Mandatory Input Validity Software Testing
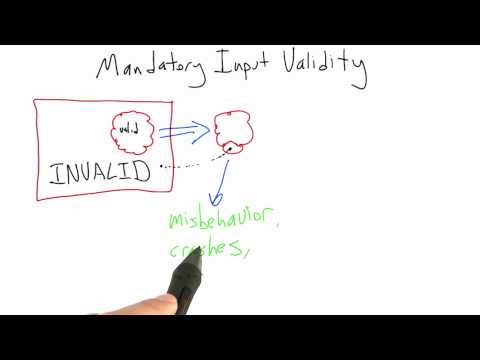
Learn Mandatory Input Validity Software Testing Mind Luster Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. Input validation is the process of testing and ensuring that the input received by a computer application meets the required standards or criteria defined within the application.
The Top 10 Mistakes To Avoid When Reviewing Source Code Varutra Cross site scripting (xss) testing checks if it is possible to manipulate the input parameters of the application so that it generates malicious output. testers find an xss vulnerability when the application does not validate their input and creates an output that is under their control. This video is part of an online course, software testing. check out the course here: udacity course cs258. This article only scratches the surface of what’s possible with input validation, but following these practices can make a world of difference in keeping your applications safe and secure. So, whenever you test a form, consider these three ways to validate users' input before submitting a bug report to prevent rejections and efficiently power up your testing process. learn about three highly effective form validation methods to streamline your testing process.
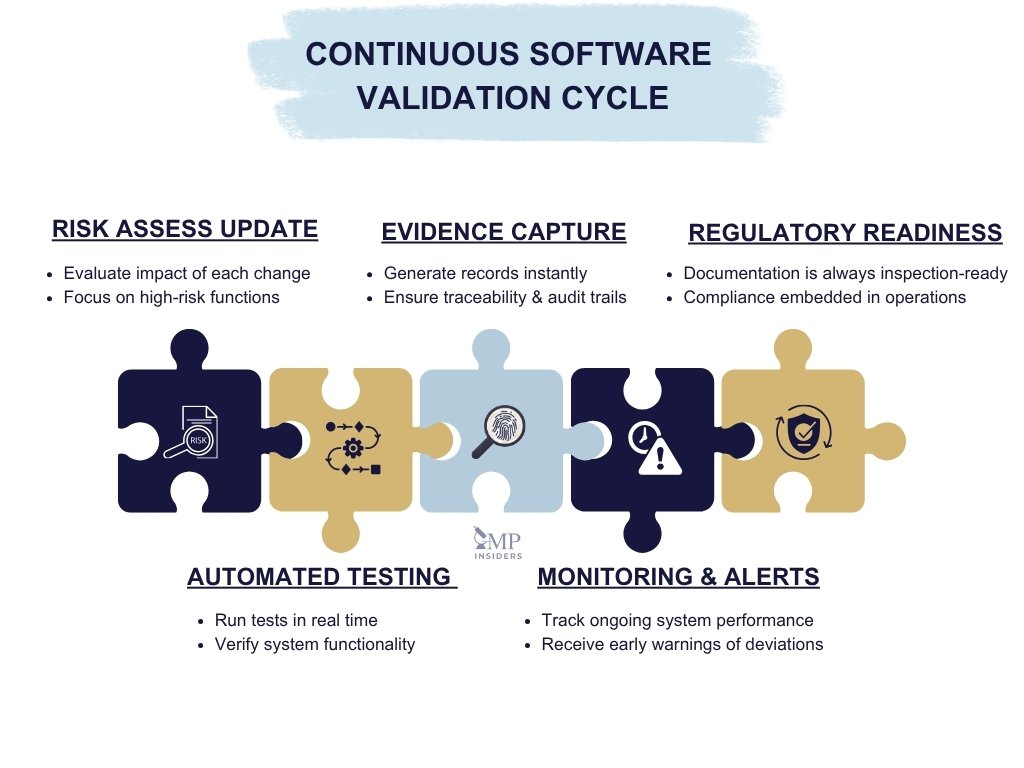
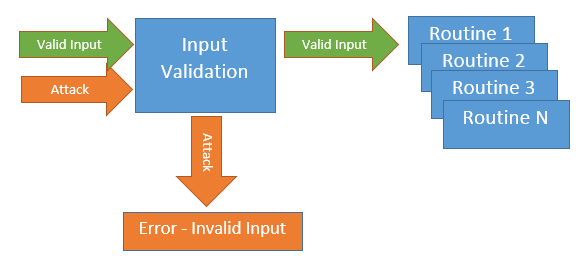
Continuous Software Validation In Gmp Risk Based Control Across The This article only scratches the surface of what’s possible with input validation, but following these practices can make a world of difference in keeping your applications safe and secure. So, whenever you test a form, consider these three ways to validate users' input before submitting a bug report to prevent rejections and efficiently power up your testing process. learn about three highly effective form validation methods to streamline your testing process. Reuse shared validation functions across your codebase for consistency. following this checklist helps block injection attacks, reduce bugs, and keep your app secure by design. It is vital that input validation is performed to provide the starting point for a secure application or system. without input validation the software application system will continue to be vulnerable to new and varied attacks. Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. Unlock the essentials of input validation for secure software development through practical techniques and examples. in software development, input validation is often considered the first defense against various security vulnerabilities.

Software Testing Methodologies Exploring Effective Techniques Reuse shared validation functions across your codebase for consistency. following this checklist helps block injection attacks, reduce bugs, and keep your app secure by design. It is vital that input validation is performed to provide the starting point for a secure application or system. without input validation the software application system will continue to be vulnerable to new and varied attacks. Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. Unlock the essentials of input validation for secure software development through practical techniques and examples. in software development, input validation is often considered the first defense against various security vulnerabilities.
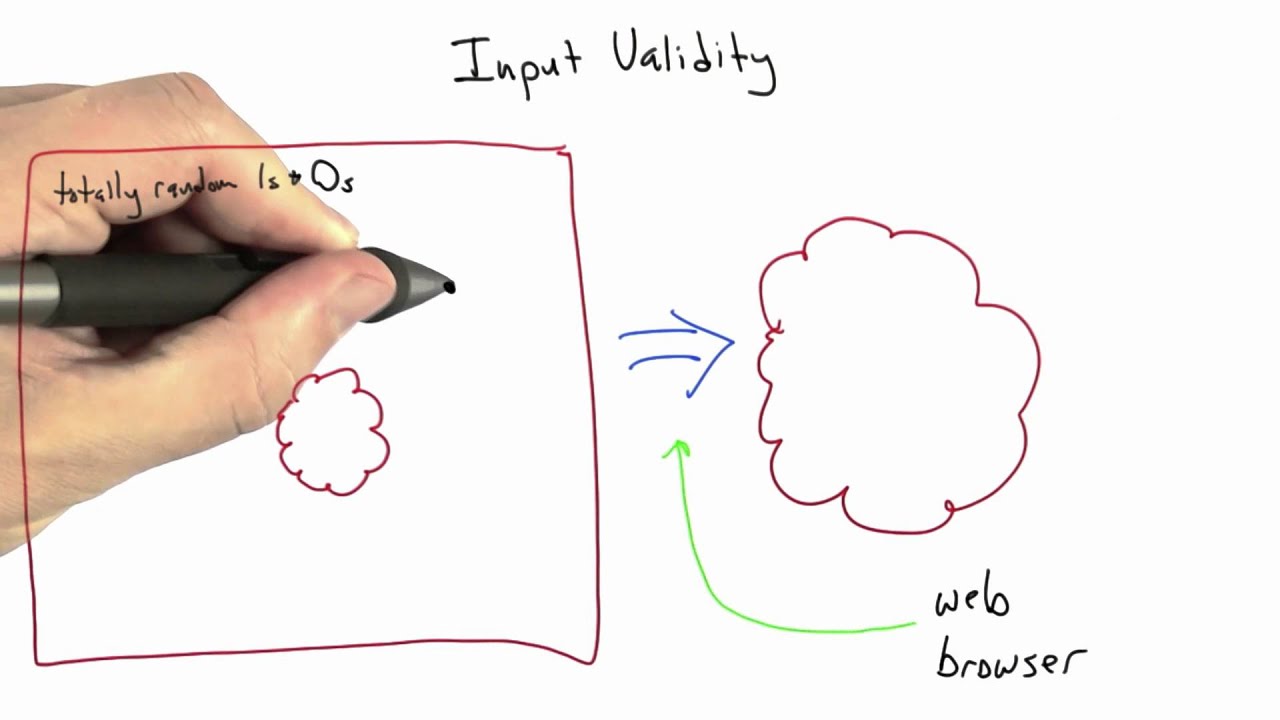
Input Validity Software Testing Youtube Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. Unlock the essentials of input validation for secure software development through practical techniques and examples. in software development, input validation is often considered the first defense against various security vulnerabilities.

Input Validation And Bypass Testing Of Web Applications
Comments are closed.