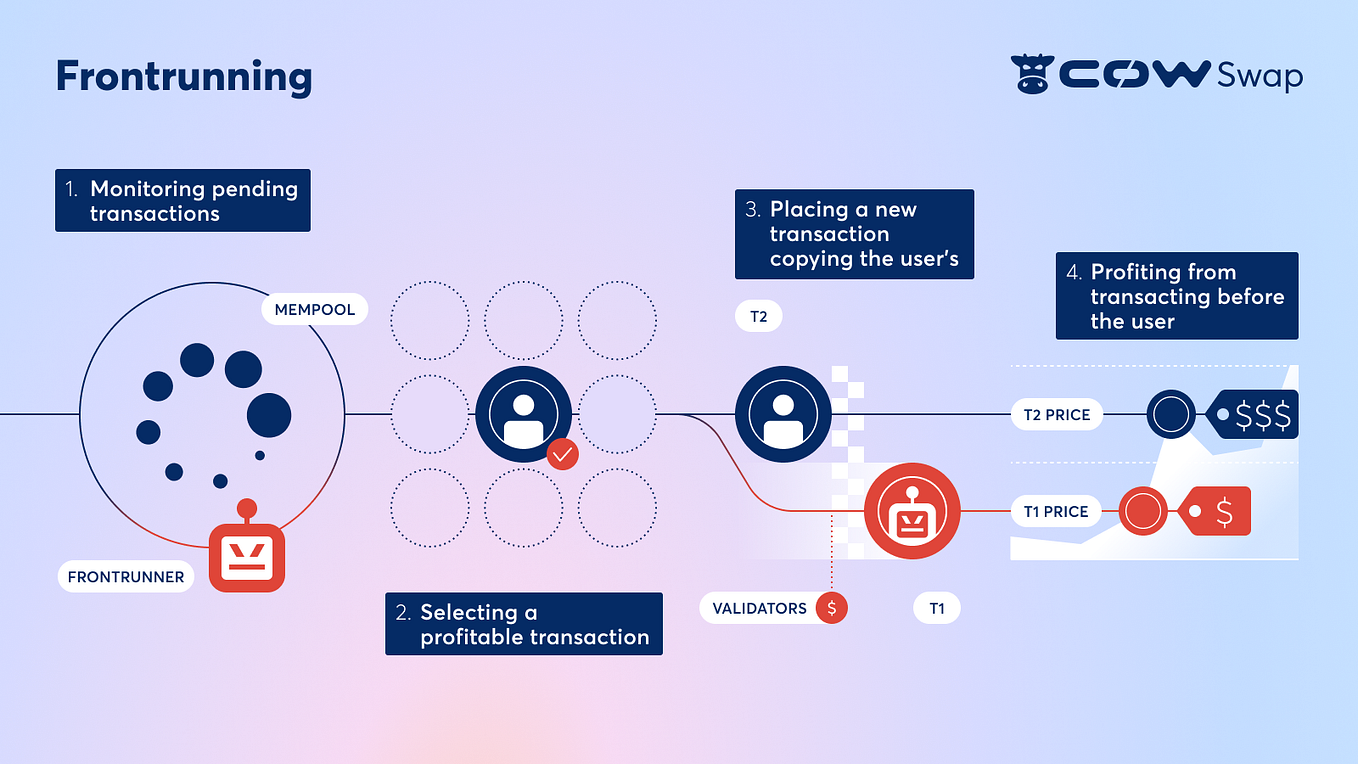
What Is Backrunning Mev Attacks Explained By Cow Protocol Medium Learn what an mev attack is, how it works, and how users can reduce risk in web3. what is an mev attack? an mev attack (maximal extractable value attack) occurs when someone like a block producer or privileged actor, frequently an automated bot, manipulates the order of transactions. Uncover maximal extractable value (mev): learn about arbitrage, front running, and other defi exploits. discover mitigation strategies and the future of fair blockchain interactions. Jito and mev on solana: a different blockchain technology playbook solana's mev story is structurally different from ethereum's. solana has no traditional public mempool; transactions are forwarded directly to the current leader. that made the classical sandwich attack harder in theory but far from impossible in practice. One such challenge is the phenomenon of miner extractable value (mev) exploits, which can severely impact the efficiency and fairness of blockchain systems. as the demand for crypto exchange development continues to grow, addressing mev vulnerabilities has become a critical priority for developers and exchanges alike.

What Is Backrunning Mev Attacks Explained Cow Dao Jito and mev on solana: a different blockchain technology playbook solana's mev story is structurally different from ethereum's. solana has no traditional public mempool; transactions are forwarded directly to the current leader. that made the classical sandwich attack harder in theory but far from impossible in practice. One such challenge is the phenomenon of miner extractable value (mev) exploits, which can severely impact the efficiency and fairness of blockchain systems. as the demand for crypto exchange development continues to grow, addressing mev vulnerabilities has become a critical priority for developers and exchanges alike.
Understanding Different Mev Attacks Frontrunning Backrunning And
Comments are closed.