Md5 Collision Attack Lab Task1 And Task 2
Md5 Collision Attack Lab A Cryptographic Security Seed Lab Md5 To achieve this goal, students need to launch actual collision attacks against the md5 hash function. using the attacks, students should be able to create two different programs that share the same md5 hash but have completely different behaviors. The idea behind this task is to append separate suffixes to the two colliding files and subsequently observe the hash values produced by the md5 algorithm. this experiment delves into the.
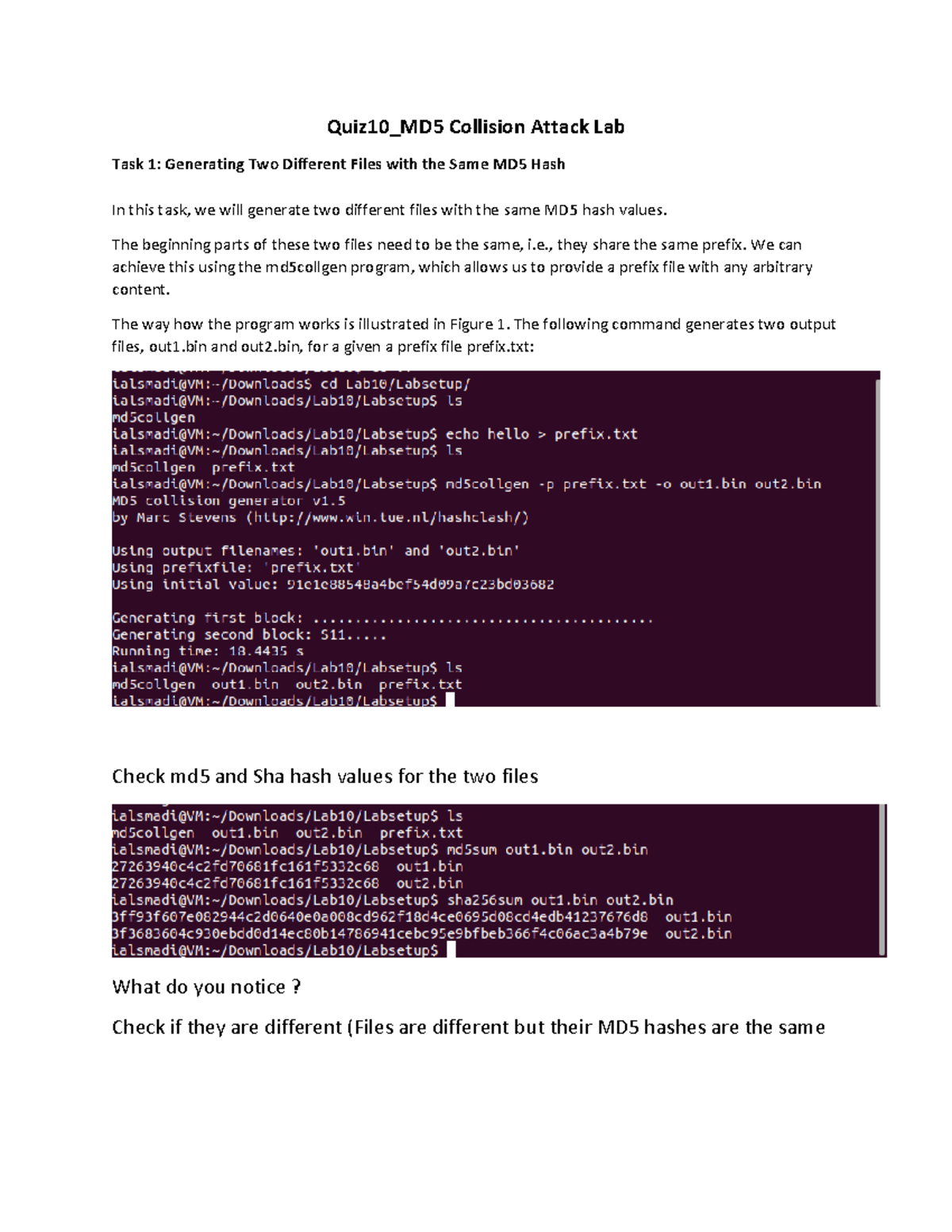
Quiz10 Md5 Collision Attack Lab Quiz10 Md5 Collision Attack Lab Task The learning objective of this lab is for students to really understand the impact of collision attacks, and to see first hand what damage can be caused if a widely used one way hash function’s collision resistance property is broken. Verify that the md5 hashes are the same using md5sum hi1 hi2. now let’s append a random string to the end of both files and check the md5 hashes of both files again. From very high level, it is not so complicated. md5 divides the input data into blocks of 64 bytes, and then computes the hash iteratively on these blocks. the core of the md5 algorithm is a compression function, which takes two inputs, a 64 byte data block and the outcome of the previous iteration. the compression function. This exercise vividly illustrated how two different files could be crafted to produce the same hash, highlighting the vulnerability of md5 to collision attacks.
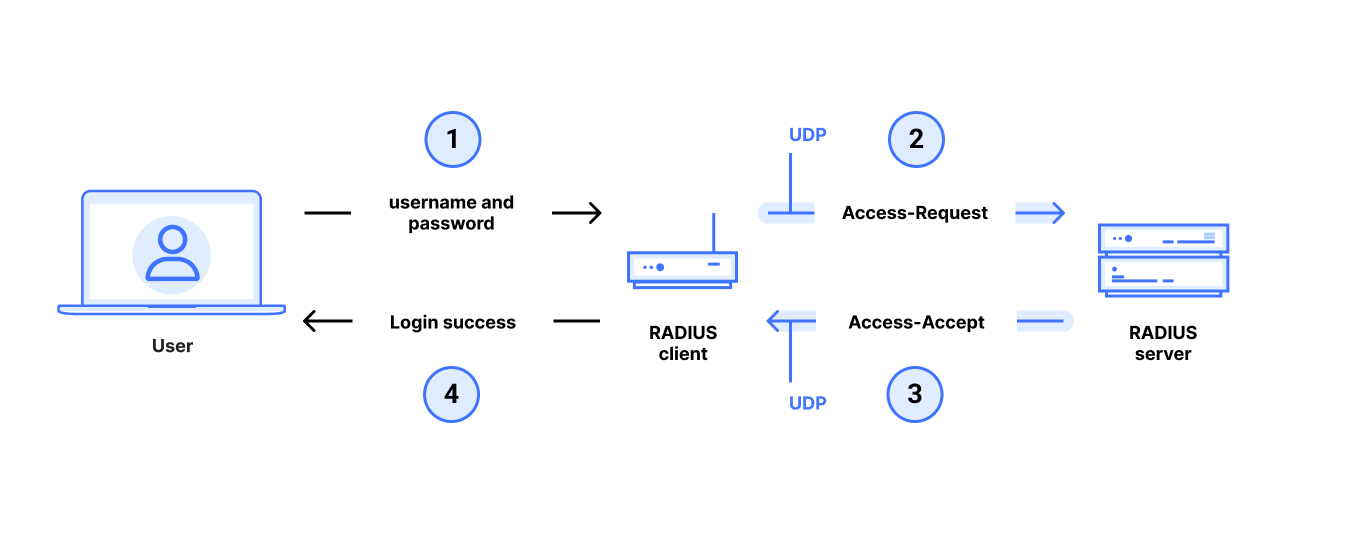
Radius Udp Vulnerable To Improved Md5 Collision Attack Gixtools From very high level, it is not so complicated. md5 divides the input data into blocks of 64 bytes, and then computes the hash iteratively on these blocks. the core of the md5 algorithm is a compression function, which takes two inputs, a 64 byte data block and the outcome of the previous iteration. the compression function. This exercise vividly illustrated how two different files could be crafted to produce the same hash, highlighting the vulnerability of md5 to collision attacks. Students will generate two different files and executable programs that share the same md5 hash value but behave differently, demonstrating the potential dangers of broken collision resistance properties. We used the cmp utility available in seed lab ubuntu vm to identify the differences in the two files (task1 out1.bin and task1 out2.bin) generated by md5collgen. we can see that the vast majority of the added content is the same, with only 6 bytes that differ between the two files. Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . What is collision? collision is when the hashes of two different hashed files match two different files same hash.

Md5 Collision Attack Seed Security Labs By Swetha Medium Students will generate two different files and executable programs that share the same md5 hash value but behave differently, demonstrating the potential dangers of broken collision resistance properties. We used the cmp utility available in seed lab ubuntu vm to identify the differences in the two files (task1 out1.bin and task1 out2.bin) generated by md5collgen. we can see that the vast majority of the added content is the same, with only 6 bytes that differ between the two files. Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . What is collision? collision is when the hashes of two different hashed files match two different files same hash.
Comments are closed.