Mac Address Spoofing 100 Working
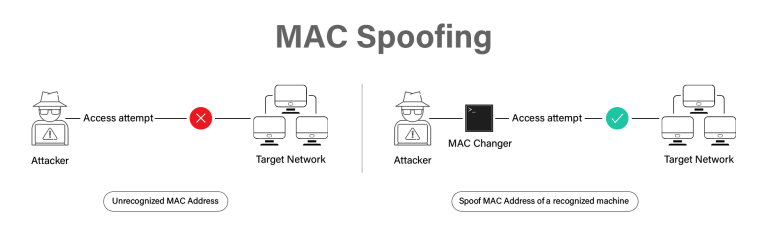
Mac Spoofing Attacks Explained A Technical Overview A cross platform mac address spoofing tool with both gui and command line interfaces. change your network adapter's mac address for privacy, testing, or network troubleshooting purposes. This comprehensive blog breaks down what mac spoofing is, how it works, why it’s used, and how to protect against it —including real world examples and the latest mitigation techniques in 2026.
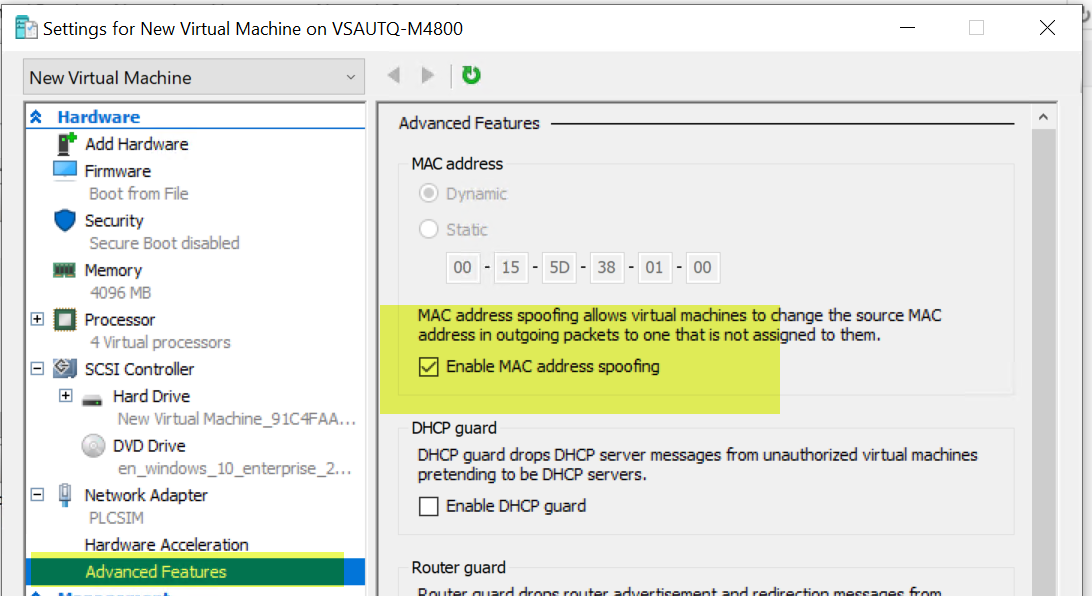
Enable Mac Address Spoofing Microsoft Q A Learn what mac address spoofing (also called mac address cloning) is, why it’s used, and when it’s helpful. explore real world examples, risks, and differences from imei spoofing. includes step by step instructions for peplink, teltonika, and sierra wireless routers. Is an invisible intruder bypassing your firewall? learn how to detect mac address spoofing using wireshark, python, and enterprise switch logs. Media access control (mac) address spoofing is a fundamental technique in both offensive security operations and defensive network hardening. Mac spoofing is a technique for changing a factory assigned media access control (mac) address of a network interface on a networked device. the mac address that is hard coded on a network interface controller (nic) cannot be changed. however, many drivers allow the mac address to be changed.
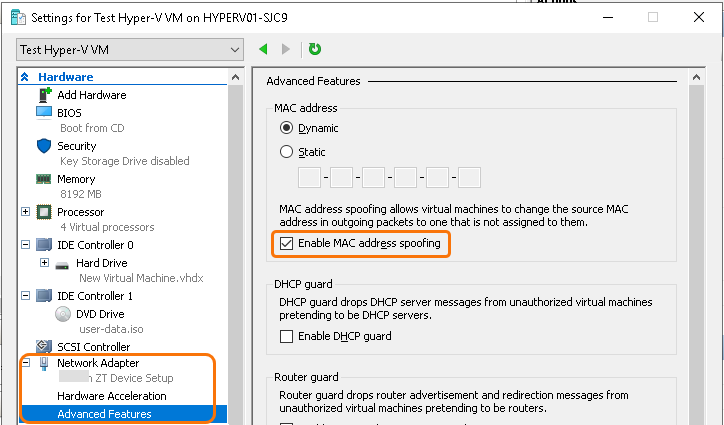
Hardware Setting To Enable Mac Address Spoofing Media access control (mac) address spoofing is a fundamental technique in both offensive security operations and defensive network hardening. Mac spoofing is a technique for changing a factory assigned media access control (mac) address of a network interface on a networked device. the mac address that is hard coded on a network interface controller (nic) cannot be changed. however, many drivers allow the mac address to be changed. Learn to bypass wi fi mac address filtering. this lab covers identifying filtered networks, finding client macs with airodump ng, and spoofing with macchanger. A mac address is intended to be permanent for a device, but you can spoof (change) it to a random address or to a specific device’s mac address to impersonate that device. Each nic has a mac address assigned by the manufacturer, which uniquely identifies the device on a network. by changing the mac address, users can hide their actual identity on the network, enabling anonymous operation or bypassing network restrictions. Mac address spoofing can jeopardize your network’s security. learn how hackers use this technique and discover the steps you can take to protect your network.
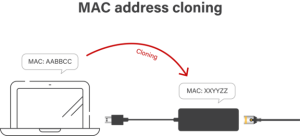
Mac Spoofing Attacks Explained A Technical Overview Learn to bypass wi fi mac address filtering. this lab covers identifying filtered networks, finding client macs with airodump ng, and spoofing with macchanger. A mac address is intended to be permanent for a device, but you can spoof (change) it to a random address or to a specific device’s mac address to impersonate that device. Each nic has a mac address assigned by the manufacturer, which uniquely identifies the device on a network. by changing the mac address, users can hide their actual identity on the network, enabling anonymous operation or bypassing network restrictions. Mac address spoofing can jeopardize your network’s security. learn how hackers use this technique and discover the steps you can take to protect your network.
Comments are closed.