Manage Members Fluid Attacks Help
Manage Members Fluid Attacks Help Efficiently manage organization and group members on the fluid attacks platform, including invitations, role assignments, and removals. Discover your potential, starting today. holders of the fluid attacks' platform (user manager track) certification have a general knowledge of the platform's features to help them fulfill their tasks of reviewing the requests of developers and tracking remediation progress.

Application Security Testing Solutions Fluid Attacks After changes are saved, you and other group members are sent a notification showing the current group information along with how it changed. the fluid attacks staff roles that give permission to edit these fields are customer manager and admin. Inviting members on fluid attacks' platform and understanding their roles in terms of permissions. still can’t find an answer? send us a ticket and we will get back to you. Members on the fluid attacks platform have distinct roles with associated permissions. you can view your role within the organization or group you are navigating in the user menu, which is in the upper right corner of your screen. Chat with the ai agent to get information quickly about your organization or group, or vulnerability management advice, leveraging fluid attacks' generative ai.
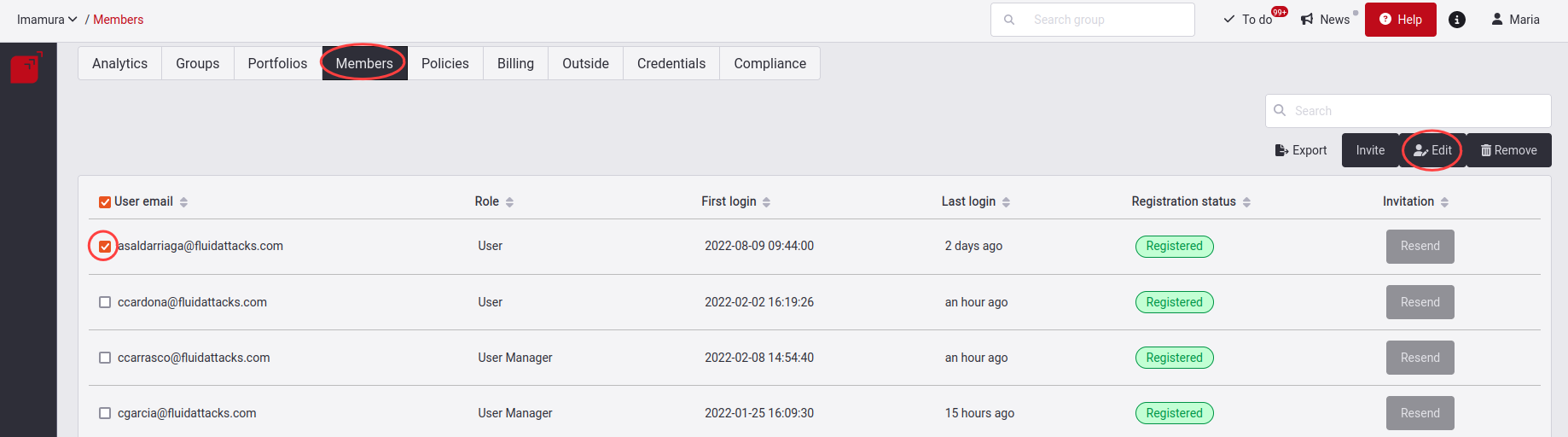
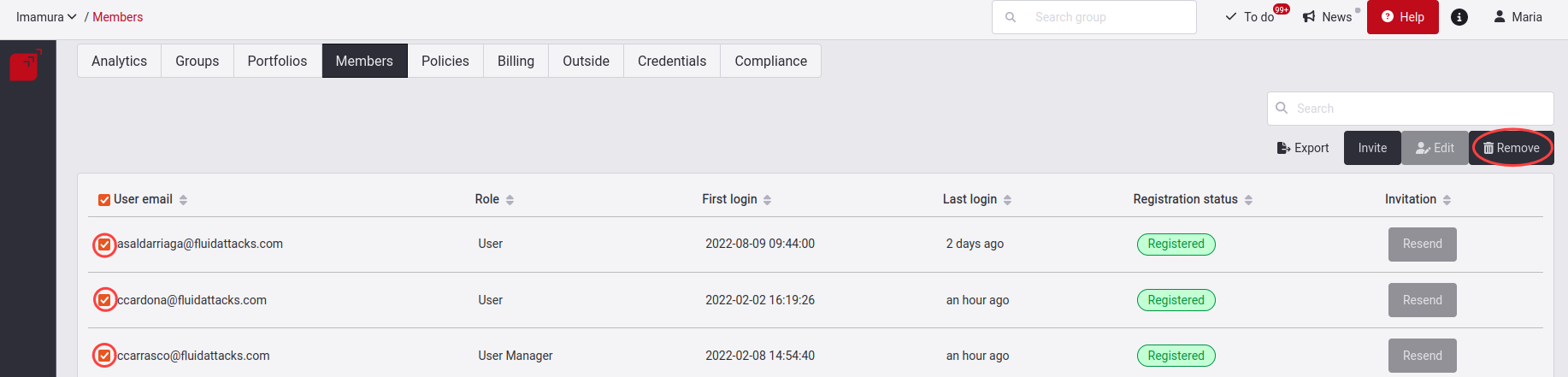
Manage Members Fluid Attacks Help Members on the fluid attacks platform have distinct roles with associated permissions. you can view your role within the organization or group you are navigating in the user menu, which is in the upper right corner of your screen. Chat with the ai agent to get information quickly about your organization or group, or vulnerability management advice, leveraging fluid attacks' generative ai. Add users to your group and manage their roles! user managers in the arm can invite and manage group users, their responsibilities, and roles in the stakeholders section. Holders of the fluid attacks' platform (developer track) certification have a general knowledge of the platform's capabilities to help them fulfill their tasks of understanding and remediating vulnerabilities in their software projects. Creating a new group and managing it is your organization's decision and responsibility. on fluid attacks' platform, groups are projects that you create dedicated to your applications or software products to keep track of their security assessments and risk exposure separately. Learn to invite team members to sign up on the fluid attacks platform so they can be assigned vulnerability remediation work.
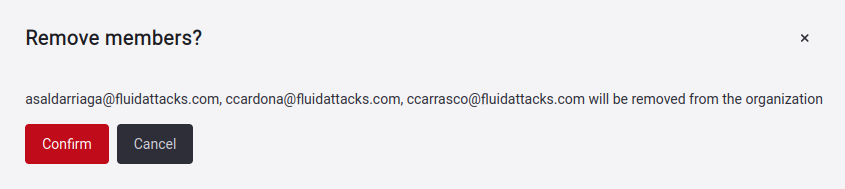
Manage Members Fluid Attacks Help Add users to your group and manage their roles! user managers in the arm can invite and manage group users, their responsibilities, and roles in the stakeholders section. Holders of the fluid attacks' platform (developer track) certification have a general knowledge of the platform's capabilities to help them fulfill their tasks of understanding and remediating vulnerabilities in their software projects. Creating a new group and managing it is your organization's decision and responsibility. on fluid attacks' platform, groups are projects that you create dedicated to your applications or software products to keep track of their security assessments and risk exposure separately. Learn to invite team members to sign up on the fluid attacks platform so they can be assigned vulnerability remediation work.
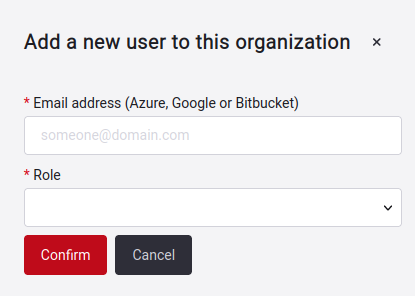
Manage Members Fluid Attacks Help Creating a new group and managing it is your organization's decision and responsibility. on fluid attacks' platform, groups are projects that you create dedicated to your applications or software products to keep track of their security assessments and risk exposure separately. Learn to invite team members to sign up on the fluid attacks platform so they can be assigned vulnerability remediation work.
Comments are closed.