Linux Ssh Authentication
Configure Ssh Key Based Authentication On Linux Ssh authentication uses a public–private key pair. the private key remains on the client machine and must be kept secret, while the public key is placed on the server in the ~ .ssh authorized keys file to enable authentication. ssh keys are generated using the ssh keygen utility. In this article, we looked at ssh authentication methods, ways for servers to require them in order, and for clients to prefer some to others. in conclusion, knowing how to order authentication methods introduces another layer of security to the golden standard, which is ssh.
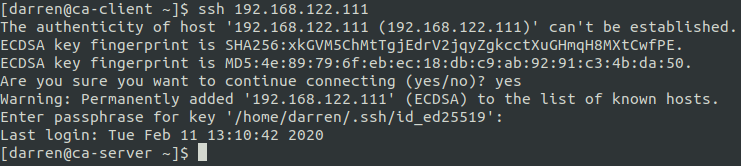
Ssh Key Based Authentication Explains how to set up ssh keys for public key authentication on a linux, freebsd, openbsd, os x macos or unix based systems. In this guide, we’ll explore how to create ssh keys, perform an ssh key exchange, and configure the sshd config file for key based login. whether you’re a system administrator or a linux enthusiast, this deep dive will equip you with everything you need to master ssh key authentication. Public key authentication is the best way to secure ssh connections. learn how to generate a key pair and securely access remote servers. Think you know ssh? think again. unlock powerful ssh tips, secure your logins with key based auth, fix frustrating errors, and level up your linux skills with this hands on guide.

Authentication Methods And Their Order In Ssh Baeldung On Linux Public key authentication is the best way to secure ssh connections. learn how to generate a key pair and securely access remote servers. Think you know ssh? think again. unlock powerful ssh tips, secure your logins with key based auth, fix frustrating errors, and level up your linux skills with this hands on guide. Implementing ssh key based authentication is a critical step in securing your linux and unix systems. by following this comprehensive guide, you’ve taken a significant step toward protecting your servers from unauthorized access and potential breaches. Traditional password logins and even regular ssh keys are starting to feel outdated. a stronger and more scalable option is now available: ssh certificate based authentication. in this guide, we’ll walk through how to use ssh certificates on ubuntu. The ssh protocol (aka secure shell) is used to establish secure and reliable communications between two hosts. it supports different ssh authentication methods and uses strong encryption to protect exchanged data. Ssh public key authentication allows secure remote access between machines without using passwords. this guide will start you off by generating key pairs with ssh keygen, then build your expertise in applying and managing ssh keys like a seasoned professional.

Linux Ssh Authentication Implementing ssh key based authentication is a critical step in securing your linux and unix systems. by following this comprehensive guide, you’ve taken a significant step toward protecting your servers from unauthorized access and potential breaches. Traditional password logins and even regular ssh keys are starting to feel outdated. a stronger and more scalable option is now available: ssh certificate based authentication. in this guide, we’ll walk through how to use ssh certificates on ubuntu. The ssh protocol (aka secure shell) is used to establish secure and reliable communications between two hosts. it supports different ssh authentication methods and uses strong encryption to protect exchanged data. Ssh public key authentication allows secure remote access between machines without using passwords. this guide will start you off by generating key pairs with ssh keygen, then build your expertise in applying and managing ssh keys like a seasoned professional.
Ssh Key Authentication To Linux Knowledge Sharing Tech The ssh protocol (aka secure shell) is used to establish secure and reliable communications between two hosts. it supports different ssh authentication methods and uses strong encryption to protect exchanged data. Ssh public key authentication allows secure remote access between machines without using passwords. this guide will start you off by generating key pairs with ssh keygen, then build your expertise in applying and managing ssh keys like a seasoned professional.
Fix Ssh Certificate Authentication In Linux Opentechtips
Comments are closed.