Mac Spoofing A Pentesters Guide
Mac Address Spoofing Technocate Join us as we delve into the technical aspects of mac spoofing, demonstrate how it can be executed, and discuss its implications for cybersecurity measures. We will not just tell you what mac spoofing is; we are going to show you exactly how attackers bypass your firewalls using it, and more importantly, how you can catch them. from deep packet analysis in wireshark to writing your own detection algorithms in python, this is the only guide you will ever need.
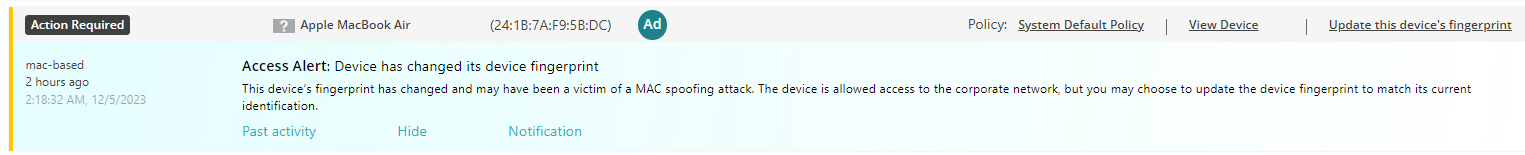
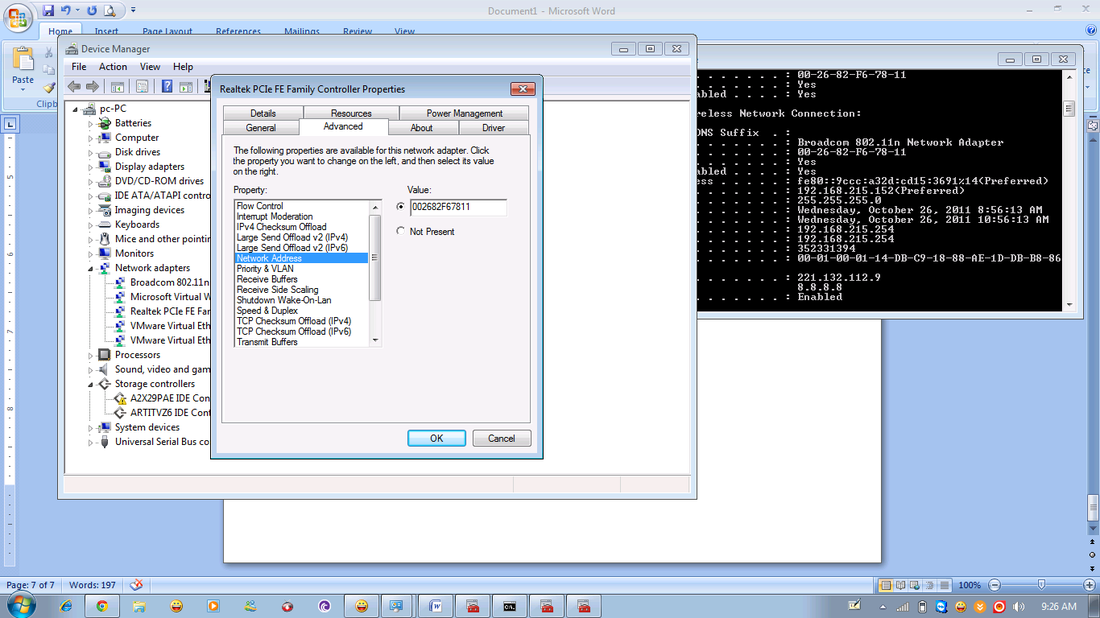
Turn On Mac Address Spoofing Protection By Iot Fingerprinting Learn what mac spoofing is, how attackers use it, and how to prevent it. this 2025 guide covers detection tools, real world risks, and expert prevention techniques for businesses and individuals. This comprehensive guide explores the practical implementation of mac address modification across various platforms, providing verified commands for penetration testers, network administrators, and cybersecurity enthusiasts. learning objectives: master mac address manipulation techniques across windows, linux, and macos systems. Mac spoofing essentially allows hackers to assume another’s identity and intercept communications. let’s look at mac spoofing in detail, how it is used, and how you can protect yourself against it. Uncover the secrets of mac spoofing: learn how network hackers manipulate device identities, protect your system, and defend against cyber threats.

What Is Mac Spoofing Mac spoofing essentially allows hackers to assume another’s identity and intercept communications. let’s look at mac spoofing in detail, how it is used, and how you can protect yourself against it. Uncover the secrets of mac spoofing: learn how network hackers manipulate device identities, protect your system, and defend against cyber threats. Learn how a mac spoofing attack works and allows unauthorized access to hackers by mimicking trusted devices. learn how you can prevent it. During the pentest, it is crucial to understand how mac spoofing works in order to effectively secure against it. by spoofing a mac address, an attacker can deceive the network into thinking their device is a trusted one, making it easier to launch further attacks. Among the various techniques used to breach network security, mac spoofing stands out due to its simplicity and effectiveness. this article provides an in depth exploration of mac spoofing, covering its definition, methods, applications, detection, and preventive measures. Macchanger is a versatile and essential tool for managing mac addresses in cybersecurity. its ability to spoof, randomize, and restore mac addresses makes it indispensable for privacy, security testing, and network troubleshooting.
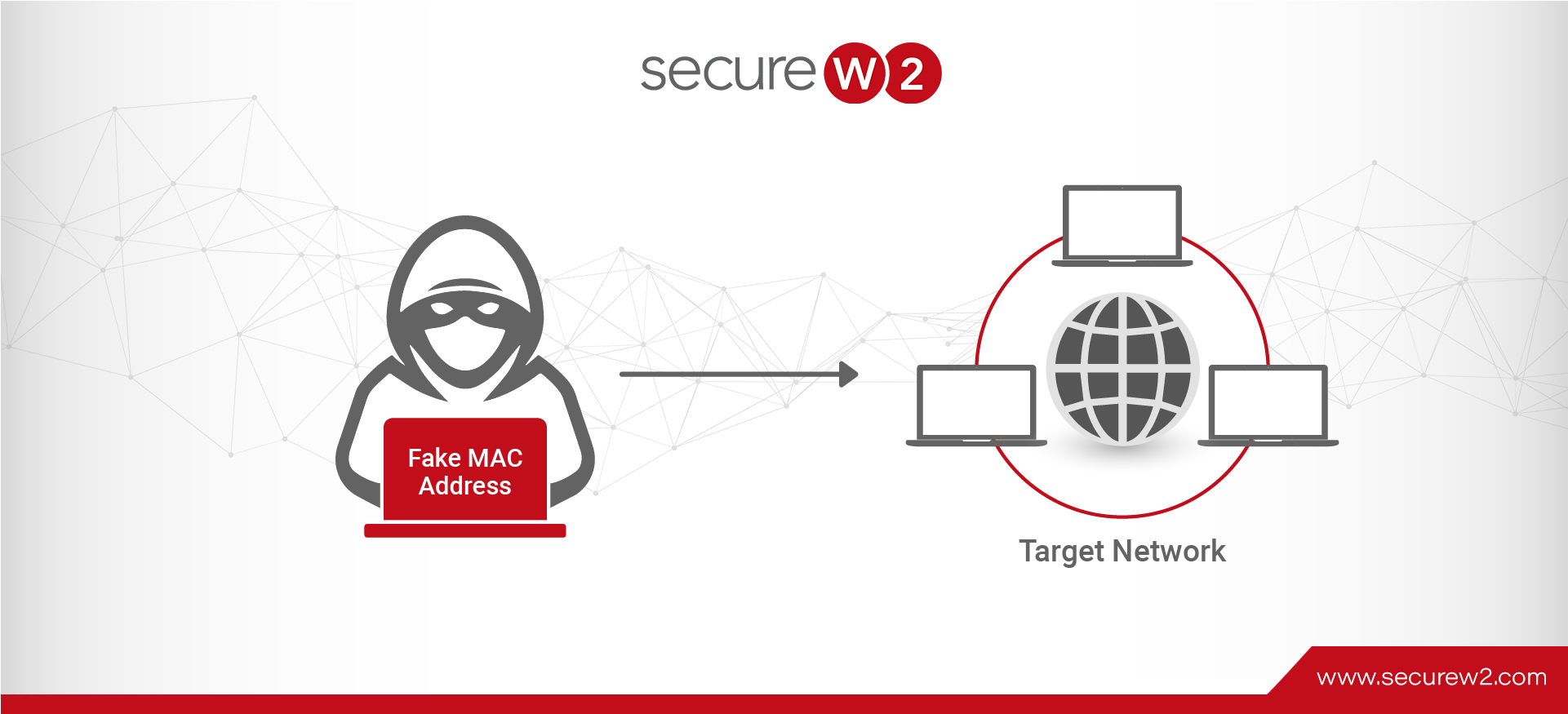
Mac Spoofing Attacks Explained A Technical Overview Learn how a mac spoofing attack works and allows unauthorized access to hackers by mimicking trusted devices. learn how you can prevent it. During the pentest, it is crucial to understand how mac spoofing works in order to effectively secure against it. by spoofing a mac address, an attacker can deceive the network into thinking their device is a trusted one, making it easier to launch further attacks. Among the various techniques used to breach network security, mac spoofing stands out due to its simplicity and effectiveness. this article provides an in depth exploration of mac spoofing, covering its definition, methods, applications, detection, and preventive measures. Macchanger is a versatile and essential tool for managing mac addresses in cybersecurity. its ability to spoof, randomize, and restore mac addresses makes it indispensable for privacy, security testing, and network troubleshooting.
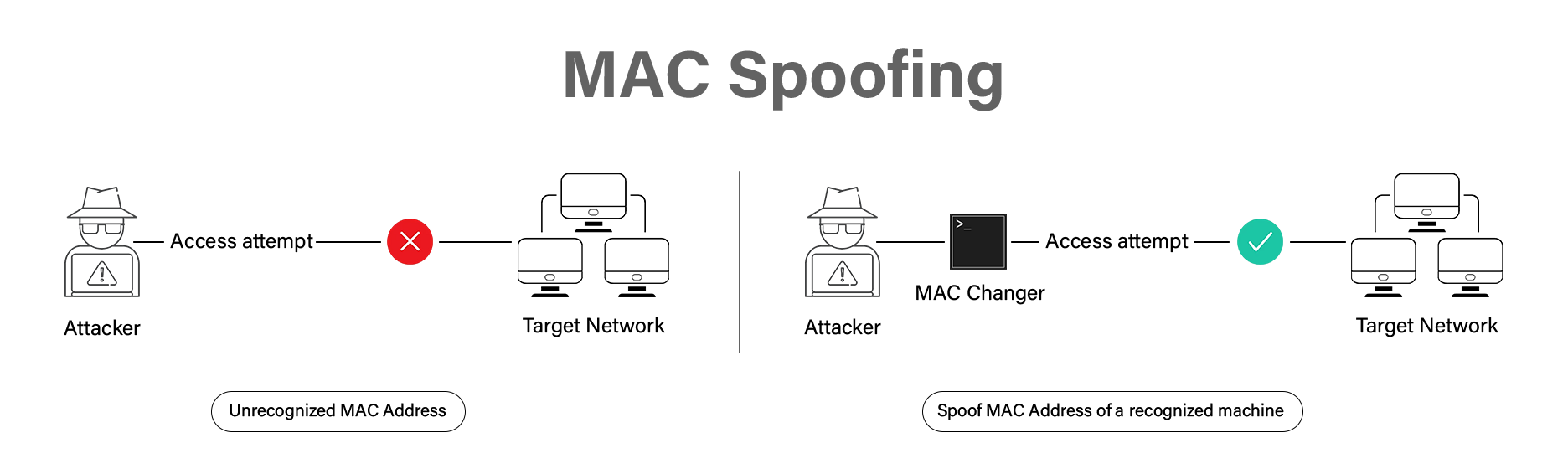
Mac Spoofing Attacks Explained A Technical Overview Among the various techniques used to breach network security, mac spoofing stands out due to its simplicity and effectiveness. this article provides an in depth exploration of mac spoofing, covering its definition, methods, applications, detection, and preventive measures. Macchanger is a versatile and essential tool for managing mac addresses in cybersecurity. its ability to spoof, randomize, and restore mac addresses makes it indispensable for privacy, security testing, and network troubleshooting.
Comments are closed.