M5 Ic Mercury Security
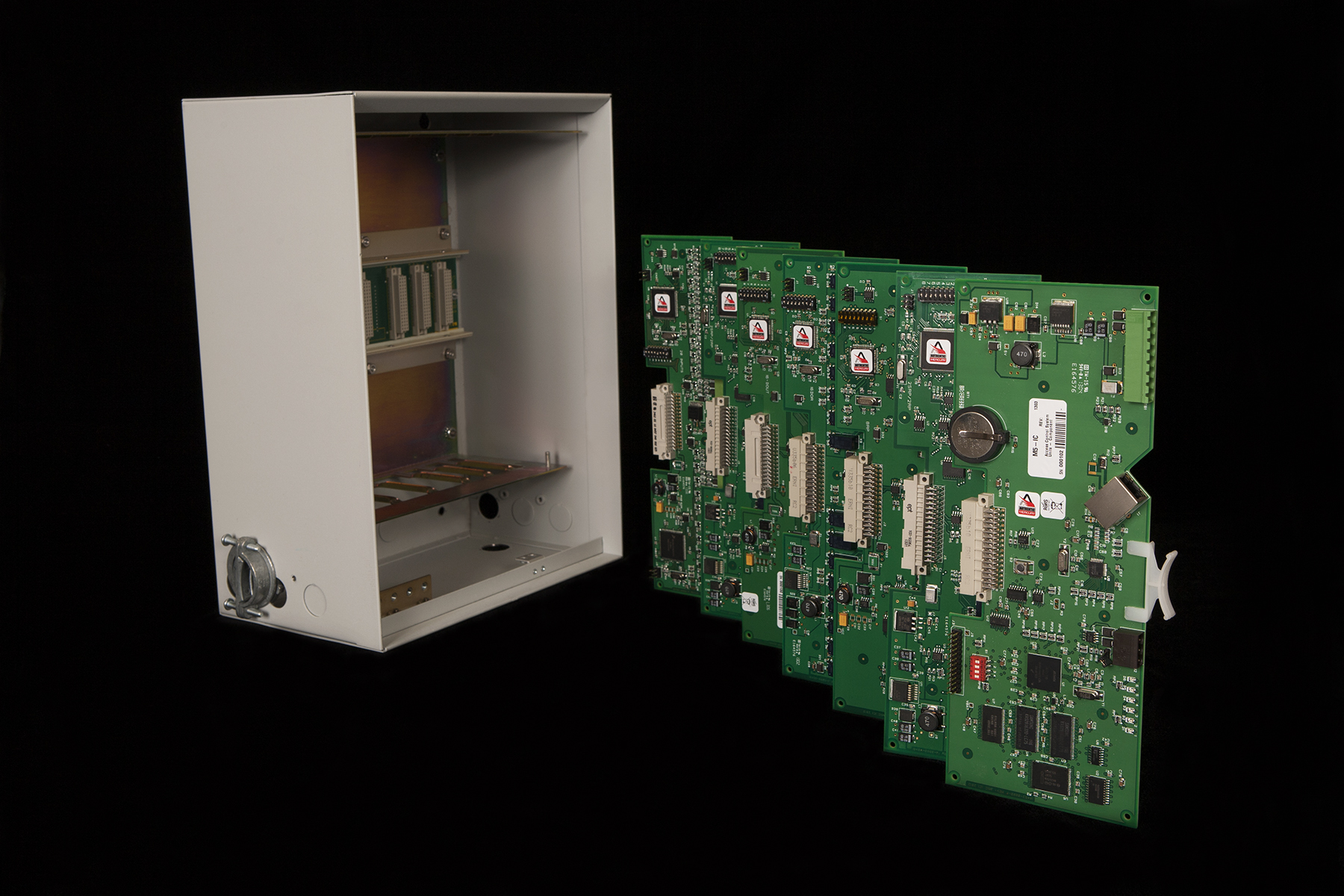
M5 Ic Mercury Security Follow us to stay up to date on the latest in security and access control systems—and all things mercury. M5 ic is an intelligent control device for the replacement of the casi px, pxn and pxnplus cpu controller. as with the entire mercury m5 bridge family of controllers, the m5 ic is built with a matching form factor to the casi micro5 line of access control hard ware allowing a fast “screwdriverless” change over and easy migration of a casi.
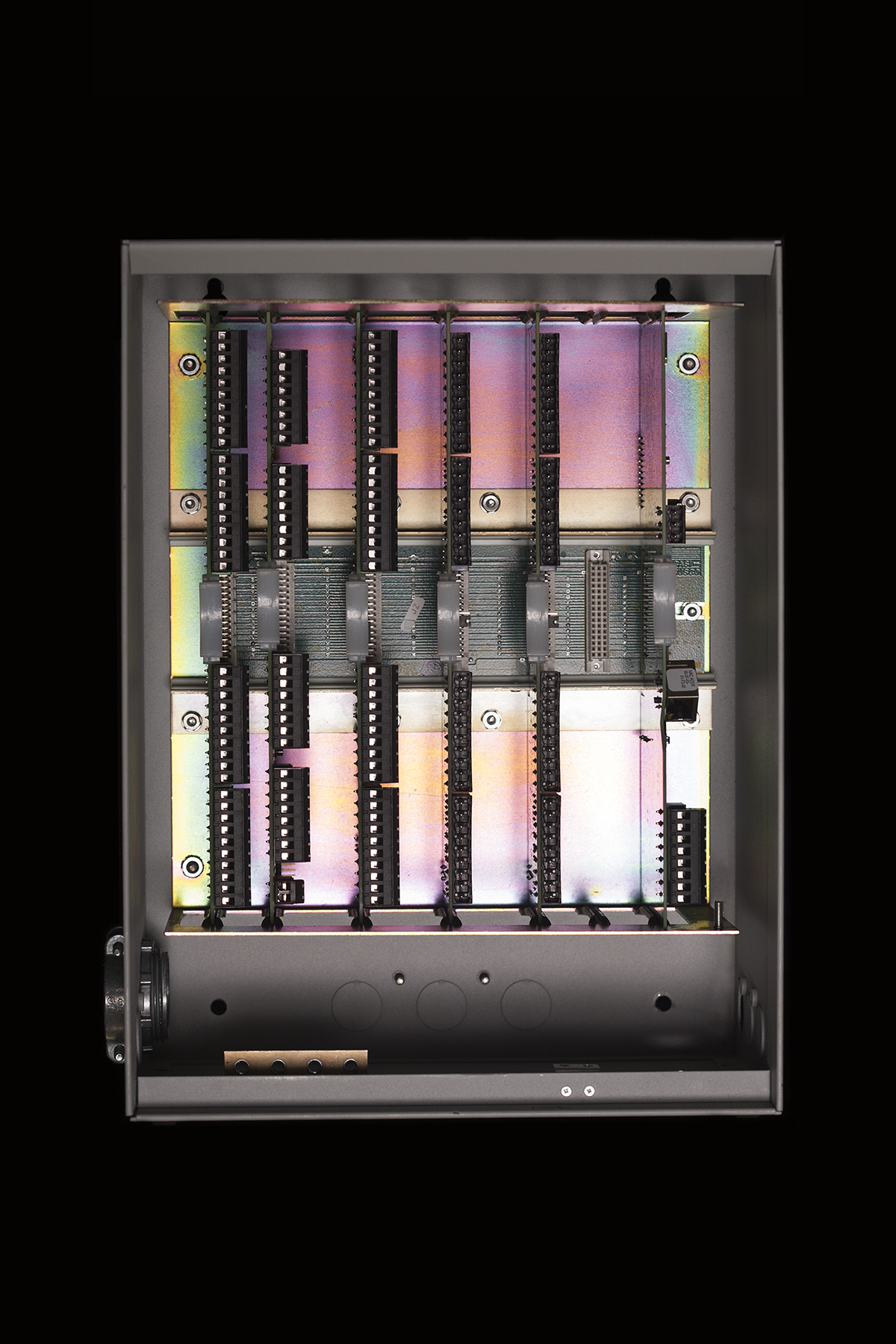
M5 Ic Mercury Security Mercury’s m5 ic controller board (ic board) for the micro5 (m5 enclosure) is part of mercury security’s bridging hardware technology and serves as an intelligent controller providing decision making, event reporting, and database. Get in depth information on mercury security m5 ic access control controllers including detailed technical specifications. View and download mercury security m5 2k installations and specifications online. four reader interface board. m5 2k computer hardware pdf manual download. Mercury security m5 ic single controller supports management of up to 64 readers.

M5 Ic Mercury Security View and download mercury security m5 2k installations and specifications online. four reader interface board. m5 2k computer hardware pdf manual download. Mercury security m5 ic single controller supports management of up to 64 readers. The m5 ic possesses all the firmware functions available in the authentic mercury controller platform and ensures every end user complete compatibility to all forthcoming system functionality mercury security has to offer. Le m5 ic possède toutes les fonctions du micrologiciel disponibles sur la plateforme de contrôleur authentic mercury et garantit à chaque utilisateur final une compatibilité totale avec toutes les fonctionnalités futures que mercury security propose. The m5 ic possesses all the firmware functions available in the authentic mercury controller platform and ensures every end user complete compatibility to all forthcoming system functionality mercury security has to offer. The m5 ic is an integral component in the hid mercury m5 bridge family approach to migrate any micro5 hardware legacy to the flexible, feature rich hid mercury access hardware.
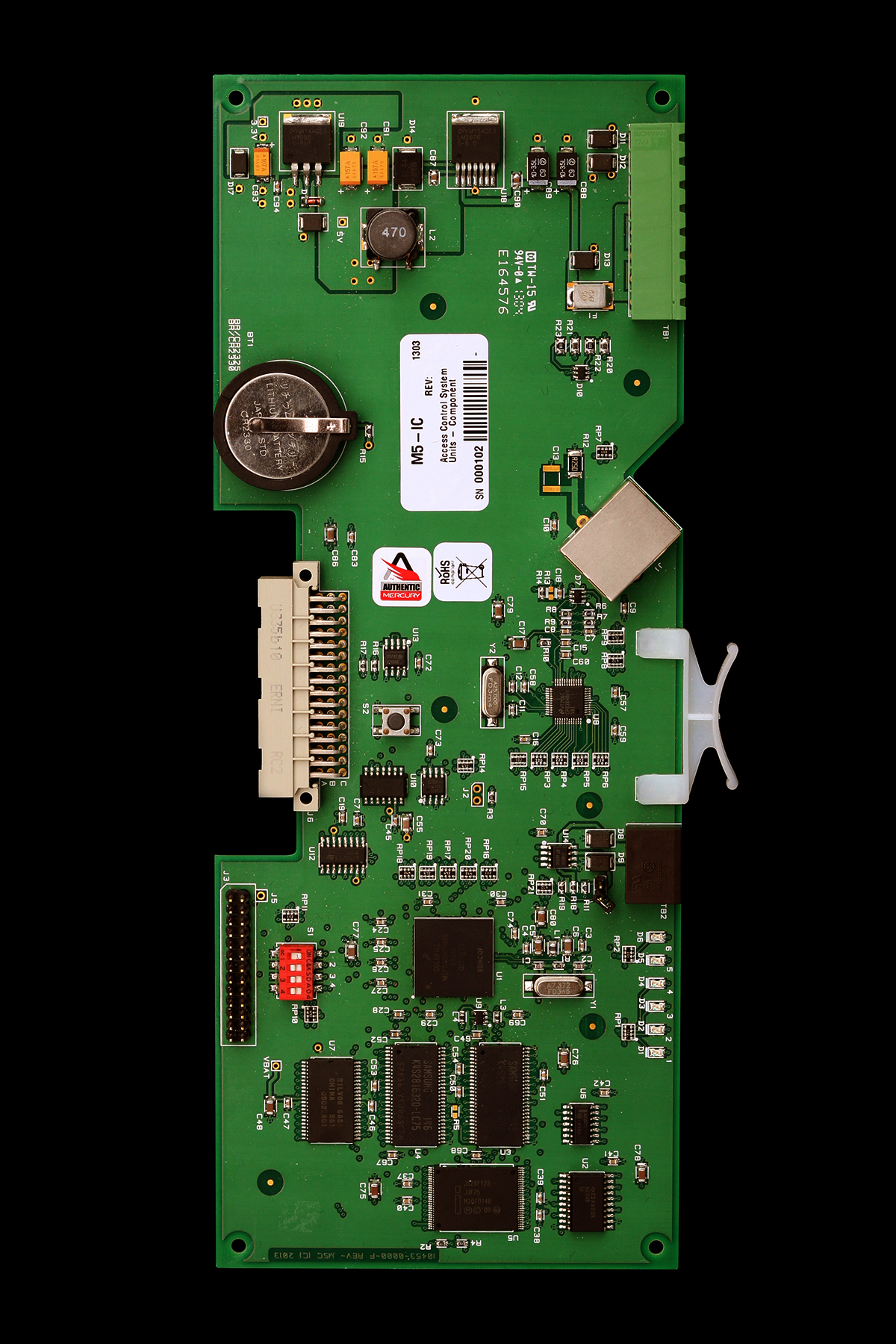
M5 Ic Mercury Security The m5 ic possesses all the firmware functions available in the authentic mercury controller platform and ensures every end user complete compatibility to all forthcoming system functionality mercury security has to offer. Le m5 ic possède toutes les fonctions du micrologiciel disponibles sur la plateforme de contrôleur authentic mercury et garantit à chaque utilisateur final une compatibilité totale avec toutes les fonctionnalités futures que mercury security propose. The m5 ic possesses all the firmware functions available in the authentic mercury controller platform and ensures every end user complete compatibility to all forthcoming system functionality mercury security has to offer. The m5 ic is an integral component in the hid mercury m5 bridge family approach to migrate any micro5 hardware legacy to the flexible, feature rich hid mercury access hardware.

Mercury Security Resources Downloads Documents Technical Support The m5 ic possesses all the firmware functions available in the authentic mercury controller platform and ensures every end user complete compatibility to all forthcoming system functionality mercury security has to offer. The m5 ic is an integral component in the hid mercury m5 bridge family approach to migrate any micro5 hardware legacy to the flexible, feature rich hid mercury access hardware.

Mercury Security Resources Downloads Documents Technical Support
Comments are closed.