Linux Security Secure Shell Ssh Introduction Evilsaint

Secure Shell Ssh Protocol Encryption Over Insecure Networks This article serves as an introduction to the secure shell (ssh) protocol for linux users. when you need to connect to linux servers remotely, ssh is the most commonly used method. Protect sensitive data and critical systems with secure and privileged access, complete visibility, and trusted communications across your organization.

Ssh Shell Secure Milolab I spend my time consuming four to six books a month on security, technololgy, psychology, learning and productivity. not to mention i am always doing a course or certificate!. This article serves as an introduction to the secure shell (ssh) protocol for linux users. when you need to connect to linux servers remotely, ssh is the most commonly used method. Here we’ll describe some of the configuration settings possible with the openssh server application and how to change them on your ubuntu system. openssh is a freely available version of the secure shell (ssh) protocol family of tools. traditional tools, such as telnet or rcp, are insecure and transmit the user’s password in cleartext when. Secure shell (ssh) is a core tool in a sysadmin's arsenal and provides a secure and encrypted connection and method of communication between a client user and a server.
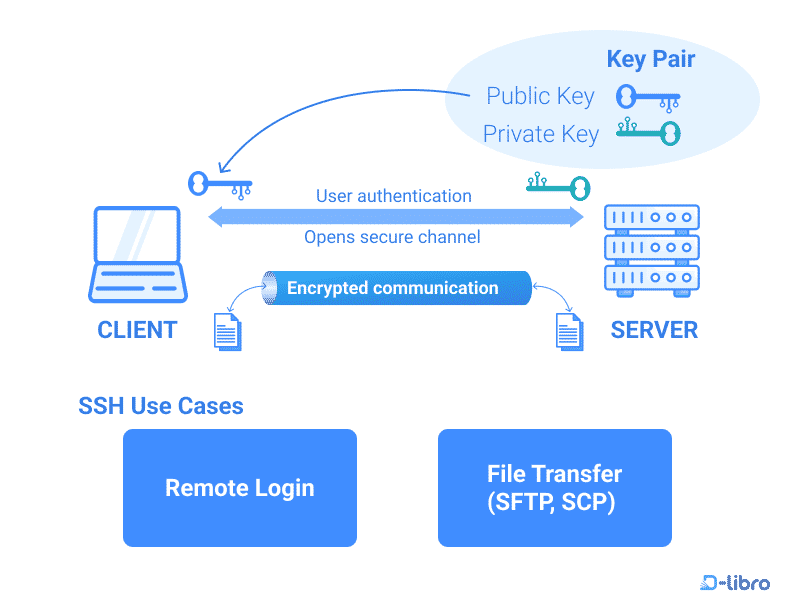
Introduction To Ssh In Linux Topic Here we’ll describe some of the configuration settings possible with the openssh server application and how to change them on your ubuntu system. openssh is a freely available version of the secure shell (ssh) protocol family of tools. traditional tools, such as telnet or rcp, are insecure and transmit the user’s password in cleartext when. Secure shell (ssh) is a core tool in a sysadmin's arsenal and provides a secure and encrypted connection and method of communication between a client user and a server. Ssh is a powerful and essential tool for linux users, providing secure remote access and file transfer capabilities. by understanding the fundamental concepts, mastering the usage methods, adopting common practices, and following best practices, you can use ssh effectively and securely. What is ssh? it is a set of standards and associated protocols to establish a secure channel between two computers. it provides mutual authentication, data confidentiality, and data integrity. originally, it was designed as a replacement of insecure applications like r commands (i.e., berkeley remote commands, e.g., rlogin, rsh, rcp). The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution. What linux is, an overview of common distributions, why developers use it, and how to connect to a remote server via ssh.

Linux Security Secure Shell Ssh Introduction Evilsaint Ssh is a powerful and essential tool for linux users, providing secure remote access and file transfer capabilities. by understanding the fundamental concepts, mastering the usage methods, adopting common practices, and following best practices, you can use ssh effectively and securely. What is ssh? it is a set of standards and associated protocols to establish a secure channel between two computers. it provides mutual authentication, data confidentiality, and data integrity. originally, it was designed as a replacement of insecure applications like r commands (i.e., berkeley remote commands, e.g., rlogin, rsh, rcp). The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution. What linux is, an overview of common distributions, why developers use it, and how to connect to a remote server via ssh.

Linux Security Secure Shell Ssh Introduction Evilsaint The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution. What linux is, an overview of common distributions, why developers use it, and how to connect to a remote server via ssh.

Ssh Protocol Secure Shell Dataflair
Comments are closed.