Malware Analysis Part 2 Basic Static Analysis Youtube
Malware Static Analysis Tryhackme Basic Static Analysis In this step by step session, cyber consultant harpreet s. arora shows how to combine static analysis, dynamic sandboxing, and ai powered behavior tools to catch zero day ransomware before it. In malware analysis, hash files can be used to identify unique malware, search for this malware in different malware repositories and databases, and as an indicator of compromise (ioc).
Static Malware Analysis Youtube In the previous article, i discussed the basics, different techniques for malware analysis, how to obtain samples, and some basic programs for conducting this type of analysis. In this article, i am trying to explain the basic static analysis methodologies of malware analysis. let’s begin! i was actually planning to focus on both basic static and basic dynamic analysis in this article but to properly explain everything i am sticking to basic static analysis. Explore basic static analysis methods, set up virtual machines for safe malware examination, and practice dynamic analysis techniques. gain hands on experience with lab exercises covering various aspects of malware investigation, from initial assessment to in depth analysis using virtual environments and network simulation tools like inetsim. In the intro to malware analysis room, we identified that searching for strings is one of the first steps in malware analysis. a string search provides useful information to a malware analyst by identifying important pieces of strings present in a suspected malware sample.
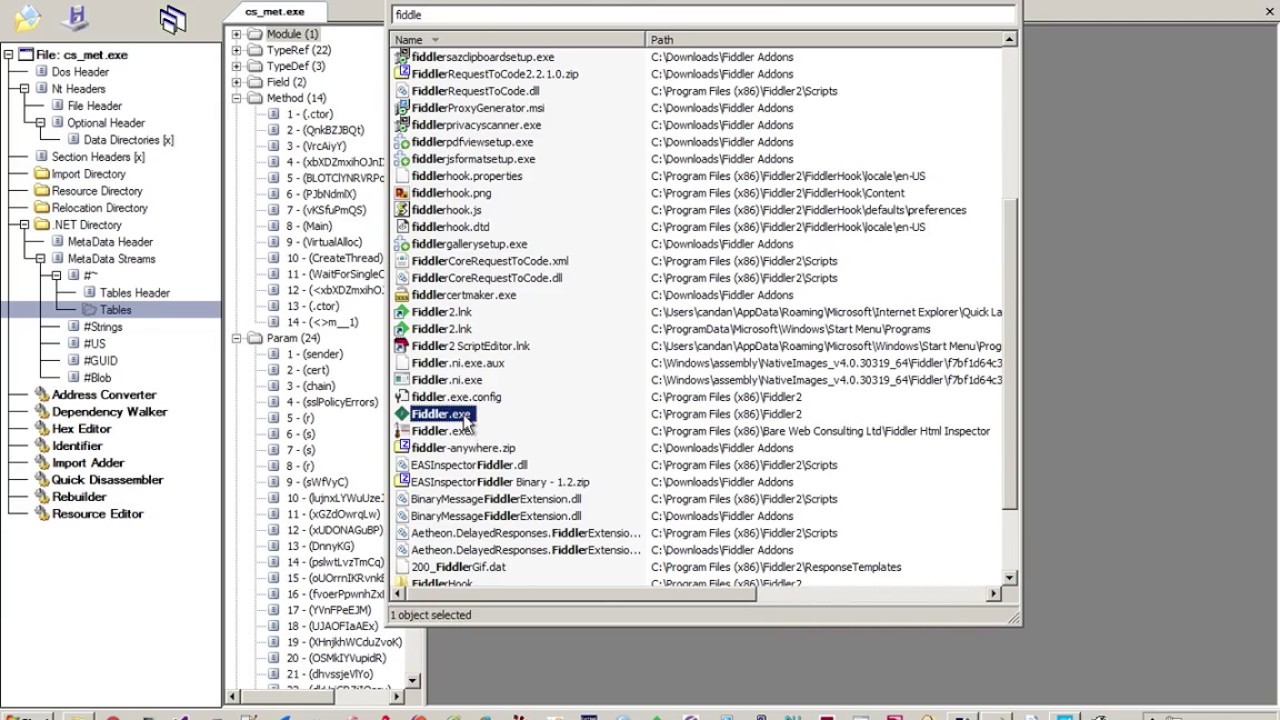
Malware Analysis Part 1 Basic Static Analysis Youtube Explore basic static analysis methods, set up virtual machines for safe malware examination, and practice dynamic analysis techniques. gain hands on experience with lab exercises covering various aspects of malware investigation, from initial assessment to in depth analysis using virtual environments and network simulation tools like inetsim. In the intro to malware analysis room, we identified that searching for strings is one of the first steps in malware analysis. a string search provides useful information to a malware analyst by identifying important pieces of strings present in a suspected malware sample. This document discusses basic static analysis techniques for malware analysis. it describes examining malware files while at rest to identify unusual features without executing the files. In the previous rooms of this module, we learned about the basics of computer architecture and assembly language. while those topics are essential building blocks to learning malware analysis, we will start analyzing malware starting from this room. Preliminary analysis: conducting initial assessments to gather basic information about the malware. static analysis: examining the malware without executing it to extract metadata and understand its structure. Chatgpt for reverse malware engineering use chatgpt to analyze data obtained from simple static analysis and produce logical comments for the purpose and behavior of the code.
Comments are closed.